John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
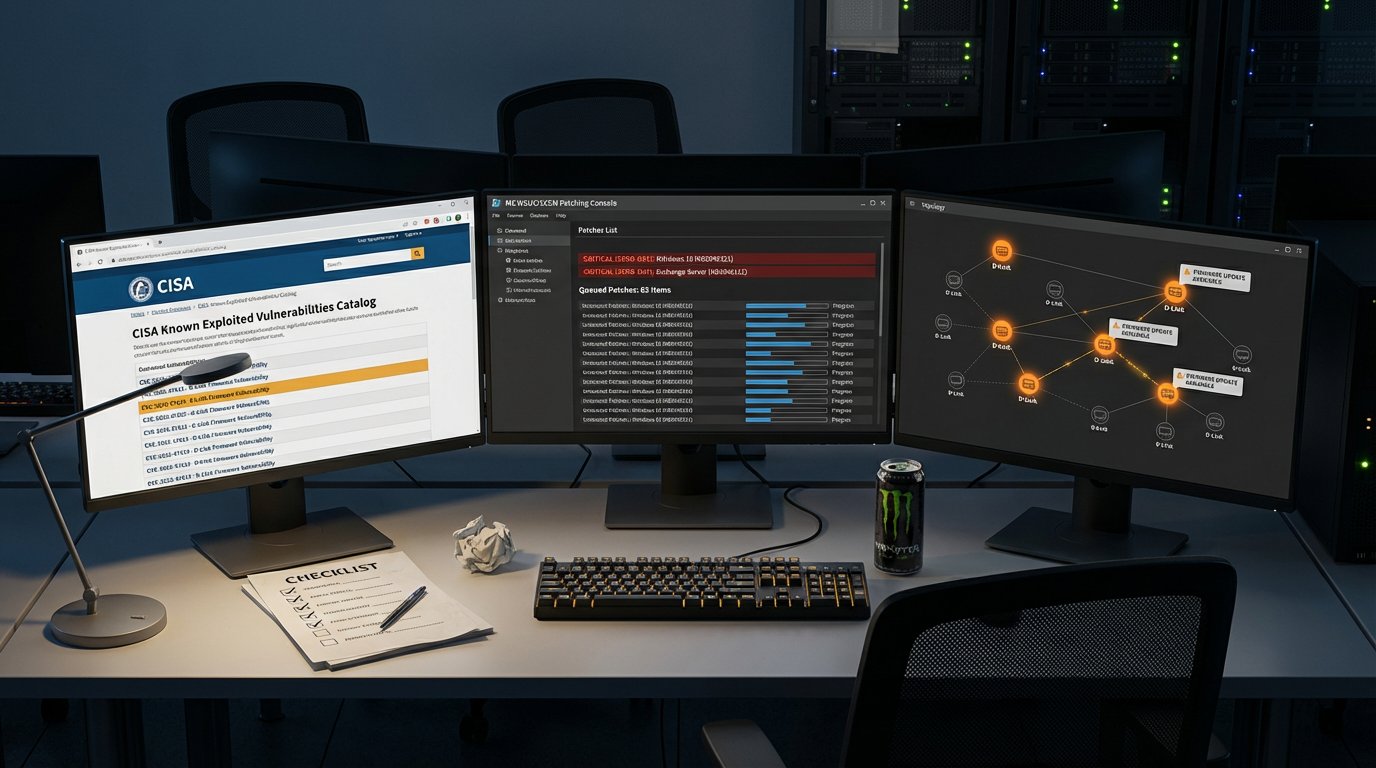
Three separate vulnerability disclosures this week, each hitting a different part of the stack. Here’s what needs patching.
Wing FTP Server: Stop What You’re Doing and Patch
CISA added CVE-2025-47813 in Wing FTP Server to the Known Exploited Vulnerabilities catalog. Translation: this bug is being used in real attacks right now.
It’s classified as an information disclosure flaw, which sounds tame. It isn’t. It’s being chained with other techniques to achieve remote code execution. Security teams should know this pattern by now: info disclosure bugs that leak paths, credentials, or internal state get stacked with injection or auth bypass flaws to build a full attack chain. The individual severity score can be misleading.
Wing FTP is one of those enterprise file transfer products that sits in the infrastructure doing its job and never generates support tickets. That invisibility is the risk. File transfer servers are a recurring target for ransomware groups and initial access brokers because they hold sensitive data and sit in network positions with broad connectivity.
Patch first. Audit your file transfer infrastructure second.
March Patch Tuesday: 82 CVEs, Two Zero-Days
Microsoft’s March 2026 Patch Tuesday covered 82 CVEs. Eight rated Critical. Two publicly disclosed before the patch shipped.
Those two disclosed vulnerabilities are the priority. “Publicly disclosed” means the details were available to attackers before Microsoft had a fix ready. Assume someone is testing them.
Prioritization for this cycle:
- The two zero-days. Known, details public, exploitation status uncertain. Assume the worst.
- Critical CVEs. Especially anything touching Exchange, Active Directory, or Hyper-V. High-value targets that are commonly exposed.
- Everything else by exposure. Internet-facing before internal. High-privilege before low-privilege.
82 CVEs is a lot but within normal range for March. The two zero-days make this cycle more urgent than average.
D-Link: Unauthenticated RCE via DNS Config
CVE-2026-0625 is an unauthenticated remote code execution bug in D-Link devices. Command injection through the dnscfg.cgi endpoint. Send a crafted request, the device doesn’t sanitize input, your payload runs as a system command. No login required.
Caveat: This CVE hasn’t been confirmed in the National Vulnerability Database or via a D-Link advisory yet. We’re including it because unauthenticated RCE in consumer and SMB networking gear is consistently real and consistently exploited. But verify against NVD before acting.
If confirmed, exposure depends on whether the web management interface is reachable from the internet. Check if remote management is enabled. Check network segmentation. And remember that the Mirai botnet and its successors have automated exploitation of exactly these kinds of bugs for years. An unauth RCE in a DNS config endpoint is botnet recruitment material.
If you have D-Link gear: check if this CVE hits your model, disable remote management, apply any firmware updates, and replace anything end-of-life with no patch available.
The Bigger Picture
Enterprise file transfer software, the Microsoft ecosystem, consumer networking equipment. Three different parts of the stack, all needing patches in the same week. This is what the patching obligation actually looks like in practice. It’s not one big critical CVE that gets all the attention. It’s a steady stream across every layer, and falling behind on any of them gets measured in breaches.
Prioritize: KEV-listed bugs first. Zero-days second. Then everything else by CVSS, exposure, and business criticality. And do it again next week.