John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com

From Job Interview to Lab-Infection: How Hackers are Worming Through Your Team
North Korea's newest 'Contagious Interview' wave is turning your own developers into delivery boys. One fake interview is enough to backdoor your entire codebase.
Read More
Persistent Espionage: Mustang Panda's LOTUSLITE Campaign Hits Banking
A refreshed LOTUSLITE variant from Mustang Panda is targeting Indian banks and South Korean policy groups. Nation-states aren't extortionists. They're collectors. And they're patient.
Read More
Helpdesk Squeeze: BlackFile and the Vishing Revival
A new extortion group called BlackFile is making millions by doing something shockingly low-tech: calling your helpdesk and asking them to hand over access.
Read More
Administrative Betrayal: The Bitwarden CLI Supply Chain Hijack
A malicious npm package impersonating the Bitwarden CLI installed its own runtime to steal secrets. When security tools are the attack vector, the whole CI/CD pipeline becomes a weapon.
Read More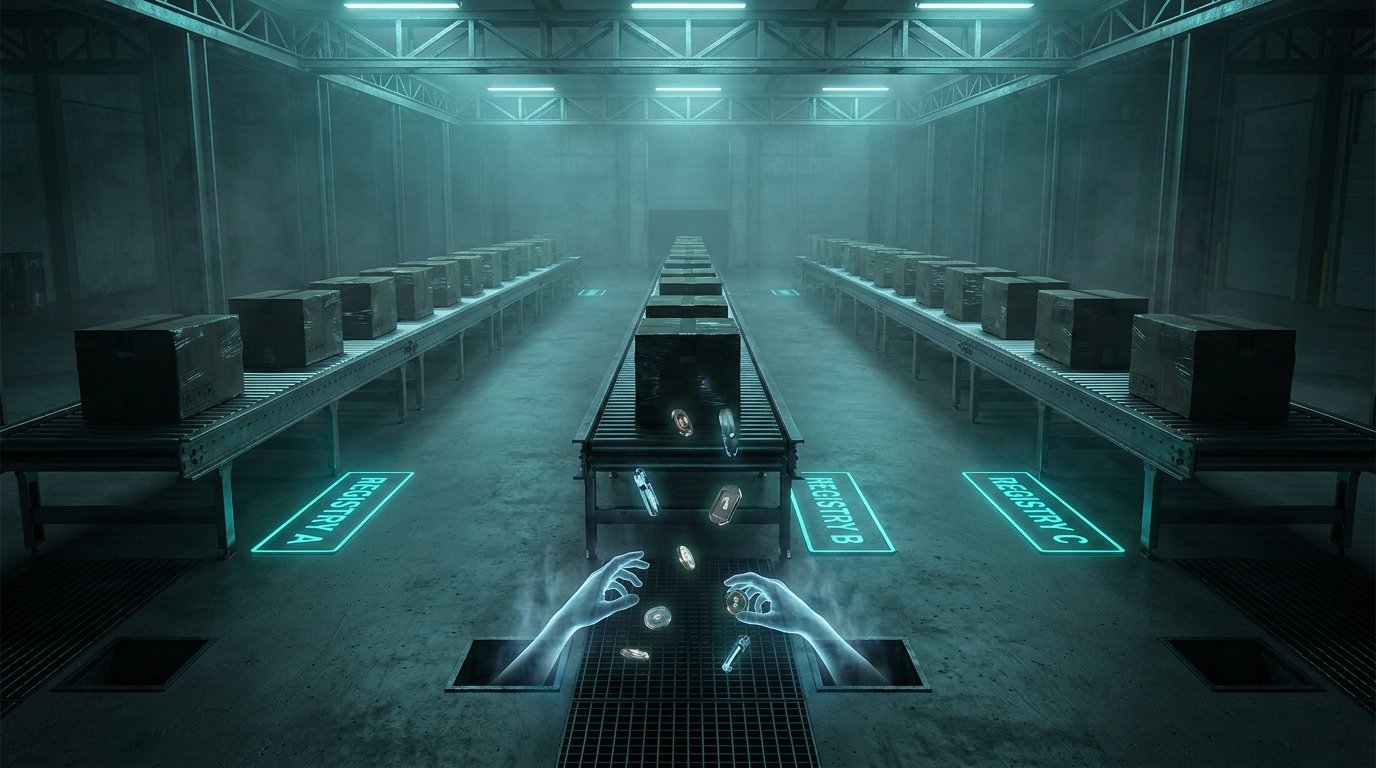
The 48-Hour Secrets Sprint: How Three Registries Were Swept in One Weekend
A coordinated 48-hour sprint hit npm, PyPI, and Docker Hub, targeting developer secrets at scale. From infected AI libraries to a trojanized security scanner, the supply chain is moving faster than your detection.
Read More
Lotus Wiper Hits Venezuela: When Cyber War Targets the Grid
Lotus Wiper has been quietly targeting Venezuelan energy and utility firms since late last year. This isn't about intelligence gathering; it's about disruption. When the goal is to stop the lights, the defensive playbook has to change.
Read More
The Devices China Already Owns: Pre-Positioning for Future Conflict
China's state actors aren't just hacking networks; they're acquiring real estate. A massive joint advisory reveals how covert device networks are being pre-positioned inside everyday hardware like routers and NAS devices, waiting for the right moment to be activated.
Read More
China Is Running Two Operations Against Taiwan at Once
Cisco Talos found Lua-based malware targeting Taiwanese NGOs and universities. Taiwan's intelligence service identified 13,000 AI-amplified influence accounts and 860,000 posts. These are not separate stories.
Read More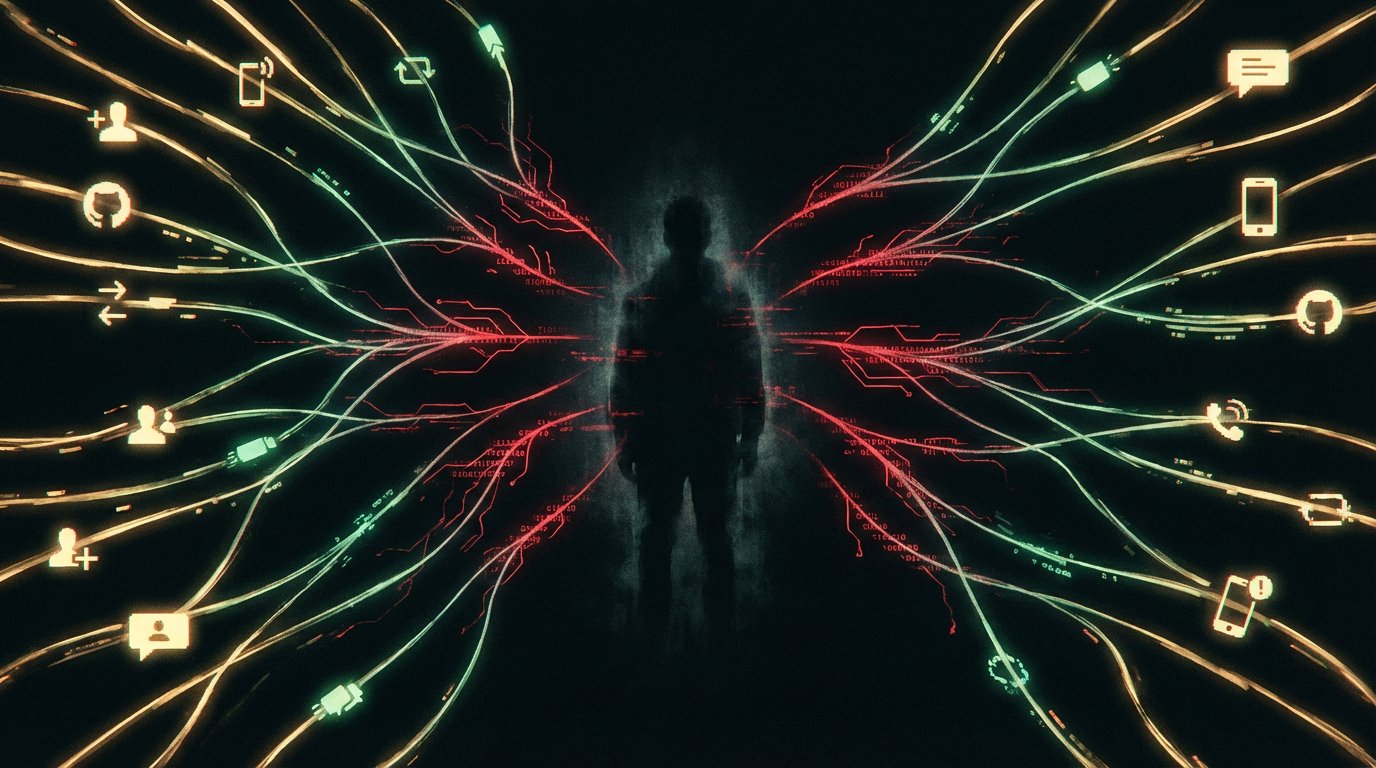
The Attack Isn't Coming From a Stranger. It's Coming From Your GitHub Notifications.
