John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
Some attack code gets patched and disappears. Some gets weaponized, polished, and handed to a whole new class of threat actors.
The iOS exploit framework being called Coruna is firmly in the second category.
Researchers confirmed that Coruna carries kernel exploit code inherited directly from Operation Triangulation, the 2023 zero-click iMessage campaign that compromised iPhones at Kaspersky by sending a message with no interaction required. That code didn’t retire. It evolved. And now it’s being used in financially motivated mass attacks against ordinary iPhone users.
What Triangulation Was
In 2023, researchers discovered that iPhones belonging to Kaspersky employees had been silently compromised through iMessage. No tap. No link. No warning. The attacker sent a message and owned the device.
The campaign exploited a previously unknown flaw in a never-documented hardware feature of Apple’s own chips. So obscure it took months of reverse engineering just to understand what had happened. Precision tools, surgical strikes against specific high-value targets.
What Coruna Is
Coruna isn’t a single trick. It’s a full framework with five complete exploit chains covering 23 vulnerabilities, including two CVEs tied directly to the original Triangulation campaign. It’s been updated to target Apple’s latest silicon, including A17 and M3 chips, and iOS versions up to 17.2.
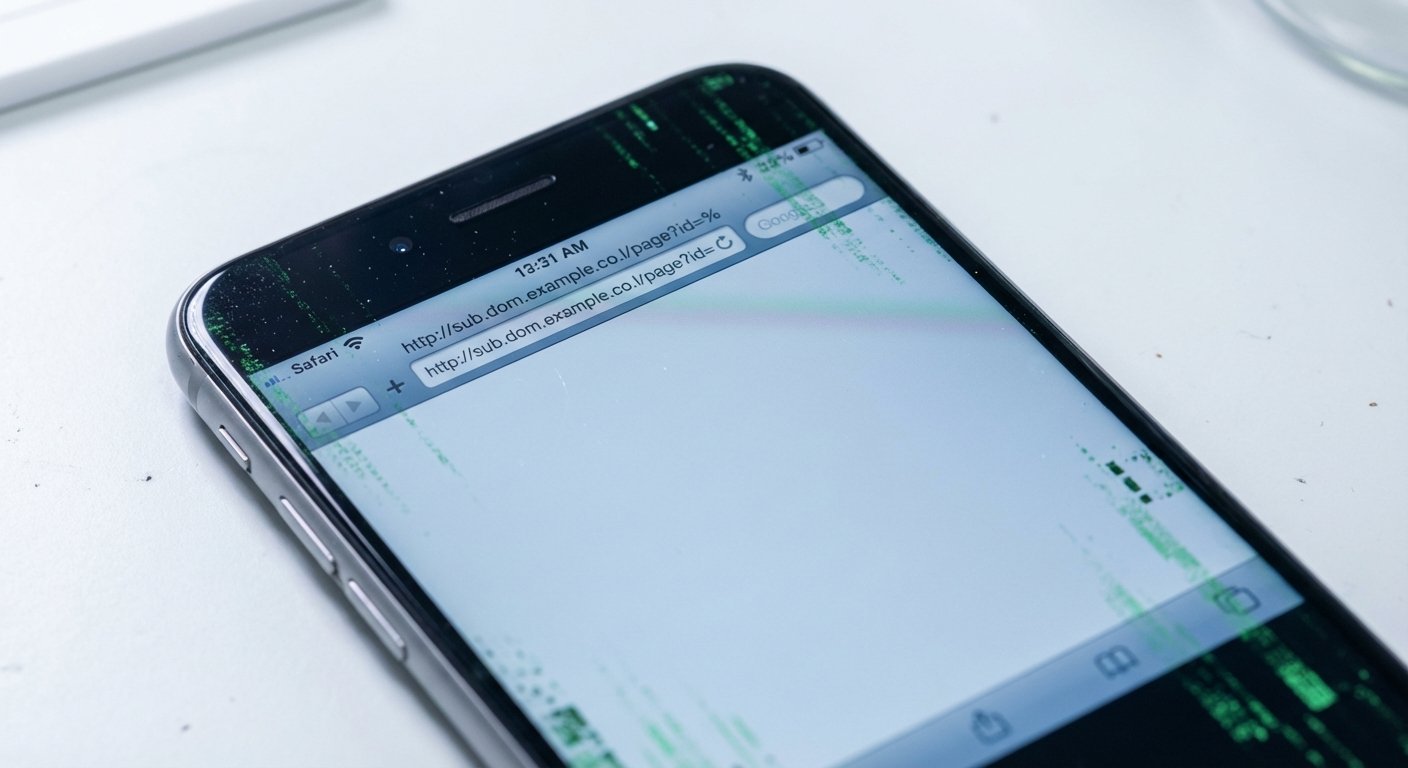
The attack starts in Safari. A stager loads first, fingerprints the device, and selects the right combination of exploits for that specific target. Modular, careful, clearly the product of sustained engineering effort.
Kaspersky’s Boris Larin put it plainly: “Coruna is not a patchwork of public exploits; it is a continuously maintained evolution of the original Operation Triangulation framework.”
Continuously maintained. That’s the phrase worth sitting with.
The Shift That Matters
Triangulation was espionage. Targeted ops against specific people with things worth stealing. Coruna has been observed in mass attacks. The targeting isn’t surgical anymore, and the motivation appears financial.
That changes who’s at risk. When elite exploit code stays in the hands of sophisticated actors running targeted ops, most people are safe by obscurity. When that same code gets thrown at broad populations, obscurity stops being a defense. You don’t have to be interesting to get hit.
Attribution hasn’t been confirmed, but whoever is running Coruna has the technical resources to maintain sophisticated iOS exploits and the operational scope to deploy them at scale.
What to Actually Do
Update your iPhone. Seriously. The vulnerabilities Coruna exploits in iOS up to 17.2 are addressed in later releases. iOS 18 is your best defense right now.
This isn’t a theoretical advisory. These exploit chains are already in use. They work. The gap between nation-state exploit development and mass criminal deployment used to be wide enough that most people could ignore it. Coruna is evidence that gap is closing.
Keep the software current. That’s the move.