John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
Financial fraud costs more than ransomware. The FBI’s 2025 IC3 report puts investment fraud losses at $8.6 billion, with all crypto-related losses topping $11 billion. BEC added another $2.9 billion across 24,700 complaints. We covered the full IC3 breakdown when the report dropped on April 8th. The security industry has largely treated this as someone else’s problem. Three stories this week make it hard to keep doing that.
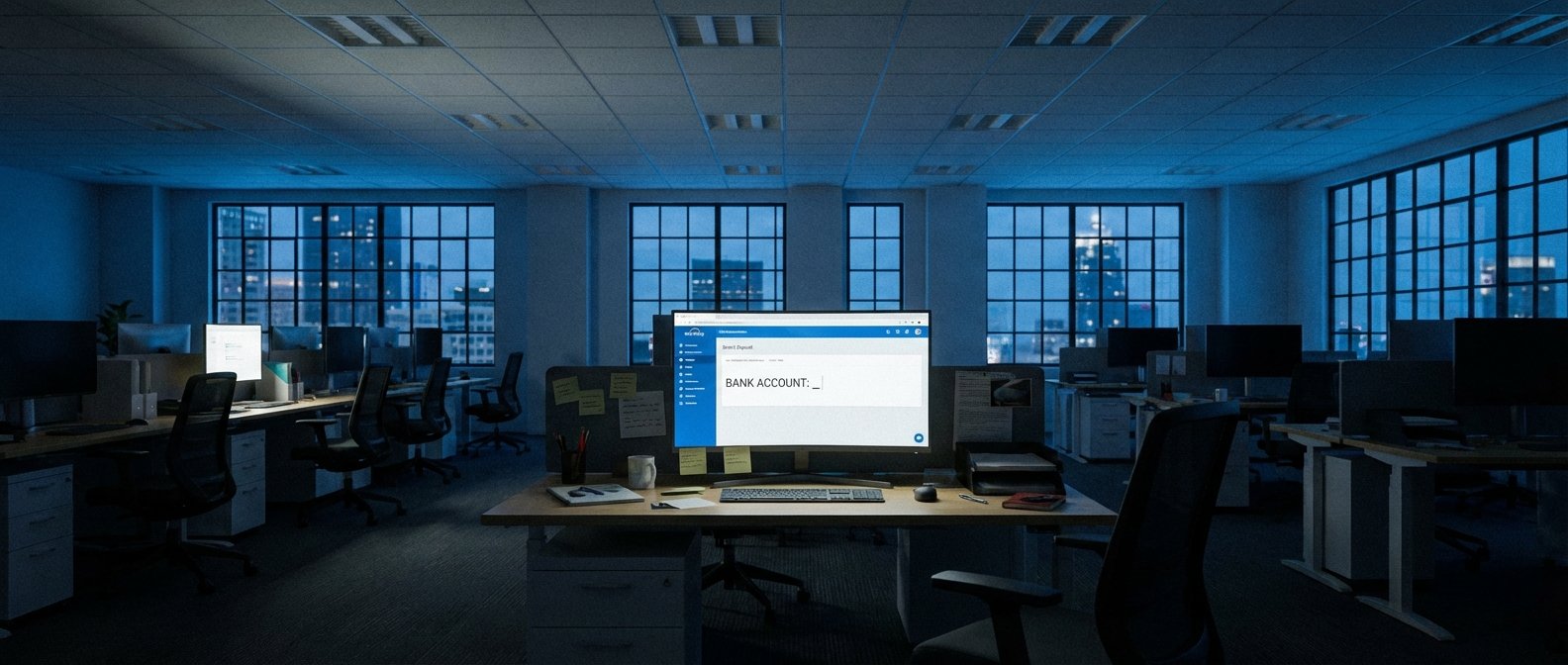
Storm-2755 (“Payroll Pirate”) runs a clean AiTM operation against Microsoft 365 users. It doesn’t steal credentials. It steals session tokens after MFA has already passed. That’s not a password problem. MFA doesn’t catch it. Once they have the session, they pivot to Workday, create inbox rules to suppress payroll notifications, and quietly reroute the victim’s direct deposit. The victim goes to work. Gets paid. Into someone else’s account. Weeks later, when rent doesn’t clear, they find out.
Operation Atlantic, led by the NCA, identified 20,000 cryptocurrency fraud victims across the UK, US, and Canada in a single week. Twelve million frozen. Forty-five million tracked globally. Blockchain analytics making it possible to move at scale.
And MITRE released F3, the Fight Fraud Framework, on April 10. ATT&CK for financial fraud. Open source, on GitHub, covering the full lifecycle from synthetic identity fraud to money mules. Built with real industry participation from day one. The security industry has had a common language for intrusions for a decade. Fraud has never had that. Until now.
Why these three stories form one picture, and what the Storm-2755 control gap means for M365 shops