Four active campaigns documented today share one design principle: the attack arrives from something the target already trusts. APT37 builds friendships on Facebook first. Attackers abuse GitHub and Jira notifications to deliver phishing links that pass SPF, DKIM, and DMARC. A fake rocket alert app spies on people in a conflict zone. AI-generated articles seed Google Discover with scareware.
Read More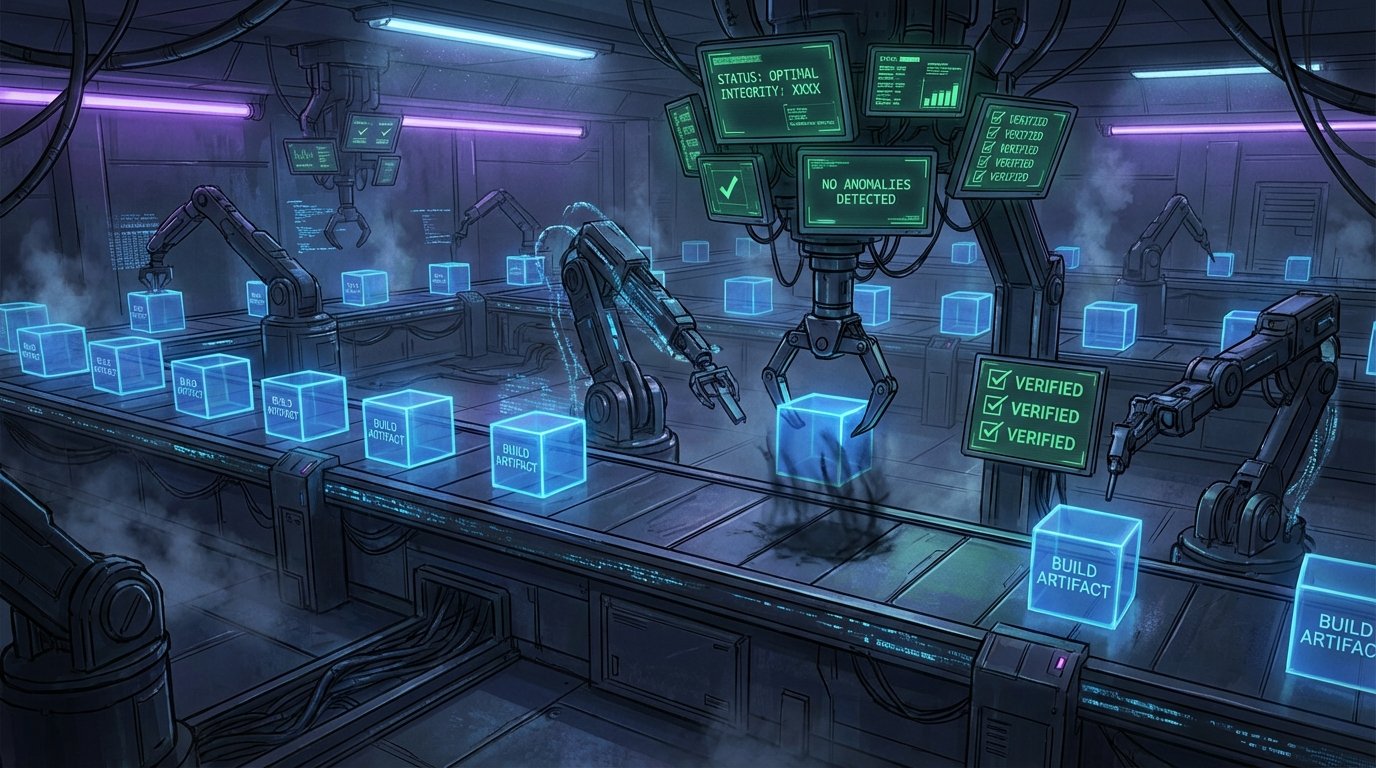
Your Antivirus Won't Catch This. Here's Why.
MSBuild is a Microsoft-signed Windows binary. SHADOW#REACTOR chains VBScript to PowerShell to a payload disguised as plain text. Both campaigns share one design principle: look like the environment, not like malware. Multiple independent threat actors are converging on the same technique, and most defenders aren't ready for it.
Read More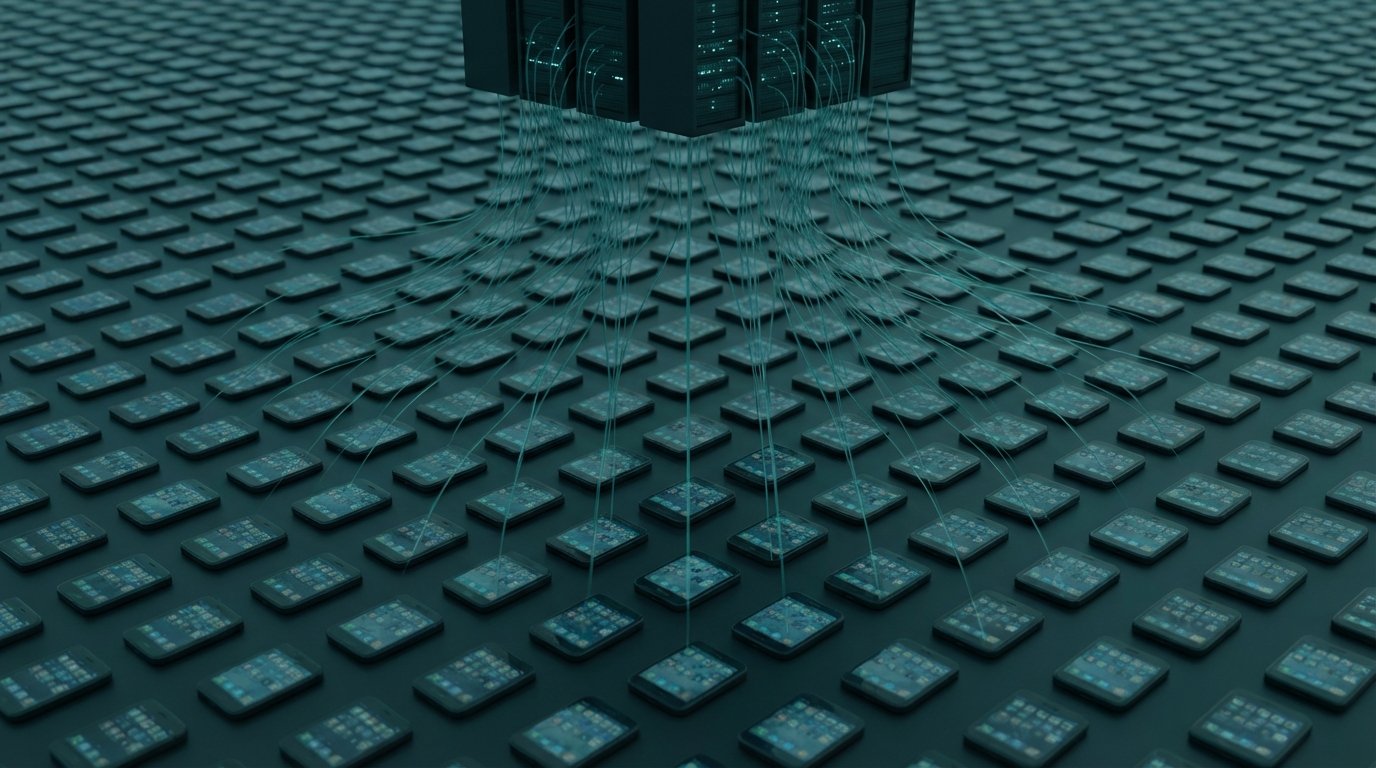
Your Phone, Your Browser, Your Router. All Still Working. All Compromised.
