John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
Mostly security stuff...
Make sure you check out my main blog at https://gnerdsec.com/blog

Machine-Speed Extortion: How Spider Groups and RMM Abuse Are Owning the Cloud
Cordial Spider, Snarky Spider, and VENOMOUS#HELPER aren't breaking into cloud environments. They're walking in through the help desk.
Read More
The Storm Is Coming: Deciphering the UK NCSC's Rare Warning
The UK's NCSC issued a forward-looking threat warning this week. No specific CVE. No named actor. Just: get ready. Here's what that actually means.
Read More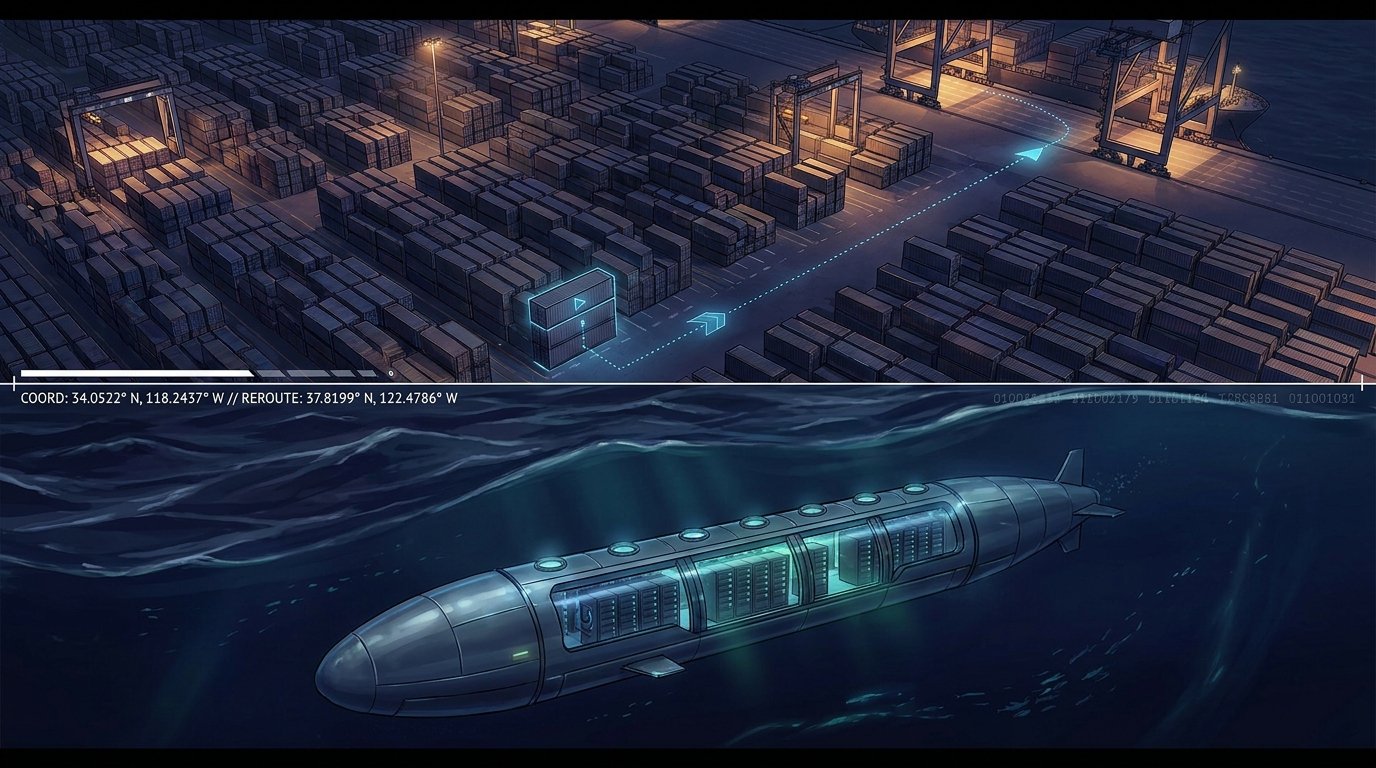
The Digital Hijack: Hacking Is No Longer Just About Data
The FBI is warning about credential theft that ends with stolen trucks. A $1 billion startup wants to put data centers at the bottom of the ocean. The physical and digital worlds are one ecosystem now.
Read More
The Price of Malice: $700 Million Seizures and Sentenced Professionals
A coordinated Dubai-US operation seized $701 million and arrested 276 people. Two American cybersecurity pros got four years each. The legal nets are widening.
Read More
The Auth Layer Is Leaking: Why cPanel, GitHub, and Microsoft Are All Scrambling
A single week brought critical auth bypasses in cPanel, GitHub Enterprise, Microsoft Entra ID, and a zero-click NTLM re-patch. This isn't a run of bad luck.
Read More
The Analog Resistance: Why Markers and Moustaches Beat AI Security
UK kids are drawing fake moustaches to bypass facial age checks. Nearly 40% of new podcasts are AI-generated slop. AI vibe checking is failing everywhere.
Read More