John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
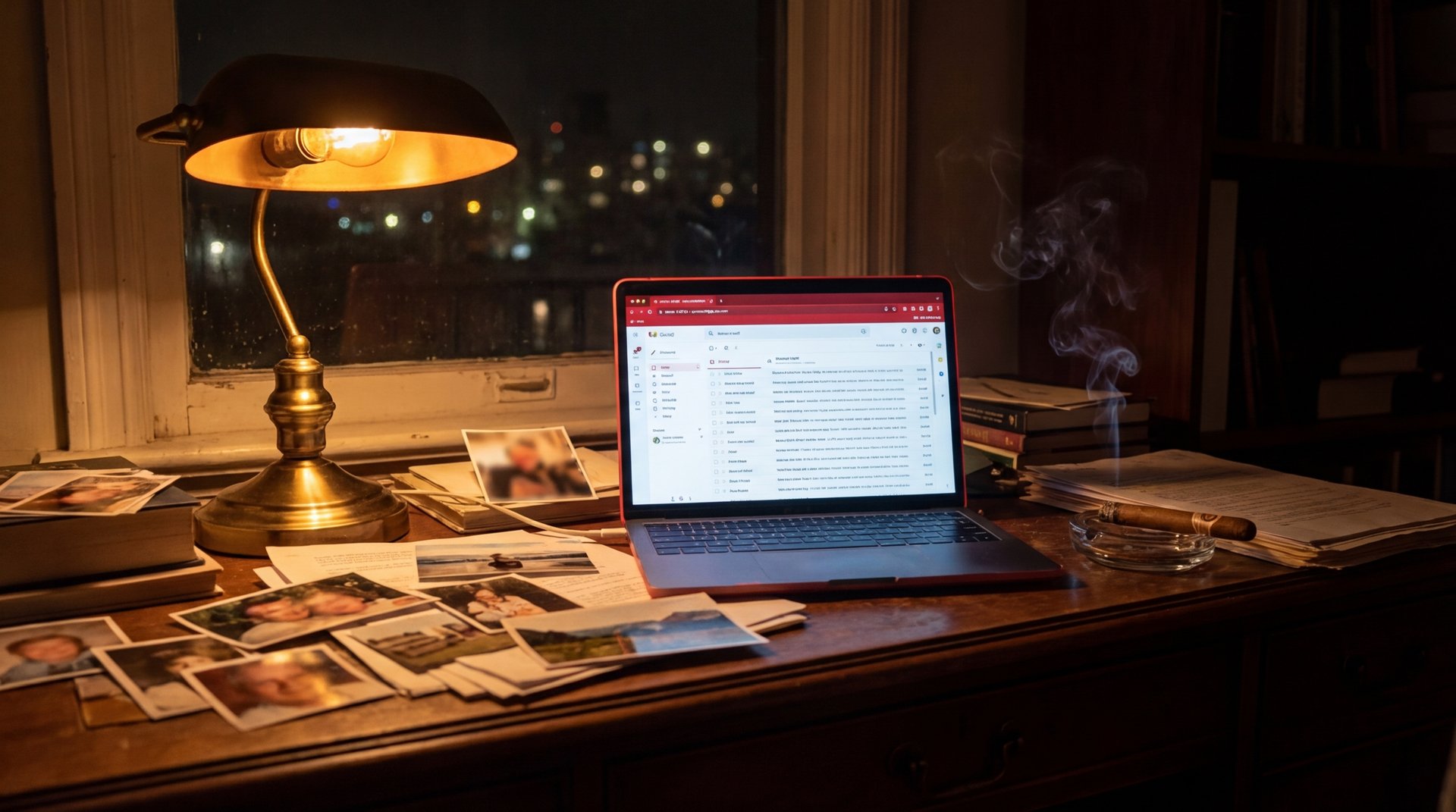
On Thursday, Iran-linked hacking group Handala posted on Telegram that the FBI’s security was “nothing more than a joke” and that they were coming for it. On Friday morning, photographs of FBI Director Kash Patel – smoking a cigar, posing with an antique convertible, taking a selfie with a bottle of rum – landed on the internet alongside hundreds of his personal emails.
