John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
Six agencies. One advisory. That doesn’t happen for fun.
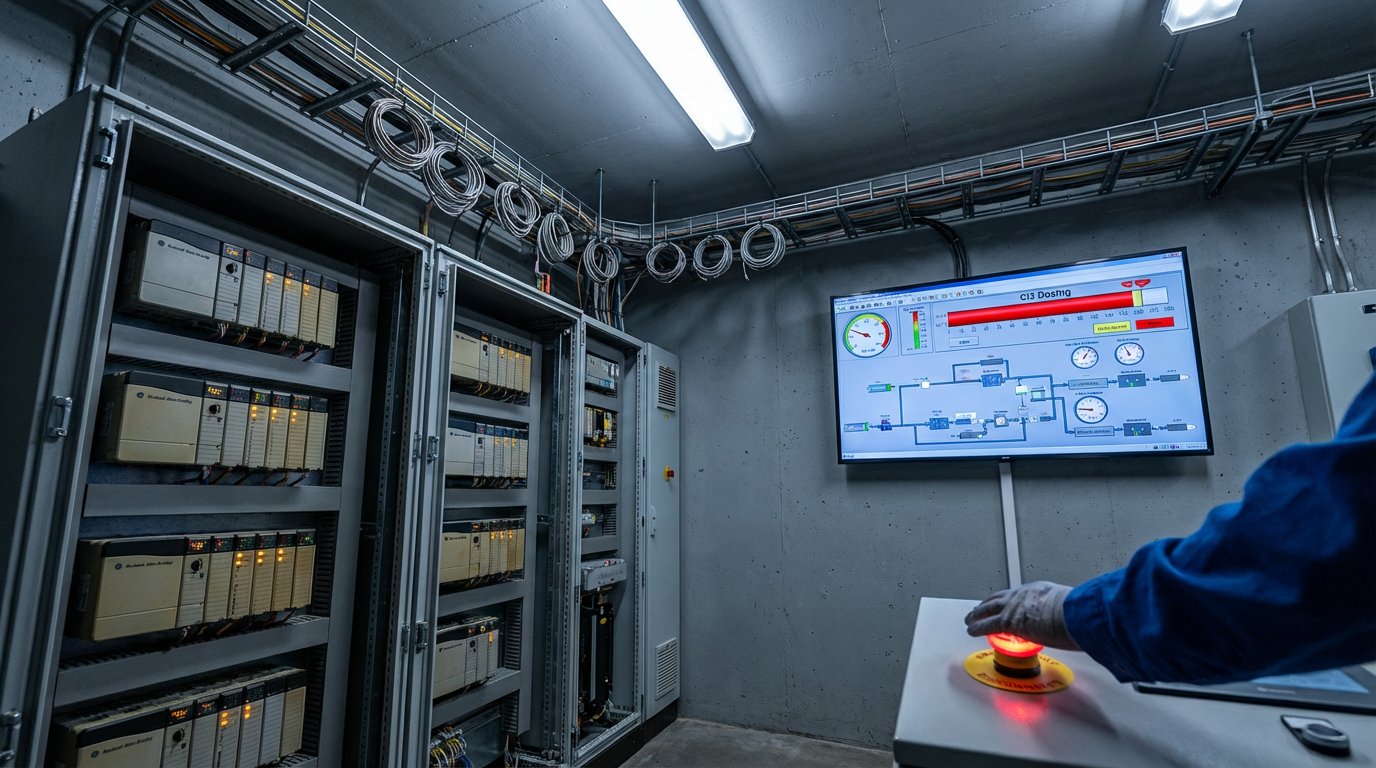
The FBI, CISA, NSA, EPA, Department of Energy, and U.S. Cyber Command all put their names on advisory AA26-097A. The Pentagon’s Cyber National Mission Force is operationally involved. The FBI opened criminal investigations. Iranian-affiliated hackers disrupted programmable logic controllers across U.S. critical infrastructure, causing real operational disruption and financial loss.
The group is CyberAv3ngers, an IRGC affiliate that hit 75+ Unitronics PLCs in water systems back in 2023 and 2024. That was supposed to be the wake-up call. Apparently not enough people woke up, because now they’re targeting Rockwell Automation CompactLogix and Micro850 controllers. Water systems. Energy. Government facilities.
The attacks manipulated data on HMI and SCADA displays. Operators were shown readings that didn’t match reality. Think about that for a second.
The FBI’s assessment connects this escalation to hostilities between Iran, the U.S., and Israel. These aren’t opportunistic criminals. These are state-sponsored operators with strategic objectives.
AA26-097A isn’t one of those vague “be vigilant” advisories. It includes specific indicators of compromise, timeframes, MITRE ATT&CK mappings, and detailed mitigation steps. Remove PLCs from direct internet exposure. Check logs for suspicious traffic on ports 44818, 2222, 102, and 502. For Rockwell devices, set the physical mode switch to run position. Segment IT and OT networks.
CyberAv3ngers hit Unitronics two years ago. The sector said “never again.” Here we are again.
Get the full advisory breakdown, specific IOCs, and mitigation checklist