220,000 Android phones recruited into a criminal proxy network via Facebook ads. 108 Chrome extensions in the official Web Store harvesting Google and Telegram credentials. Russia's GRU running DNS hijacks through 18,000 home routers until law enforcement shut it down. Three campaigns, one pattern: your device keeps working while someone else uses it.
Read More
The Week the Clock Ran Out
Defenders got squeezed this week. AI sped up vuln discovery, OT attacks stayed active, and trusted update channels turned into incident response events.
Read More
The Week the Clock Ran Out
Defenders got squeezed this week. AI sped up vuln discovery, OT attacks stayed active, and trusted update channels turned into incident response events.
Read More
Russian Satellites. Iranian Missiles. A U.S. AWACS. Three Sources Now Document the Same Kill Chain.
A Russian satellite imaged Prince Sultan Air Base before the March 27 strike. Iran hit a U.S. E-3 Sentry AWACS. A Russian satellite returned the next day for damage assessment. A Ukrainian intelligence assessment, a Western military source, and a U.S. orbital analytics firm all now document pieces of that sequence.
Read More
The Trusted Download Is the Attack Vector
CPUID's official site served a malicious installer for hours. A fake WakaTime extension has been spreading across dev machines for months. Two separate campaigns, one shared trick: they got inside the thing you already trusted.
Read More
Apple Patched the Door. Attackers Used the Window.
macOS 26.4 added Terminal security scanning to block ClickFix attacks. Within 48 hours, Atomic Stealer was back, running through Script Editor instead. One click. No warning.
Read More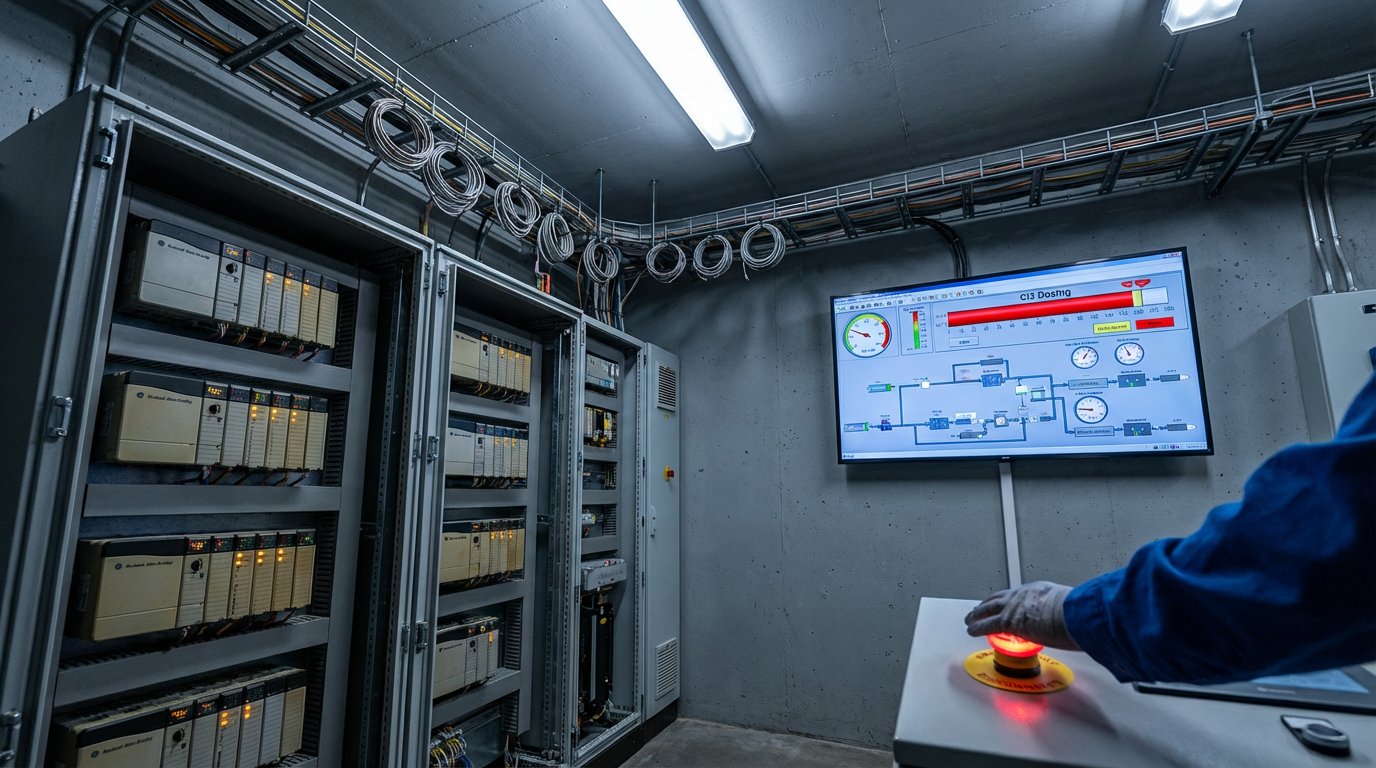
Six Federal Agencies Just Told You to Disconnect Your PLCs. Here's What Forced Their Hand.
FBI, CISA, NSA, EPA, DOE, and Cyber Command co-signed a single advisory on Iranian hackers disrupting PLCs at U.S. water, energy, and government facilities. This isn't theoretical.
Read More
Russia's GRU Hijacked 18,000 Routers to Steal Microsoft 365 Tokens Without a Single Piece of Malware
APT28 changed the DNS settings on 18,000 home routers and stole Microsoft 365 tokens after users completed MFA. No malware needed. Your second factor was irrelevant.
Read More
China's TA416 Is Back in Europe After Two Years. They Brought New Tricks.
TA416 has resumed targeting EU government and diplomatic organizations with PlugX malware, now abusing OAuth redirects to slip past traditional phishing defenses.
Read More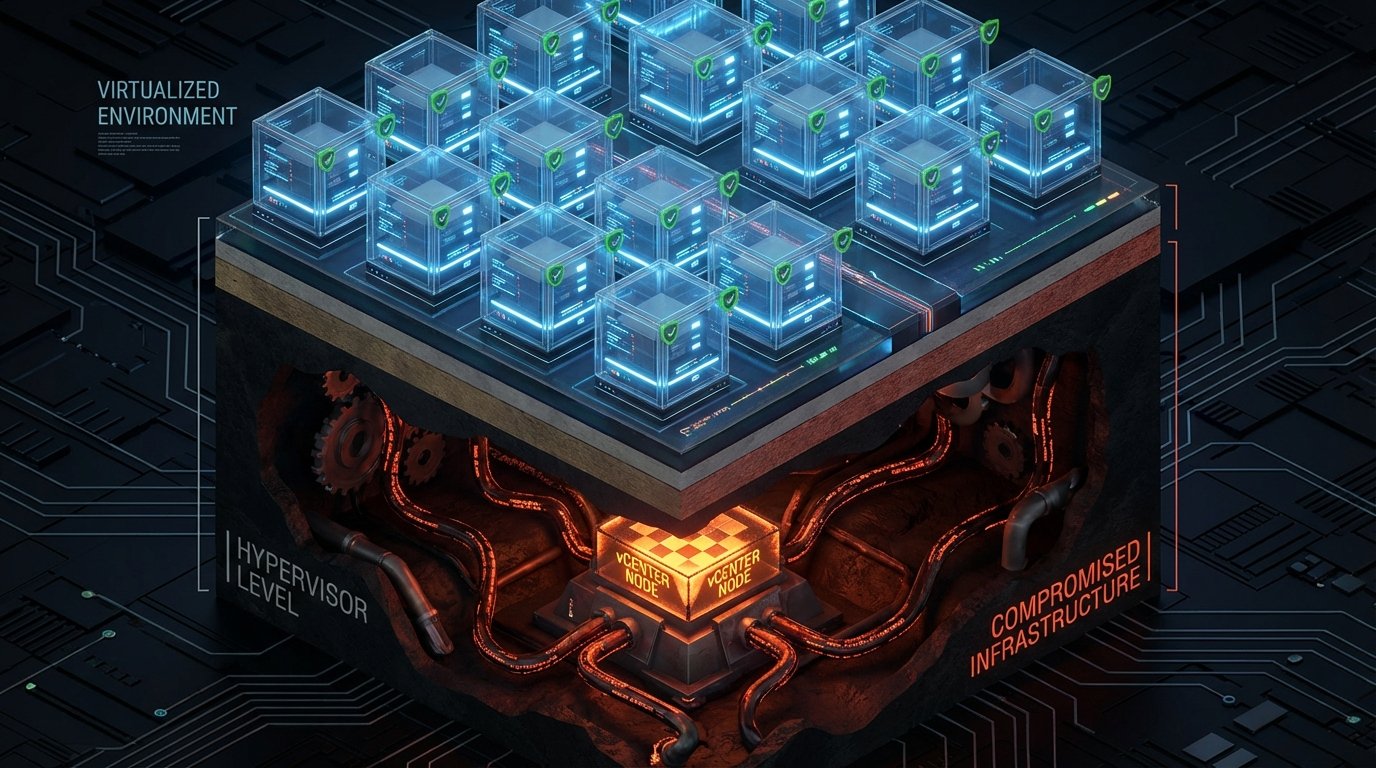
BRICKSTORM Hides Where Your EDR Can't See It
A suspected China-nexus espionage operation targets VMware vCenter and ESXi hypervisors, persisting at the virtualization layer where endpoint security is blind.
