John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
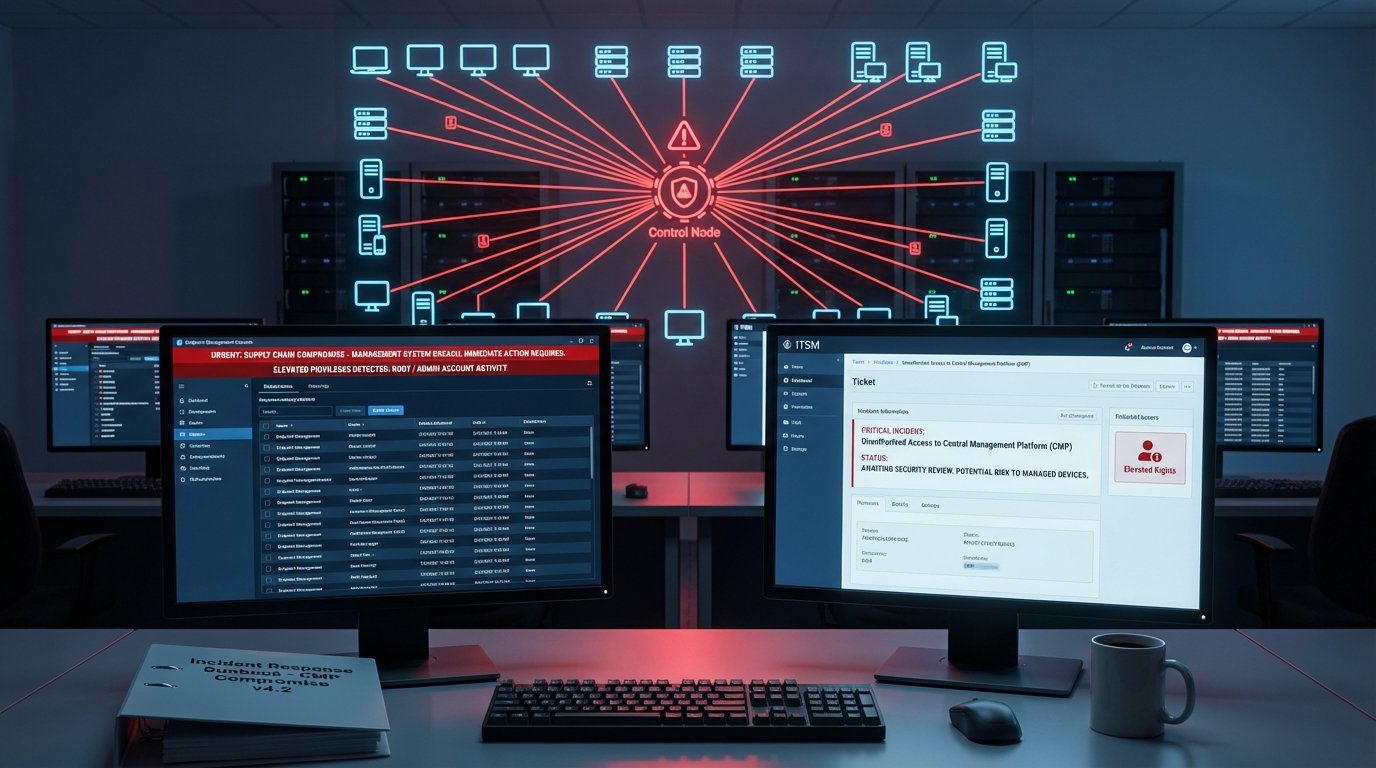
Your Management Stack Is the Shortcut Attackers Are Looking For
CISA flagged endpoint management systems after a real incident. Researchers dropped pre-auth RCE chains for BMC FootPrints ITSM. IP-KVM gear is a network takeover path. The pattern is clear: attackers go for the systems that control everything else.
Read More