John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
CISA just dropped Emergency Directive 26-03 on a Monday morning. That usually means something is very wrong. This time, the agency is commanding federal teams to inventory and patch their Cisco SD-WAN systems immediately.
Here is the kicker: we now have evidence that a sophisticated shadow campaign has been exploiting these systems since at least 2023.
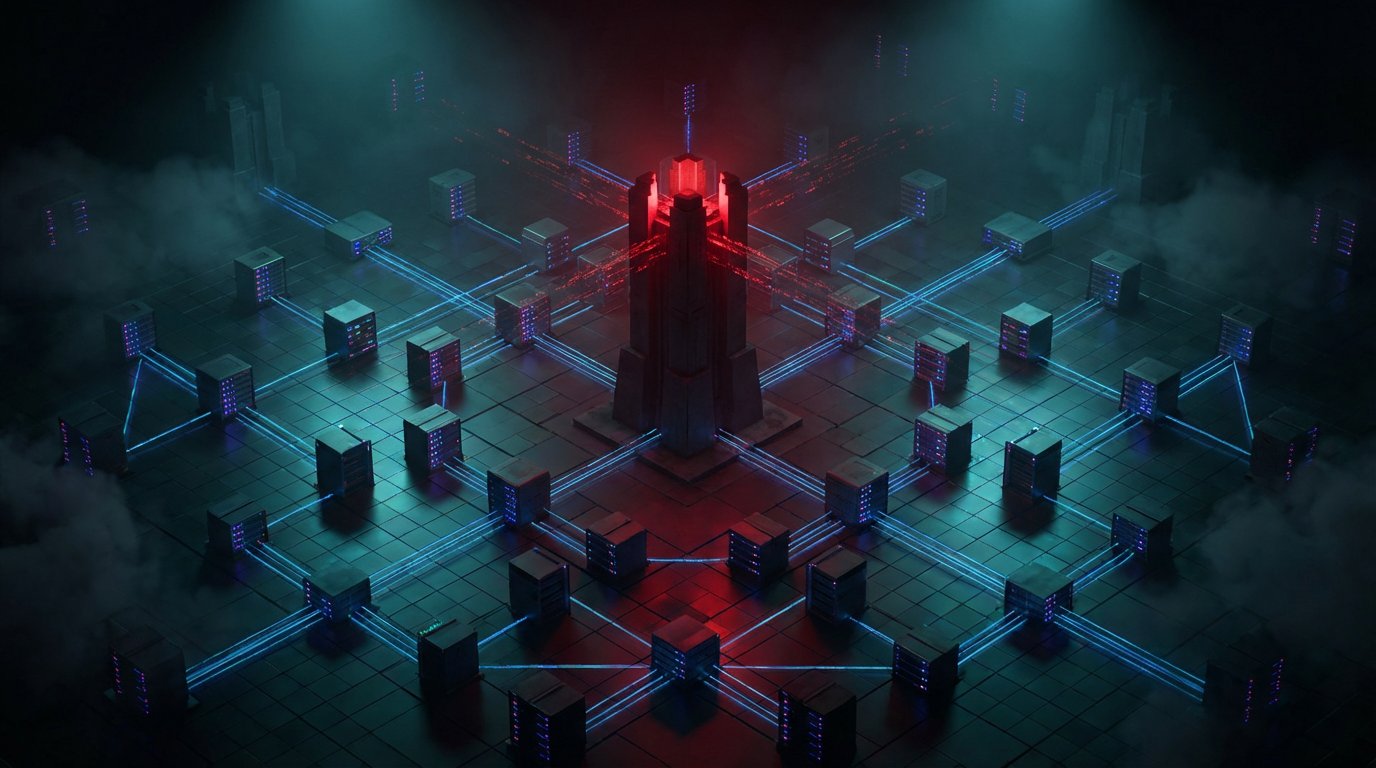
SD-WAN is essentially the central switchboard for the modern enterprise. It handles the traffic flow between your branch offices, the data center, and the cloud. Hijacking the orchestration plane is not just a server compromise. It is taking total control over the logical pathways of your entire organization’s data.
The vulnerabilities are nasty. We are talking about an authentication bypass and a path traversal that grant root privilege escalation to unauthenticated remote attackers.
Centralization was supposed to make networking easier. It did. But it also created a single, high-value target. If an attacker controls your SD-WAN, they can intercept your traffic, redirect your data through their own nodes, and completely nullify your network segmentation policies.
CISA is demanding a full inventory and remediation by April 30. For the private sector, the lesson is clear. Do not assume your network orchestration is a neutral utility. It is an active front.
You need to locate every instance of this hardware, pull snapshots for forensics, and hunt for signs of privilege hijacking. If CISA is issuing an emergency order with context dating back to 2023, the threat is mature, persistent, and already in the building.
Check out the full breakdown of Phase 1 through 4 requirements.