Read More
The Storm Infostealer Doesn't Decrypt Your Passwords Locally. It Takes Them Home First.
Storm ships encrypted credentials to attacker servers for decryption, bypassing every endpoint detection built to catch local credential theft.
Read More
Your Encrypted Messaging App Is Secure. Your Account Isn't.
The NCSC warns that Russian hackers are hijacking Signal and WhatsApp accounts through social engineering, not by breaking encryption.
Read More
Russian Hackers Are Going Back to Old Victims to Check If the Door's Still Open
CERT-UA warns APT28 and Void Blizzard are revisiting old compromises, testing dormant access, and calling targets directly in fluent Ukrainian. Incident response has an expiration date. Attackers don't.
Read More
Delete This Web Shell and It Grows Back. Thanks, Cron.
Microsoft found PHP web shells that take commands through cookies instead of URLs. Delete them and a cron job rebuilds them. Your WAF probably can't see any of it.
Read More
Hackers Built a SaaS-Style Dashboard to Loot Next.js Apps at Scale
UAT-10608 built an automated framework that exploits a CVSS 10.0 React flaw to compromise Next.js apps, harvest credentials, and display the loot in a searchable dashboard.
Read More
A Zero-Day Turned TrueConf's Update Channel Into a Malware Delivery System
Chinese-nexus actors exploited a zero-day in TrueConf to hijack the update mechanism and push trojanized updates to Southeast Asian government agencies.
Read More
Stryker Recovered from an Iranian Wiper Attack. It Took Three Weeks and 80,000 Devices.
Iran's Handala group wiped 80,000 devices across Stryker's global network. Maryland EMS lost digital ECG transmission. The DOJ confirmed Iran's government runs Handala.
Read More
Two Active Campaigns Are Using WhatsApp as the Front Door
A VBS-based Windows hijack and an Italian spyware operation are both running through WhatsApp right now. Your chat app is a threat vector.
Read More
A Full Android Rootkit Hid in Google Play for Months. 2.3 Million Downloads.
McAfee found a full rootkit hiding in 50+ Google Play apps. It roots your phone, survives factory resets, and hijacks WhatsApp sessions. 2.3 million devices already got it.
Read More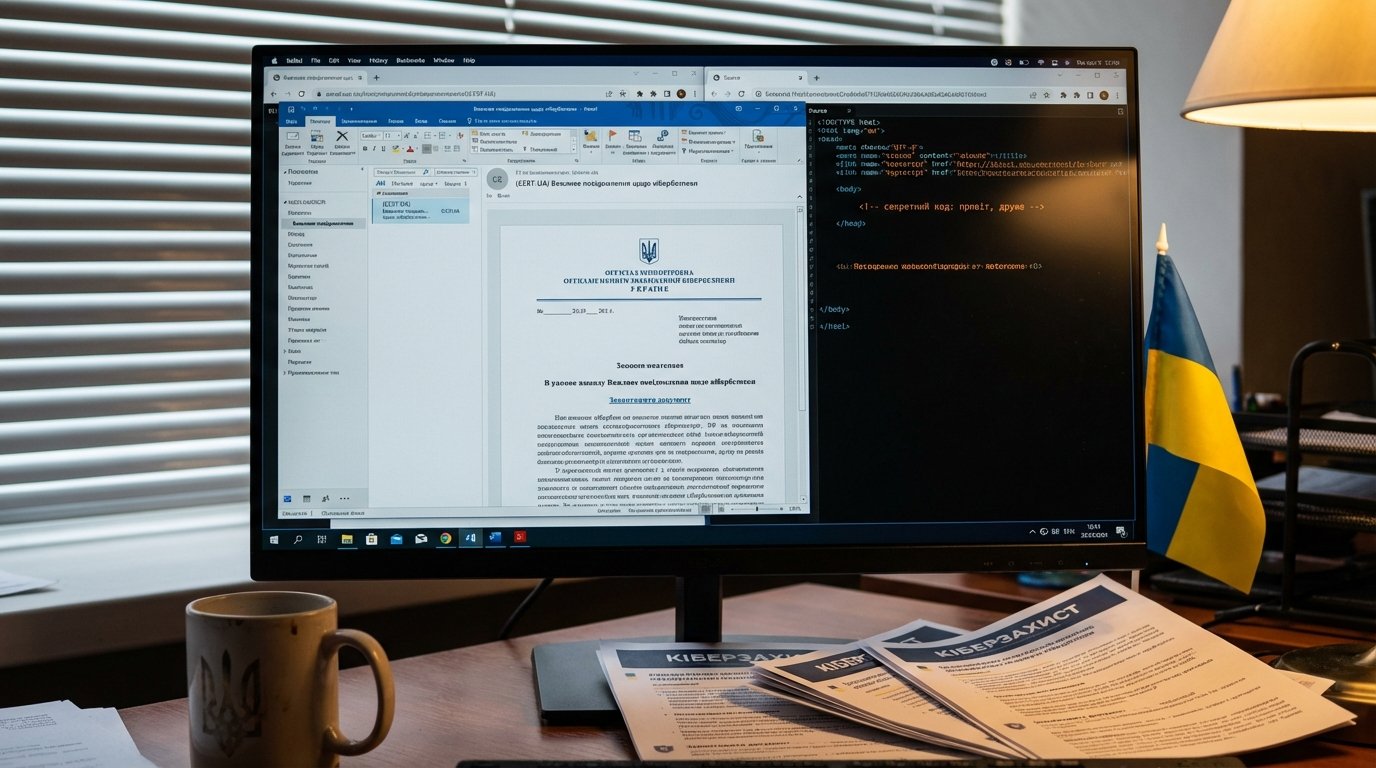
Hackers Impersonated Ukraine's CERT to Push Malware as a 'Security Tool'
Pro-Russia group Cyber Serp sent fake CERT-UA emails carrying a RAT disguised as a protection tool. They claimed 200K infections. Reality was a handful.
Read More
North Korea Backdoored Axios for Three Hours. That Was Enough.
DPRK hackers hijacked the Axios npm package, deploying a self-erasing backdoor across 100 million weekly downloads. Three hours was all they needed.
