John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
Proton Mail is supposed to be the safe one. Swiss jurisdiction, zero-knowledge encryption, the go-to recommendation when someone asks which email won’t get them surveilled. And yet the FBI used Proton data to identify an anonymous Stop Cop City protestor.
Before you delete your account: Proton didn’t fail. Most people just misunderstand what encrypted email actually protects.
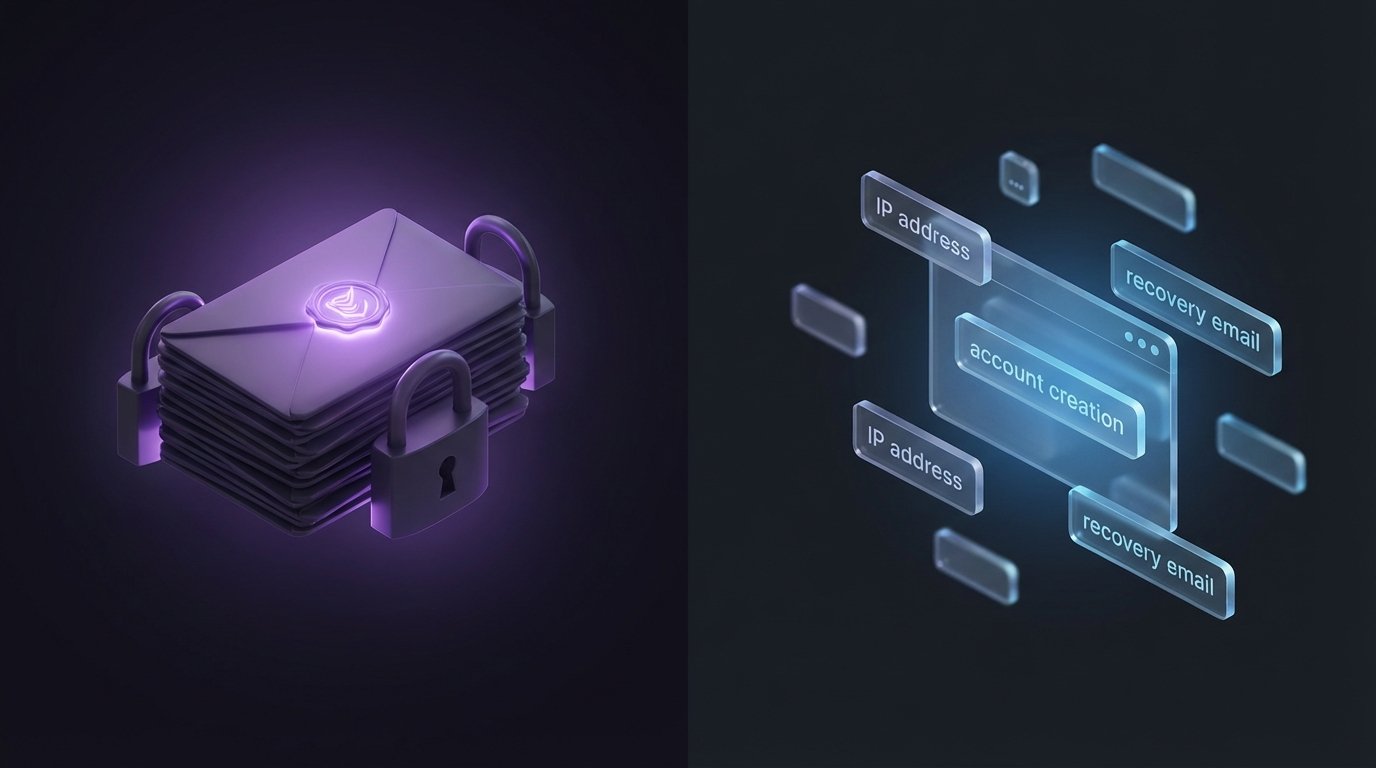
Nobody cracked anything. Swiss authorities issued a legal order, Proton complied, and what got handed over wasn’t email content. It was metadata: account creation details, payment information, a recovery email address. That was enough.
The content encryption is real. Proton genuinely cannot read your emails and can’t hand them over even if ordered to. But metadata – when the account was created, what IP address logged in, what recovery address was linked – that’s operational data every email provider collects. It goes over when the legal order comes.
“Encrypted” and “anonymous” are completely different claims. Most people treat them as the same thing. They’re not.
If anonymity is the actual goal, you need a lot more than an encrypted inbox. You need to create the account over Tor or a trustworthy VPN. Pay without a card. Link nothing to any real identity. Most people skip all of that, and then act surprised when the metadata trail leads back to them.
Proton Mail is still worth using for protecting email contents from corporate snooping, breaches, and routine surveillance. That’s a real benefit. But if the threat model is “government trying to find out who I am,” encrypted email alone doesn’t get you there.
The encryption worked. The metadata didn’t need to be cracked. Know what your tools actually protect.
Read the full breakdown of what Proton handed over and what it means for your threat model