John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
Security teams treat every asset like it’s roughly the same risk. Attackers don’t.
CISA just told organizations to harden endpoint-management systems after a real U.S. incident. Same week, researchers dropped pre-auth RCE chains for BMC FootPrints ITSM, and Eclypsium showed how cheap IP-KVM gear can become a full network takeover path. Cisco edge exploitation is still ongoing.
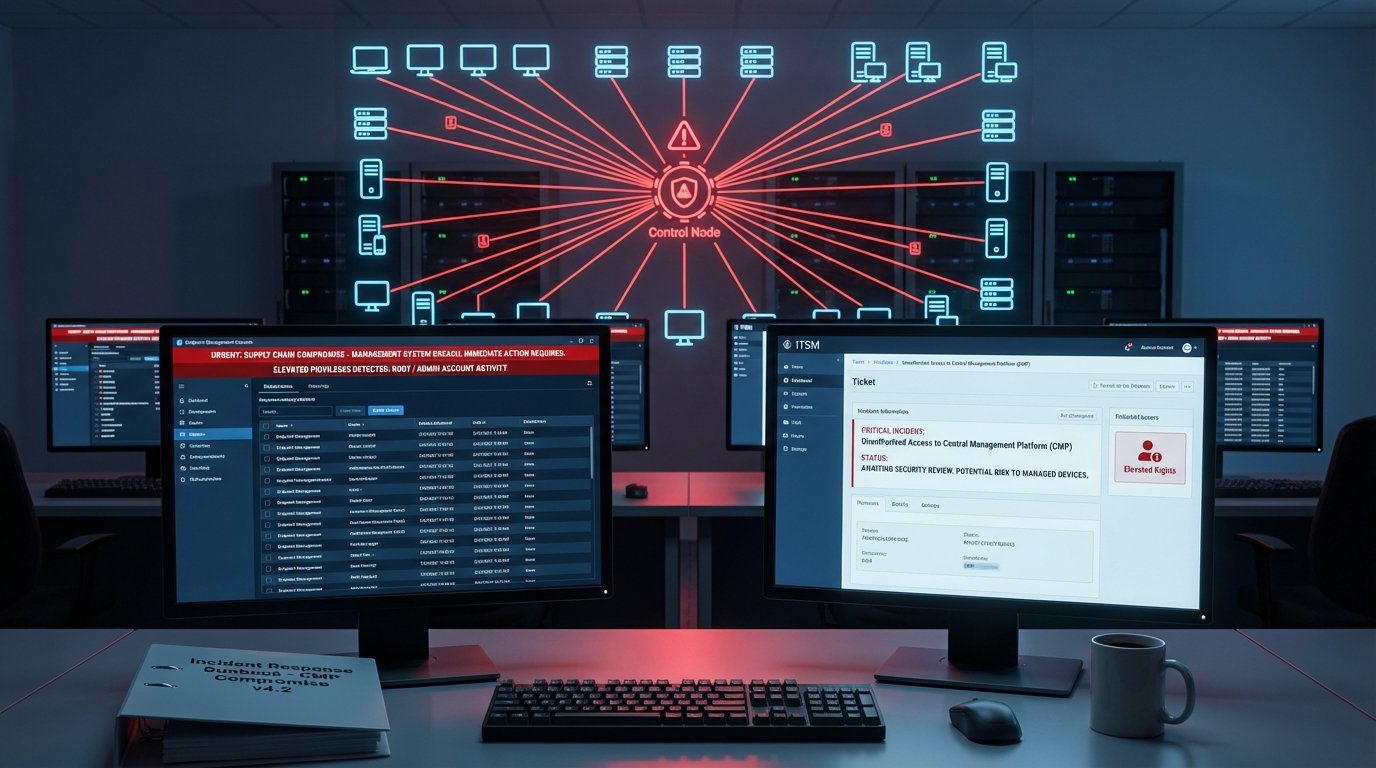
The pattern isn’t subtle: go after the systems that control other systems.
A vulnerable app server can hurt one workload. A compromised management stack can touch deployment, patching, policy, identity, and admin channels across the whole environment. One foothold, broad operational control. That’s a different class of problem.
CVSS scores won’t catch this. You need an explicit override for systems that push code, broker identity, or change security controls at scale. If one of those is exposed and a serious exploit path exists, routine queue timing is a liability.
The fix isn’t complicated. Tag control-plane assets. Auto-escalate when active exploitation or pre-auth RCE shows up. Pre-approve emergency windows so change control doesn’t eat your response time. And pair patching with threat hunting, because compromise may have happened before the patch dropped.
One rule does most of the work: when a vulnerable system controls other systems, blast radius beats queue order.
Read the full breakdown, including what to change this week.