Read More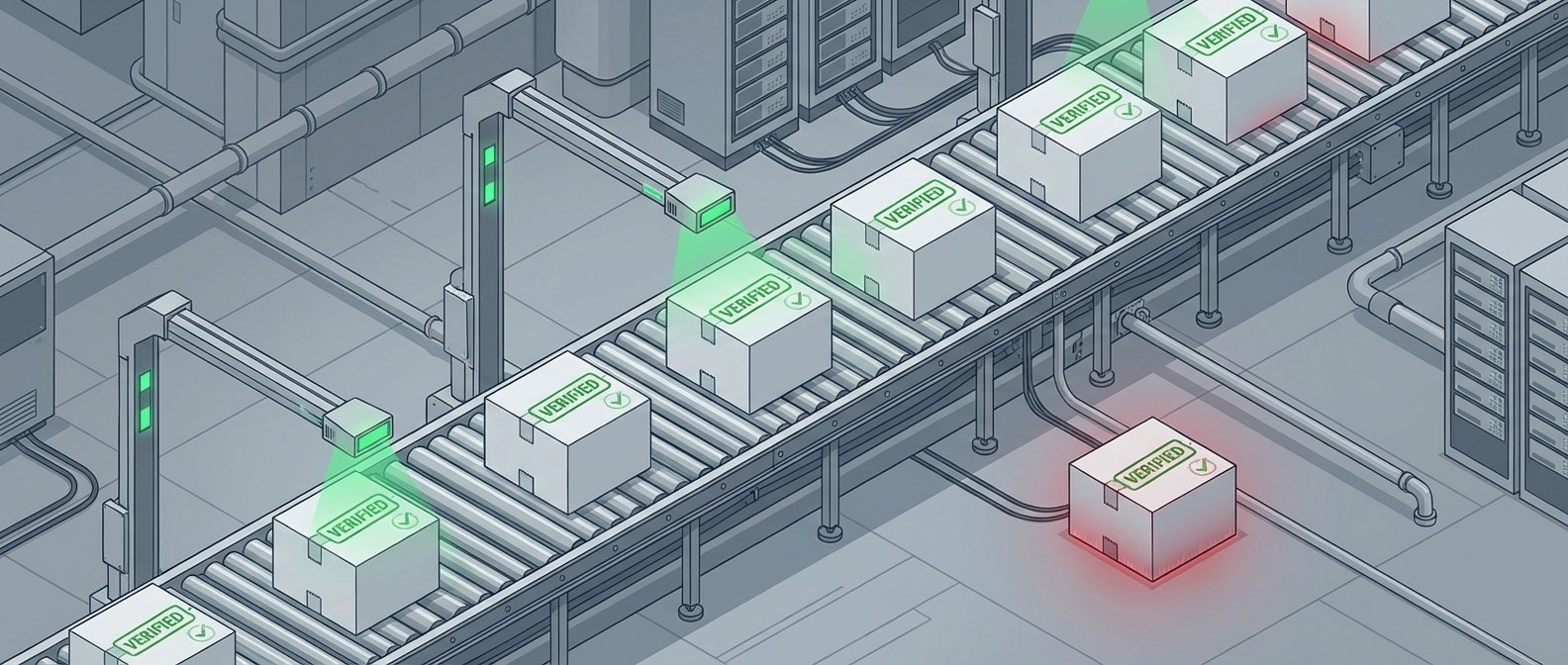
The Week Toolchain Trust Collapsed, Again
TeamPCP kept hitting developer tooling. AI attack surfaces went from theoretical to exploited. Attackers logged in instead of breaking in. And Iran went after the FBI director's personal inbox.
Read More
The Progress We Thought We Were Making Against Hackers? It Just Went Backward.
Dwell time reversed in 2025, and the reason why tells you exactly which threats most security programs are not built to catch.
Read More
Thirty Seconds. That Is All FAUX#ELEVATE Needs to Own an Enterprise Machine.
FAUX#ELEVATE skips consumer targets entirely, checks for corporate domain membership first, then steals Chrome credentials and starts mining Monero in about 30 seconds.
Read More
31.4 Terabits in 35 Seconds: Cloudflare's New Threat Report Shows Attacks Have Gone Industrial
Cloudflare's 2026 threat report documents a record-breaking 31.4 Tbps DDoS attack and reveals that 94% of bot-driven login attempts now bypass MFA by stealing session tokens instead of passwords.
Read More
Your Security Camera Is Probably Someone Else's Window Into the War
Nation-states are routinely hacking unpatched IP cameras to gather physical intelligence during active conflicts, and the cameras being targeted are the cheap, forgotten ones in your building's lobby.
Read More
Iran Is Running Every Cyberattack at Once
Iran isn't running a cyber campaign right now. It's running all of them simultaneously, and Unit 42's latest brief documents exactly that.
Read More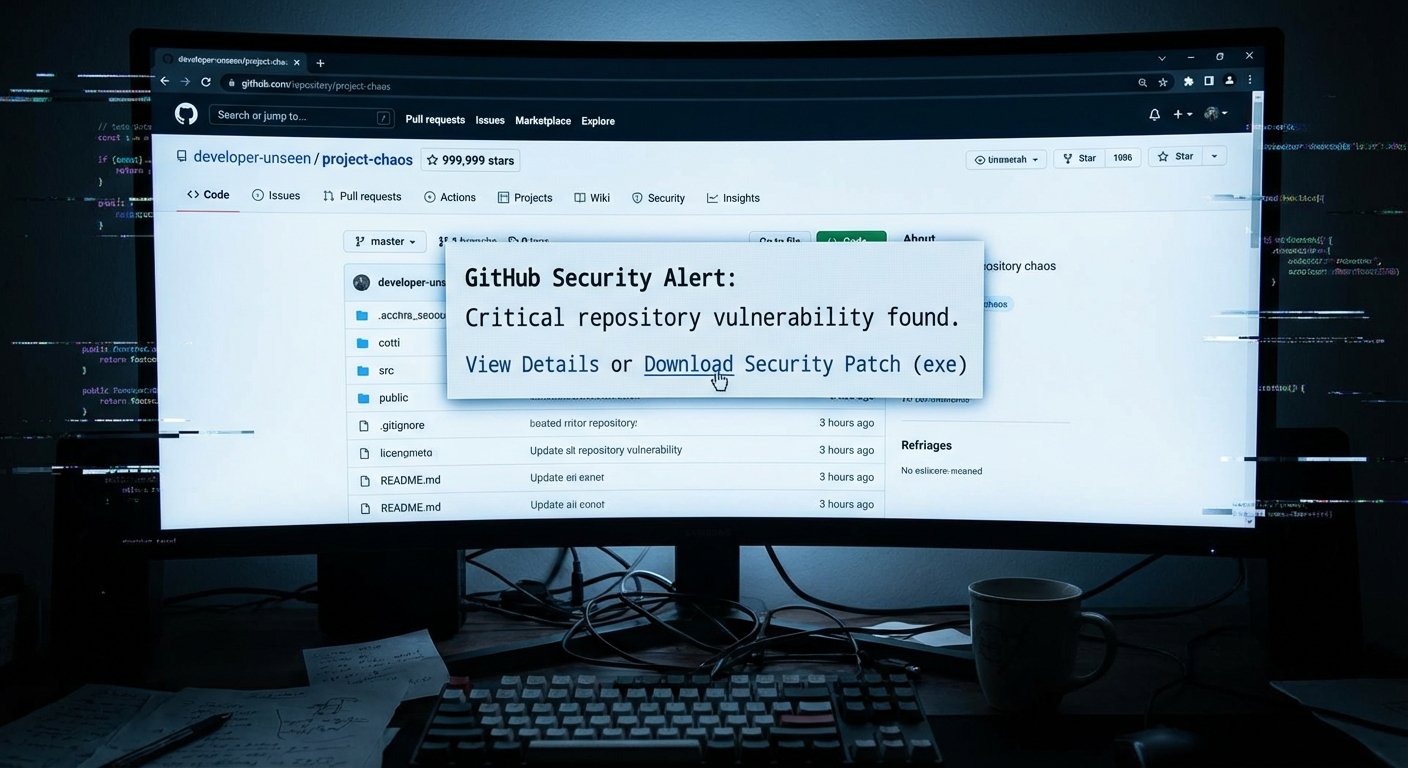
GitHub Is Becoming a Minefield for Developers. Most of Them Have No Idea.
Three simultaneous attacks on GitHub's trust signals -- fake stars, weaponized security alerts, and a scanning bug that let 72 malicious extensions slip through -- show the reputation infrastructure developers rely on is broken.
Read More
China's BPFDoor Got an Upgrade. Passive Defenses Still Can't See It.
Red Menshen's upgraded BPFDoor backdoor now hides even better inside telecom backbone networks, and the only way to find it is active threat hunting that most carriers aren't doing.
Read More
From Wiping 80,000 Devices to Hacking the FBI Director: Handala's March
Iran-linked Handala publicly warned they were coming for the FBI. Kash Patel said nothing. The next morning, his cigar photos were on the internet.