The FBI confirmed the breach. Their tone was essentially: don’t worry about it.
Here’s the part that stings: Patel was reportedly warned in December 2024 that Iranian hackers had already accessed some of his personal communications – weeks before he was even confirmed as FBI director. CNN and BBC both reported that warning. There’s no public indication those warnings led to anything being locked down.
Then, on March 19, after the FBI seized four of Handala’s websites, Patel went in front of cameras and said: “We took down four of their operation’s pillars and we’re not done.”
Eight days later, Handala was not done either.
Who Handala Actually Is
The name comes from a famous Palestinian cartoon character. The group presents itself as pro-Palestinian hacktivists. That’s always been the costume. The US Department of Justice formally attributed Handala to Iran’s Ministry of Intelligence and Security in March 2026. Unit 42 at Palo Alto Networks calls them “the most prominent Iranian hacktivist persona” currently operating. They’re a state intelligence operation, not a ragtag collective.
They’ve also been one of the most active and destructive cyber actors targeting the US this month, which is saying something.
The Month in Full
Start with March 11. Handala broke into a Stryker internal administrator account and gained access to Microsoft Intune – the cloud platform that lets admins manage and wipe devices remotely across an entire organization. They wiped approximately 80,000 Stryker employee devices. Remotely. No traditional malware. They just used the legitimate management console to destroy the data.
The FBI responded by seizing four Handala domains on March 19. Patel announced it triumphantly. Handala launched replacement sites within hours and immediately claimed to have breached Lockheed Martin.
Then came the Thursday Telegram post: “Soon you will realise that the FBI’s security was nothing more than a joke.”
Then came the cigar photos Friday morning.
What Was Actually Stolen
The FBI was quick to point out – accurately – that this was Patel’s personal Gmail, not his FBI inbox. The emails run from roughly 2010 to 2019. TechCrunch verified several using DKIM cryptographic signatures. A DOJ official told Reuters the material appeared to be real.
The Gmail address Handala targeted had already been floating around breach databases for years. It was flagged as a target at least since late 2024. The FBI told Patel. Then, two weeks before this happened, he went on camera and taunted the people who had his email address.
The FBI’s statement: “The information in question is historical in nature and involves no government information.”
Probably true. No classified material, no national security damage in the traditional sense. Just a decade of personal correspondence, vacation photos, and some shots of the FBI director doing things he presumably didn’t expect to become public.
Which is, of course, the entire point.
This Is the Playbook
Handala’s statement when they published: “Kash Patel… will now find his name among the list of successfully hacked victims.”
The strategic logic isn’t complicated. They’re not trying to steal launch codes from someone’s 2014 Gmail. They’re trying to make the head of the FBI look like he can’t secure his own email. They’re generating Reuters headlines and BBC coverage running photos of the FBI director posing with rum.
This playbook worked when teenage hackers hit CIA Director John Brennan’s AOL in 2015. It worked when Russian hackers hit John Podesta’s Gmail in 2016. The lesson was supposed to be that senior officials need to treat personal accounts like national security surfaces, because adversaries certainly do.
Handala announced the attack before they launched it. There’s no indication anything was done in that window.
One more detail: the site Handala used to publish the files was flagged by VirusTotal as potentially distributing malware. Anyone who visited to read Patel’s old emails may have gotten malware on their device in the process. The leak is a lure. The lure is also an attack.
The Bigger Picture
Iran has been in a near-complete internet blackout for nearly a month. Its own citizens can barely get online. And yet its intelligence services are running active hack-and-leak operations, wiping American corporate devices, relaunching seized websites within hours, and publishing the FBI director’s personal correspondence using Russian infrastructure and Tonga-registered domains.
The institutions designed to counter this aren’t at full strength right now. The adversaries running these operations clearly know that.
Patel will be fine. His 2014 emails are embarrassing, not catastrophic. The FBI will survive cigar photos. What’s worth paying attention to is everything that had to go wrong for this to happen, and how little of it was stopped.
Read the full breakdown of how Handala went from wiping 80,000 devices to the FBI director’s inbox