John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
If you use OpenClaw to run your AI agents, you need to update right now. A new vulnerability, CVE-2026-41296, allows for a full escape from the sandbox.
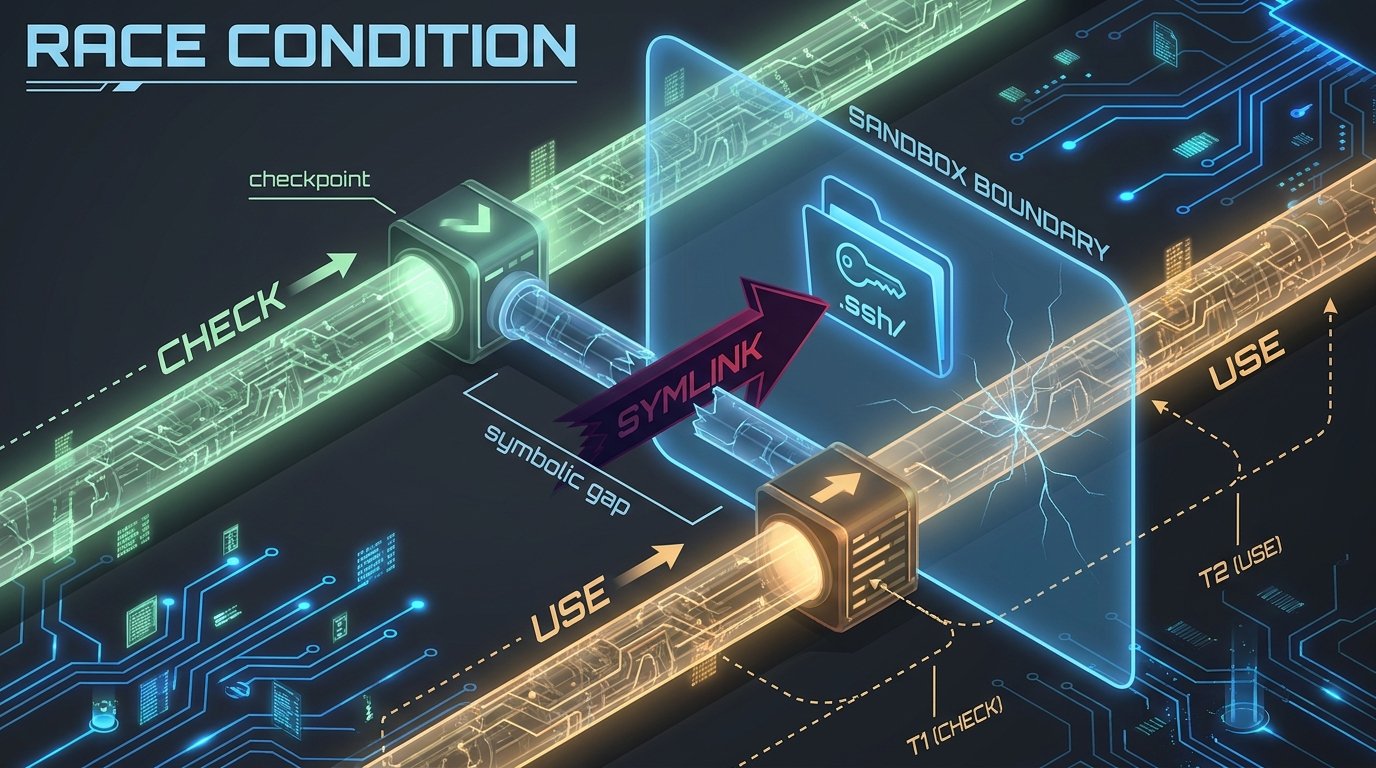
This is a classic race condition. The system checks to see if a file is safe, but there is a tiny window between that check and the actual read. An attacker can win that race by swapping a safe file for a malicious symlink. Before the system knows what hit it, your private SSH keys or environment secrets are being read by an unauthorized actor.
We talked about a separate OpenClaw bug earlier this month, but this one is much worse. It breaks the fundamental security promise of the platform. Version 2026.3.31 closes the window for good.
Do not wait. Update your instance today and double check what your agent has access to. The sandbox is only a boundary if the fix is installed.
Read the technical breakdown and get the patch instructions for the OpenClaw sandbox escape