Read More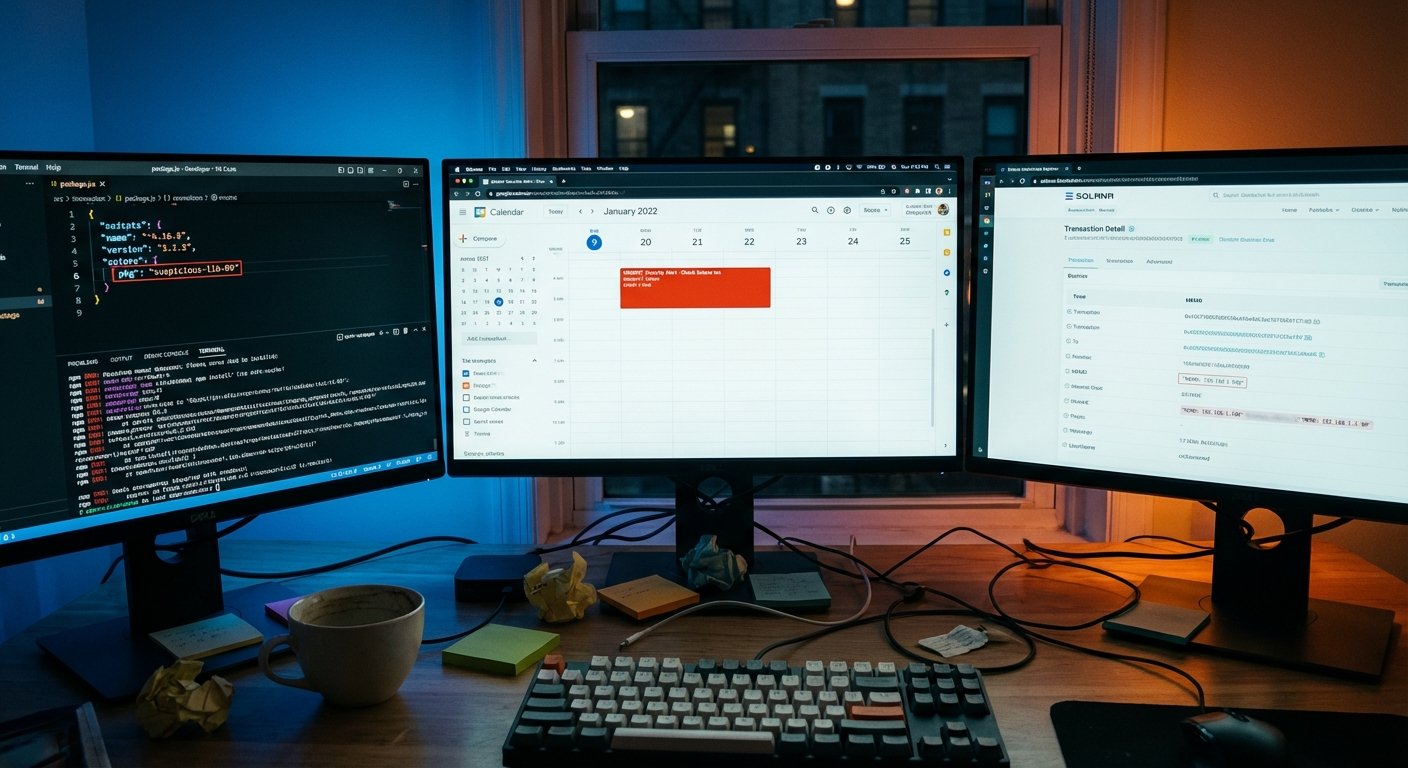
This Malware Hides Its Command Server in the Blockchain, and Borrows Google Calendar Too
GlassWorm targets developers through compromised npm, PyPI, and GitHub packages. Its C2 address is hidden in a Solana blockchain memo. You can't take down a blockchain transaction.
Read More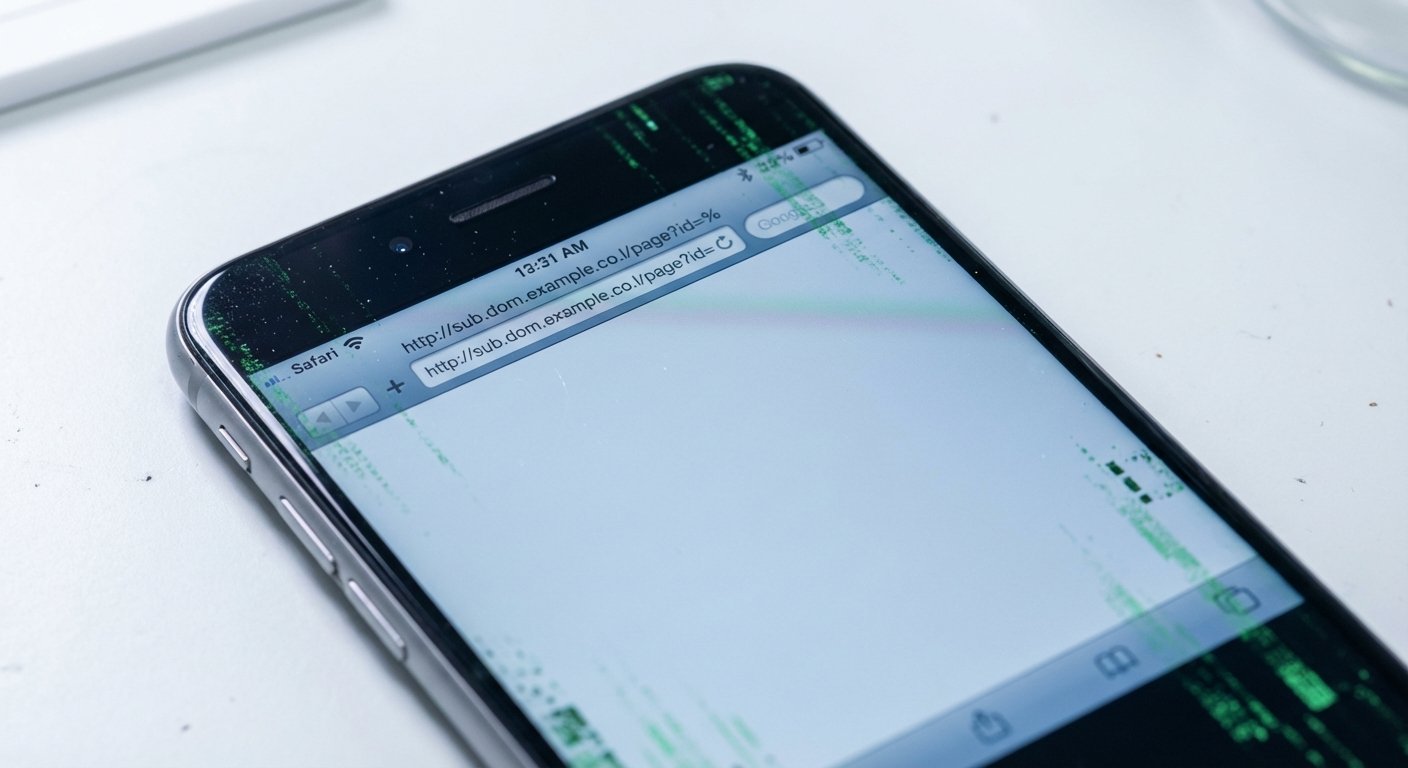
The iPhone Exploit That Won't Die: Operation Triangulation's Code Is Back and More Dangerous
Exploit code from the 2023 Operation Triangulation campaign lives inside Coruna, a new iOS attack framework hitting modern iPhones in mass attacks. Elite nation-state code is now being aimed at everyone.
Read More
China Is Running Three Cyber Operations Against the West Simultaneously. Here's What They Look Like.
BPFDoor sleeping inside telecom networks, US officials blaming Beijing for enabling billion-dollar fraud, and a $20B Telegram black market just sanctioned by the UK. Three fronts, one picture.
