John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
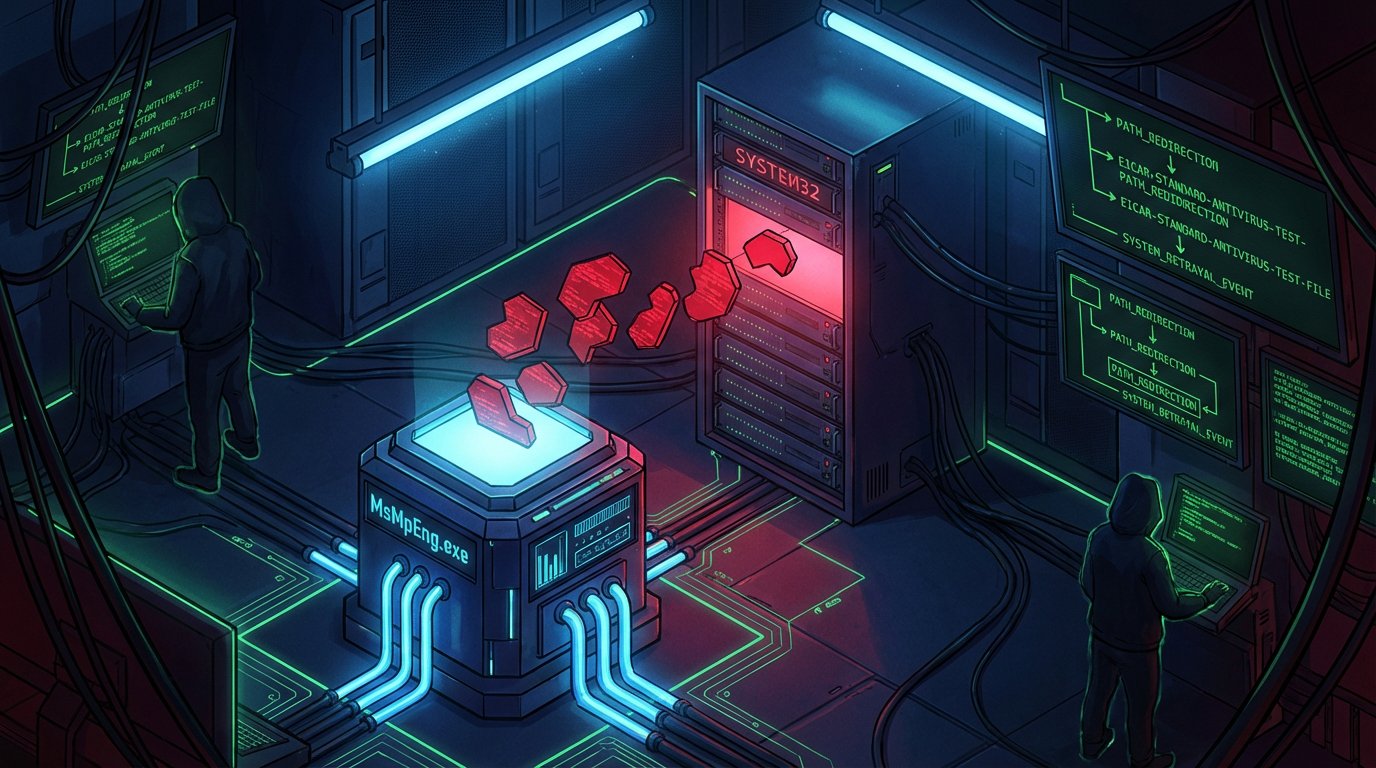
Windows Defender is supposed to be the most trusted service on your machine. But a researcher going by Nightmare-Eclipse is currently proving that trust is a liability. Over the last few weeks, three different zero-days have dropped, each one exploiting the basic fact that Defender has high privileges and trusts the paths it is given.
The most poetic one is RedSun. It uses an EICAR test file to bait the engine into a scan, then redirects the output to overwrite system binaries. Defender effectively writes the malware for you. Then there is UnDefend, which lets a standard user permanently jam Defender’s update pipeline. Your dashboard stays green, but your signatures stay stuck in the past.
Microsoft’s surgical patches are not hitting the mark because the problem is architectural. If you are relying on that little green light in your taskbar to tell you your system is safe, you might want to start checking your file timestamps manually. It is about to get a whole lot funnier.
Check out the deep dive on why the Defender trust model is inherently broken.