John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
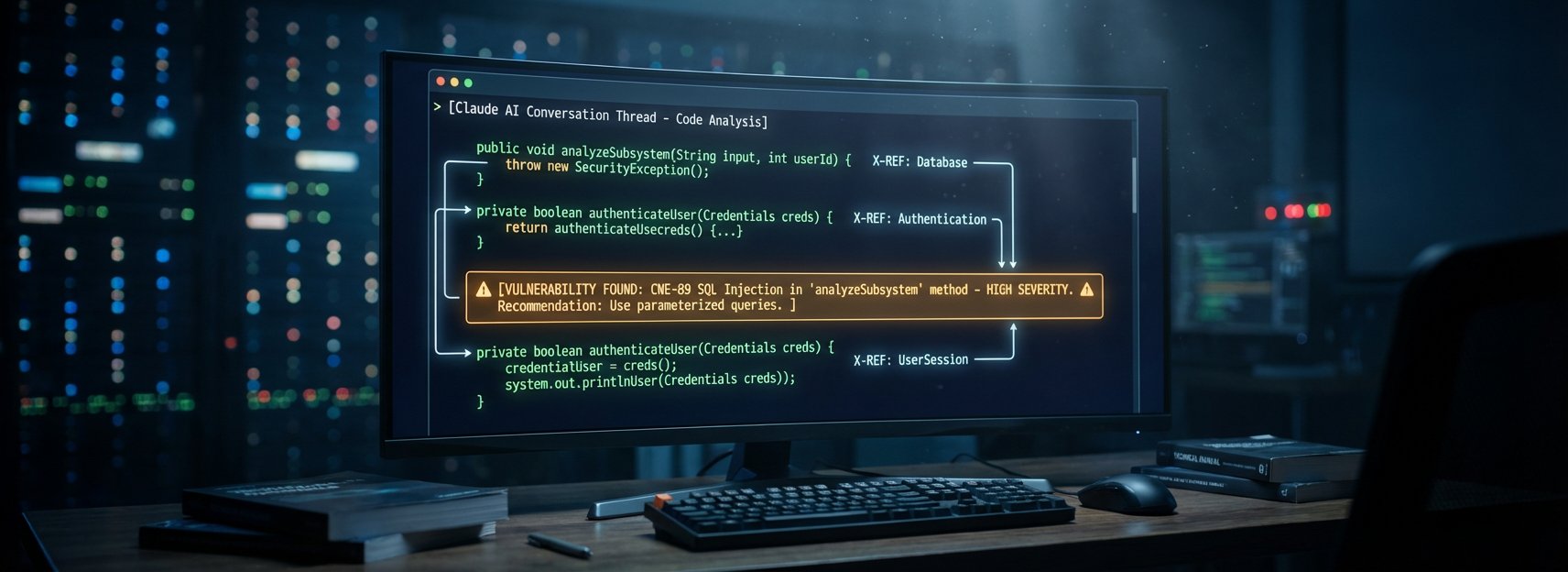
Human auditors looked at this code for 13 years. Nobody found the bug.
Then a researcher at Horizon3.ai fed Apache ActiveMQ’s codebase to Claude. Ten minutes later, CVE-2026-34197 was on the board. CVSS 8.8. Patched March 30. No credentials needed on older versions.
The reason it survived so long is the reason it matters: no single component was broken. The exploit chains through five separate subsystems – Jolokia, addNetworkConnector(), xbean, a URI parameter, and Spring’s application context. Each piece looks fine on its own. Human auditors check components. Claude checked the interactions.
Researcher Naveen Sunkavally called it “80% Claude, 20% gift-wrapping.” The same discovery would have taken a skilled human about a week.
That cuts both ways. Defenders can now surface bugs like this faster than ever. So can attackers running the exact same tools against your unpatched infrastructure.
If you’re running ActiveMQ, upgrade to Classic 5.19.4 or Artemis 6.2.3. Then check your logs for brokerConfig=xbean:http:// in VM transport URIs. That’s your exploitation fingerprint.
Full breakdown of the exploit chain and what it means for AI-assisted security research