Read More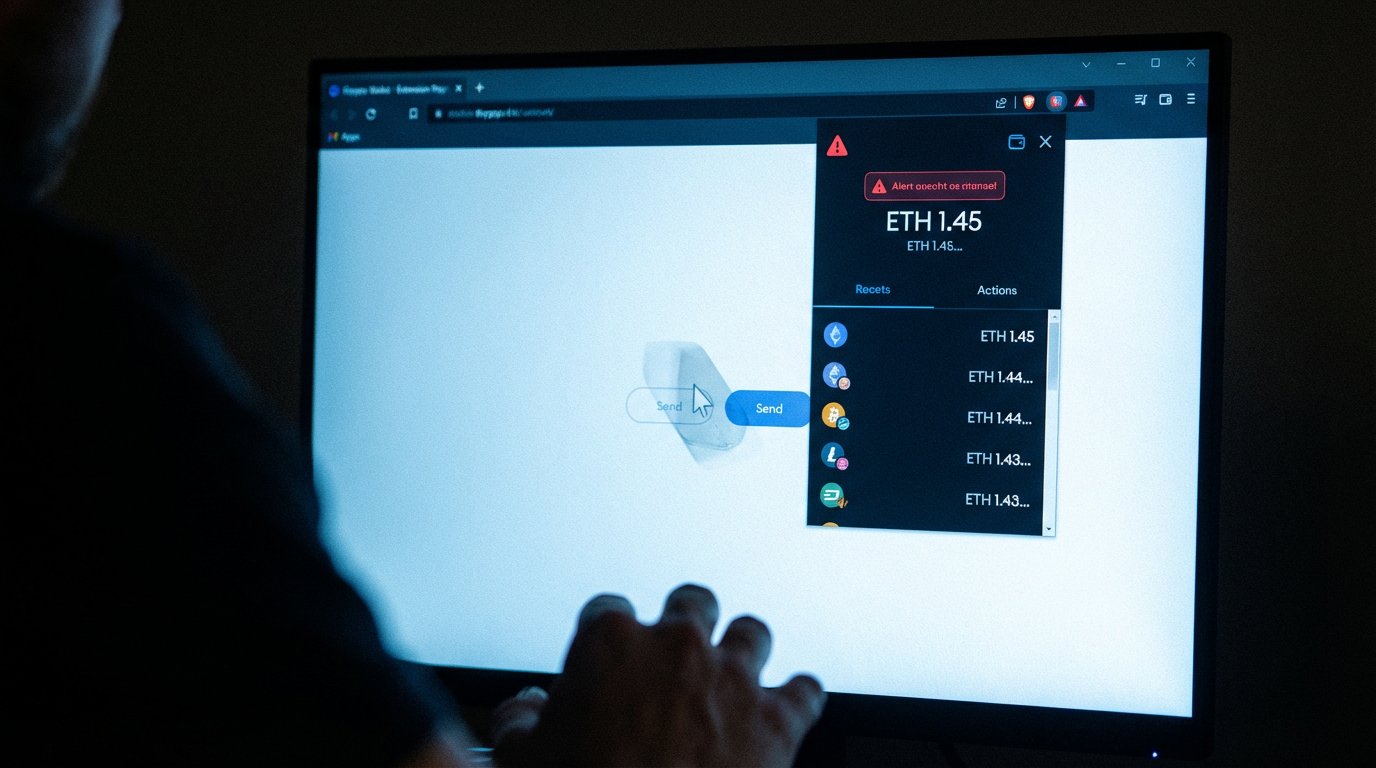
Torg Grabber Is Coming for Your Crypto Wallet Extensions
Torg Grabber is a new infostealer targeting 728 cryptocurrency browser wallet extensions, including MetaMask, Phantom, Exodus, and Coinbase. It's a full MaaS operation with real victims.
Read More
340+ Organizations Hit by M365 Phishing That Bypasses MFA Without Touching Your Password
A device code OAuth phishing campaign has compromised 340+ organizations since February 2026, bypassing MFA and surviving password resets. It's still running.
Read More
CanisterWorm: TeamPCP Hides Its C2 on a Blockchain You Can't Take Down
TeamPCP's new wiper, CanisterWorm, uses an ICP blockchain canister as its C2 resolver -- no domain to seize, no server to kill. And it now runs on any system, not just Kubernetes.
Read More
The Trivy Domino: How One Poisoned Security Tool Spread to a Thousand Cloud Environments
A poisoned Trivy Docker image grew into one of the year's worst CI/CD compromises. Thousands of pipelines ran the payload, LiteLLM got backdoored on PyPI, and the attackers built a three-part kit designed to hit Kubernetes clusters and stay.
Read More
Searching for Tax Forms? Malicious Google Ads Want to Kill Your Antivirus First
A malvertising campaign running since January targets W2 and W9 searchers with a kill chain that disables endpoint security at the kernel level before installing remote access malware. Your antivirus can't stop it once it's running.
Read More
The npm Ghost: That Install Log Looked Normal Because It Was Built to Fool You
Seven malicious npm packages have been stealing sudo passwords and crypto wallet data from developer machines since February. The trick: they generate fake terminal output so convincing that developers don't look twice.
Read More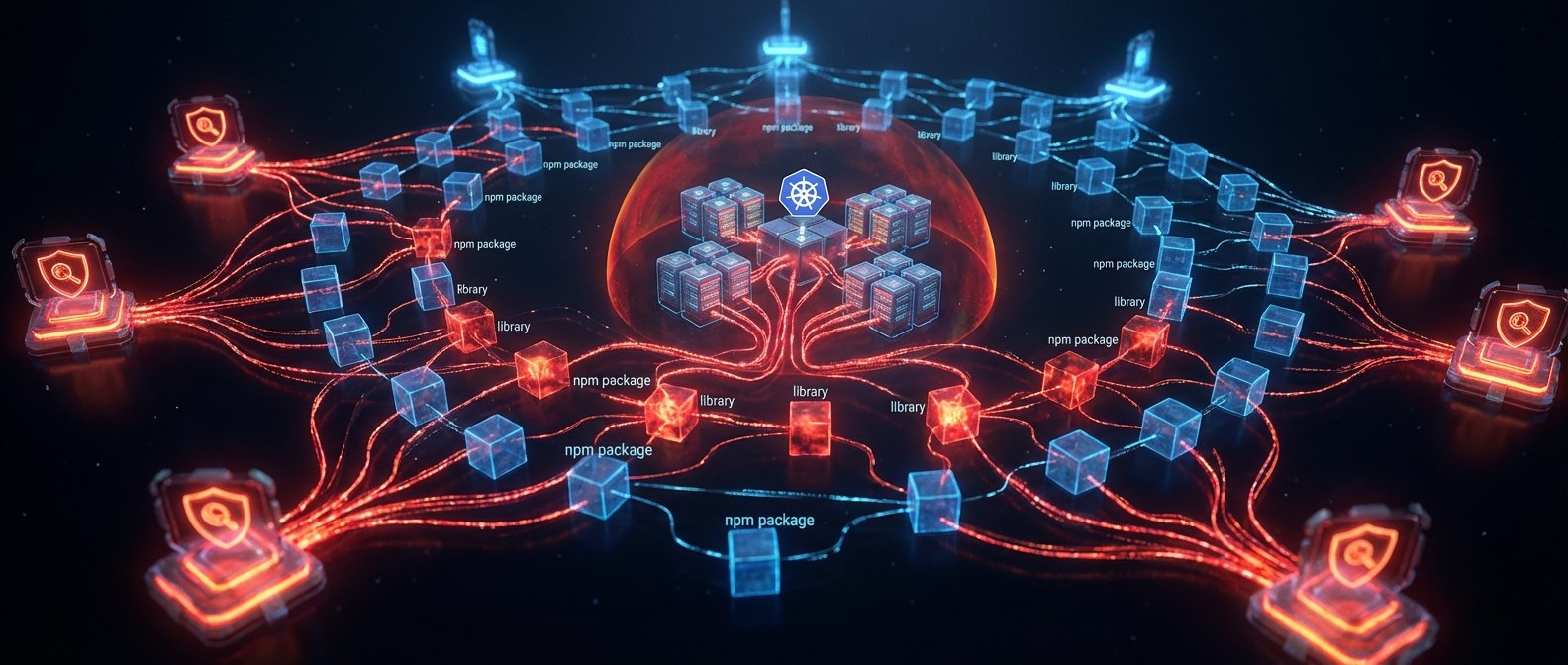
CanisterWorm: How TeamPCP Hijacked Your Security Scanners and Built an Untakeable Botnet
TeamPCP compromised Trivy and KICS CI/CD scanner tags, spread CanisterWorm to 47 npm packages, and deployed a Kubernetes wiper targeting Iranian timezones -- all controlled via blockchain C2 that can't be taken down.
Read More
Someone Is Broadcasting a Numbers Station Through the Iran War
Since US and Israeli strikes on Iran began on February 28, a shortwave numbers station at 7910 kHz has been broadcasting in Farsi twice daily. Signal analysis points toward Ramstein Air Base.
Read More
Two Tools Published This Week Just Broke Chrome's Encryption and Bypassed Your MFA
VoidStealer cracked Chrome's Application-Bound Encryption via a debugger trick, while Astaroth defeats SMS, TOTP, and push MFA in real time -- and the only method that survives both is FIDO2.
Read More
Inside the North Korean IT Worker Playbook: IBM and Flare's New Research Shows Exactly How They Get In
IBM and Flare published the most detailed technical breakdown yet of how North Korean IT workers infiltrate US companies, including specific detection controls security and HR teams can actually use.
Read More
How a Virginia Security Firm Set a Trap and Caught a North Korean Spy Applying for a Remote Job
Nisos set up a fake hiring scenario, handed a suspected DPRK worker a monitored laptop, and caught them. The most unsettling part: the companies already infiltrated had no idea until Nisos called.
