John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
Researcher Wladimir Palant spent months tearing apart VStarcam camera firmware. What he found wasn’t a bug. It was a pattern.
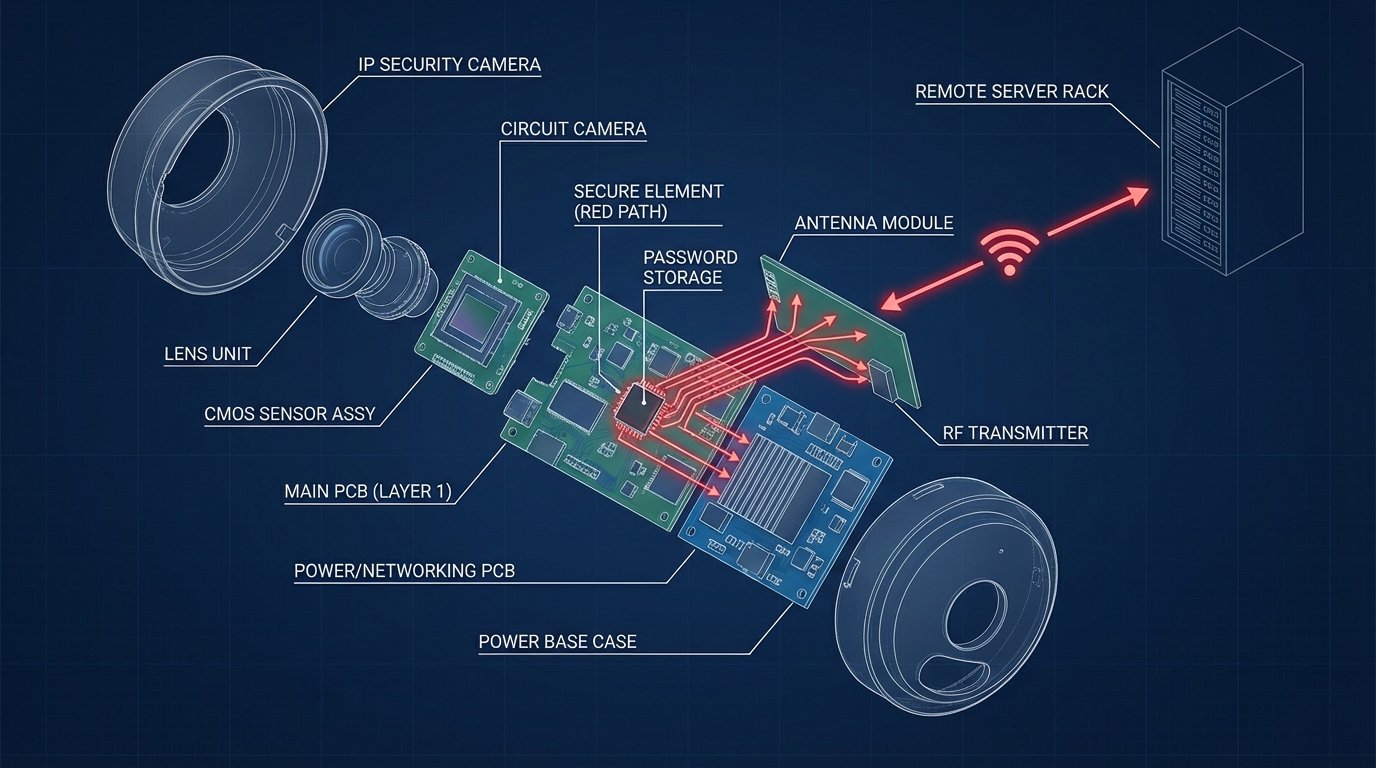
Over four years, VStarcam systematically added mechanisms to leak your access password back to the manufacturer. 2020: password leaks via logging. 2021: log uploads to VStarcam servers. 2022: unauthenticated access to those logs. 2024: a covert backdoor that directly leaks passwords. Each step builds on the last. None of this is accidental.
It gets worse. These cameras use the PPPP protocol, which punches through your router’s NAT and maintains a persistent connection to vendor infrastructure. Your firewall doesn’t matter. The “encryption” protecting that connection uses a four-byte effective key. Firmware updates arrive over plain HTTP. There’s also an authentication bypass in the web UI and an open telnet port with hardcoded credentials. On a product marketed as a security camera.
You might not think you own a VStarcam. Check again. The same hardware ships under Besder, MVPower, AOMG, and OUSKI. If your camera uses Eye4, EyeCloud, PnPCam, VeePai, or about a dozen other apps, it’s VStarcam hardware.
Palant attempted coordinated disclosure. Three months of silence. No patch, no statement, no response. If you own one of these, consider replacing it with something that offers local storage and doesn’t insist on phoning home through your firewall. If the camera connects to the internet regardless of your settings, it’s not your camera. It’s someone else’s camera in your house.
Read Palant’s full findings on VStarcam’s deliberate backdoor engineering