Read More
You Can't Seize the Internet: Iran's Handala Hackers Were Back Online Hours After the FBI Acted
The DOJ seized four Handala domains. Iran's MOIS-backed hackers had new infrastructure up within hours, called the action 'trivial,' and kept operating. That tells you everything about the limits of domain seizures as deterrence.
Read More
Handala, Publicly Attributed: What the FBI Seizure Changes About Iran Cyber Signaling
The FBI seized Handala's sites and released a 40-page warrant formally linking the group to Iran's intelligence ministry. Attribution just moved from analyst opinion to federal court filing.
Read More
Your Encrypted Chat Is Fine. Your Trust Model Isn't.
The FBI and CISA warn that Russian intelligence compromised thousands of Signal and WhatsApp accounts -- not by breaking encryption, but by tricking users into handing over access. Here's what that means and what to do.
Read More
Botnet Takedown at Massive Scale: Good News, Short Window
New scale confirmation makes this takedown meaningful, but defenders only win if they use the brief recovery window to harden fast.
Read More
Messaging and Collaboration Infrastructure Is Still an APT-Friendly Entry Point
Zimbra exploitation, Roundcube sanitizer bypasses, and OpenSIPS auth-bypass risk all point to one truth: communication infrastructure remains a high-value route to durable access.
Read More
Attacker Scale in 2026: Botnets, EDR Killers, and Phishing-as-Operations
From BYOVD-based EDR suppression to tax-season phishing pipelines and botnet disruption, attacker scale now comes from operational integration, not one breakthrough trick.
Read More
Mobile Trust Is Fracturing: Android Fraudware and iOS Exploit Chains Converge
Perseus on Android, DarkSword on iOS, and new iPhone exploitation reporting point to a shared reality: mobile trust assumptions are breaking across both ecosystems.
Read More
DarkSword Spread Beyond One Campaign. Mobile Risk Has to Follow.
Google threat intelligence ties DarkSword-linked iOS exploitation to a broader actor picture than earlier reporting suggested. The bigger signal isn't the exploit chain. It's that the capability is spreading across actors and channels.
Read More
iPhone Exploit Chains Are Becoming a Market, Not a One-Off
DarkSword iOS exploit capability is showing up across multiple actor sets -- state-linked groups, commercial spyware vendors, and infostealer campaigns. The old 'rare nation-state' framing doesn't hold anymore.
Read More
Ransomware Is Getting Less Profitable and More Prolific
Mandiant's latest report shows ransomware payments declining while victim counts hit record highs. The ecosystem isn't dying. It's fragmenting faster than defenders can track.
Read More
Iran Didn't Need Malware to Cripple Stryker. They Just Used Microsoft Intune.
The Handala group wiped tens of thousands of Stryker devices using the company's own MDM platform. No malware. No exploit. Just admin access and the willingness to press the button.
Read More
Two Spy Campaigns, Two Completely Different Playbooks
A Chinese APT has been sitting inside Southeast Asian military networks for six years. Meanwhile, Russian hackers are stealing Signal accounts with fake support messages. Same goal, wildly different approaches.
Read More
The Software You Trust Is Becoming the Attack: Two Supply-Chain Strikes in One Week
GlassWorm hijacked VS Code extension dependencies. AppsFlyer's SDK got compromised to serve crypto stealers. Both attacks exploited trust, not carelessness.
Read More
Hackers Used Stryker's Own IT Tool to Nuke Its Entire Device Fleet
An Iranian-linked group called Handala reportedly hijacked Microsoft Intune and wiped Stryker's devices at scale. The tool designed to secure their fleet became the weapon that destroyed it.
Read More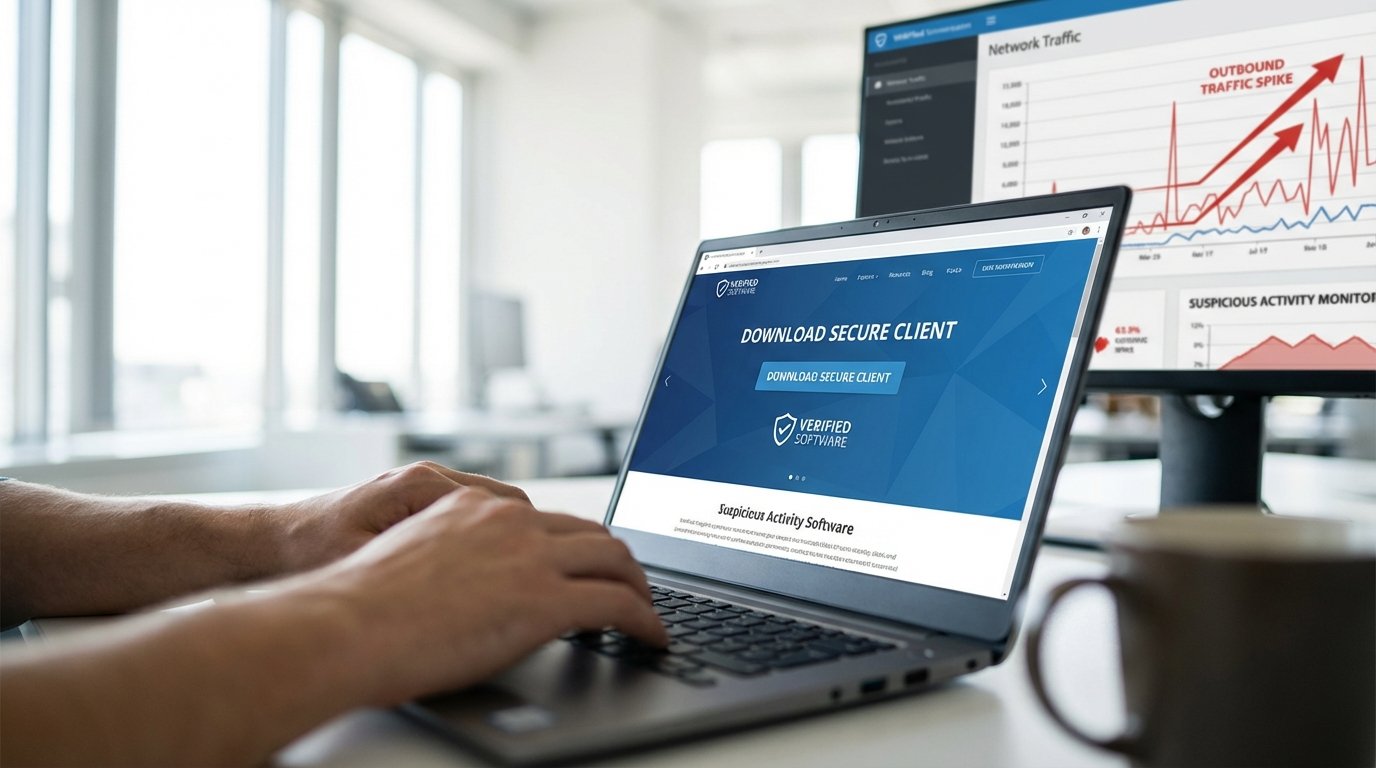
Storm-2561: Googling Your VPN Download Just Became a Security Risk
Microsoft exposed Storm-2561, a threat actor using SEO poisoning to serve fake VPN downloads that steal corporate credentials. The attack requires zero phishing emails. Just a search engine.
Read More
Iran Hit a Medical Device Giant, a NATO Parliament, and Your Instagram Feed on the Same Day
March 11 wasn't three separate cyberattacks. It was one coordinated Iranian campaign across three fronts: a wiper on Stryker, a breach of Albania's parliament, and an influence op on Instagram. All in 24 hours.
Read More
APT28's Covenant Trick and North Korea's AirDrop Hack: How Nation-States Borrow Their Tools
Russia's APT28 hijacked an open-source red-team tool to hit Ukraine. North Korea's UNC4899 used Apple AirDrop to break into a crypto firm. Both attacks exploit the trust we put in legit software.
Read More
The Edge Is the Front Line: FortiGate, ASUS Routers, and the War on Network Perimeters
Enterprise firewalls and consumer routers are getting hammered. FortiGate credential theft and the KadNap botnet show the same failure at the network edge.
Read More
ClickFix Is the Social Engineering Trick That Took Over 2026
A dead-simple social engineering trick is showing up everywhere in 2026. Users paste a command into PowerShell or a Run dialog and boom, malware runs. Three separate campaigns hit this week alone.
Read More

