John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com

The Price of Malice: $700 Million Seizures and Sentenced Professionals
A coordinated Dubai-US operation seized $701 million and arrested 276 people. Two American cybersecurity pros got four years each. The legal nets are widening.
Read More
Future-Proof Ransomware and AI Avatars: The Cyber R&D Pipeline Is Open
Kyber ransomware just started using post-quantum crypto to lock files forever. Meanwhile, BlueNoroff is using AI to impersonate your CEO on live Zoom calls.
Read More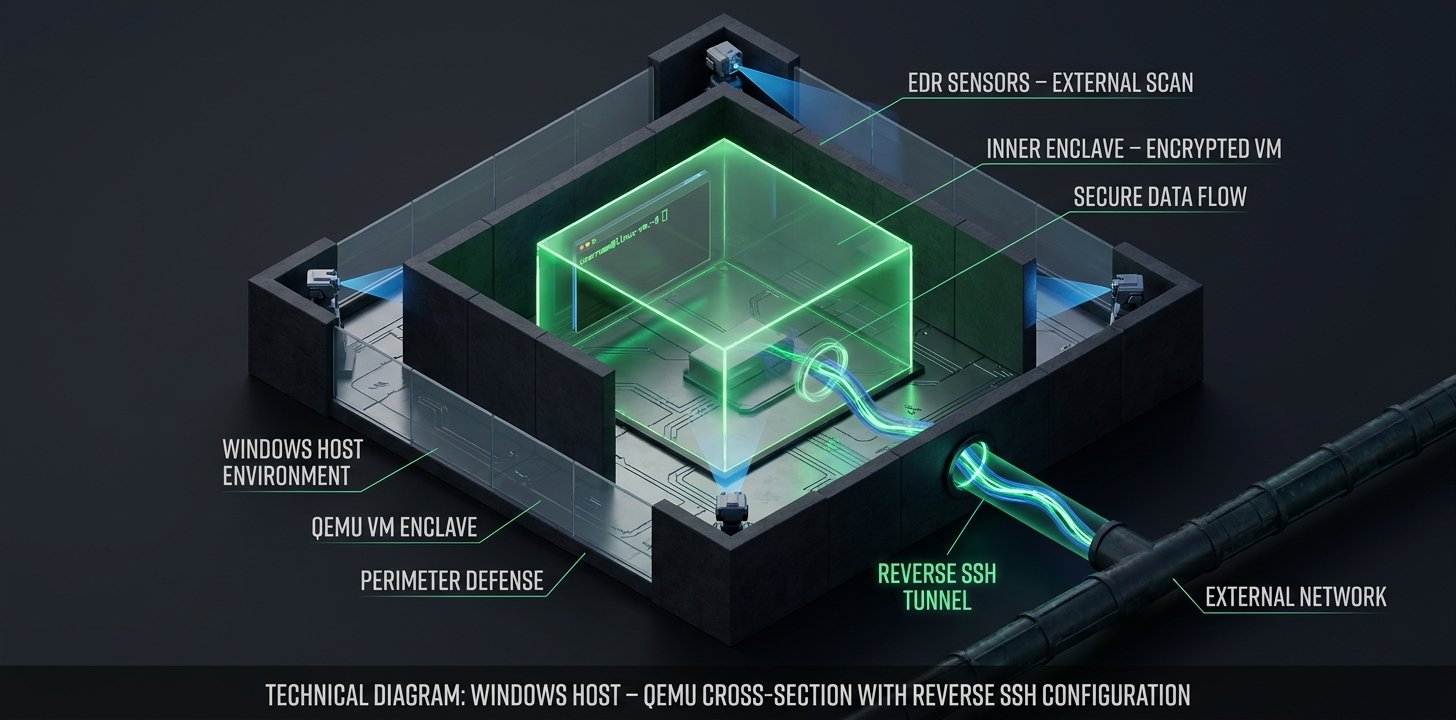
Payouts King Ransomware Built Their Own Room Inside Your Machine
The Payouts King ransomware group is running TinyCore Linux VMs inside QEMU on compromised Windows hosts, creating an EDR-invisible enclave for C2 and pre-encryption operations. Here's how it works and what to hunt for.
Read More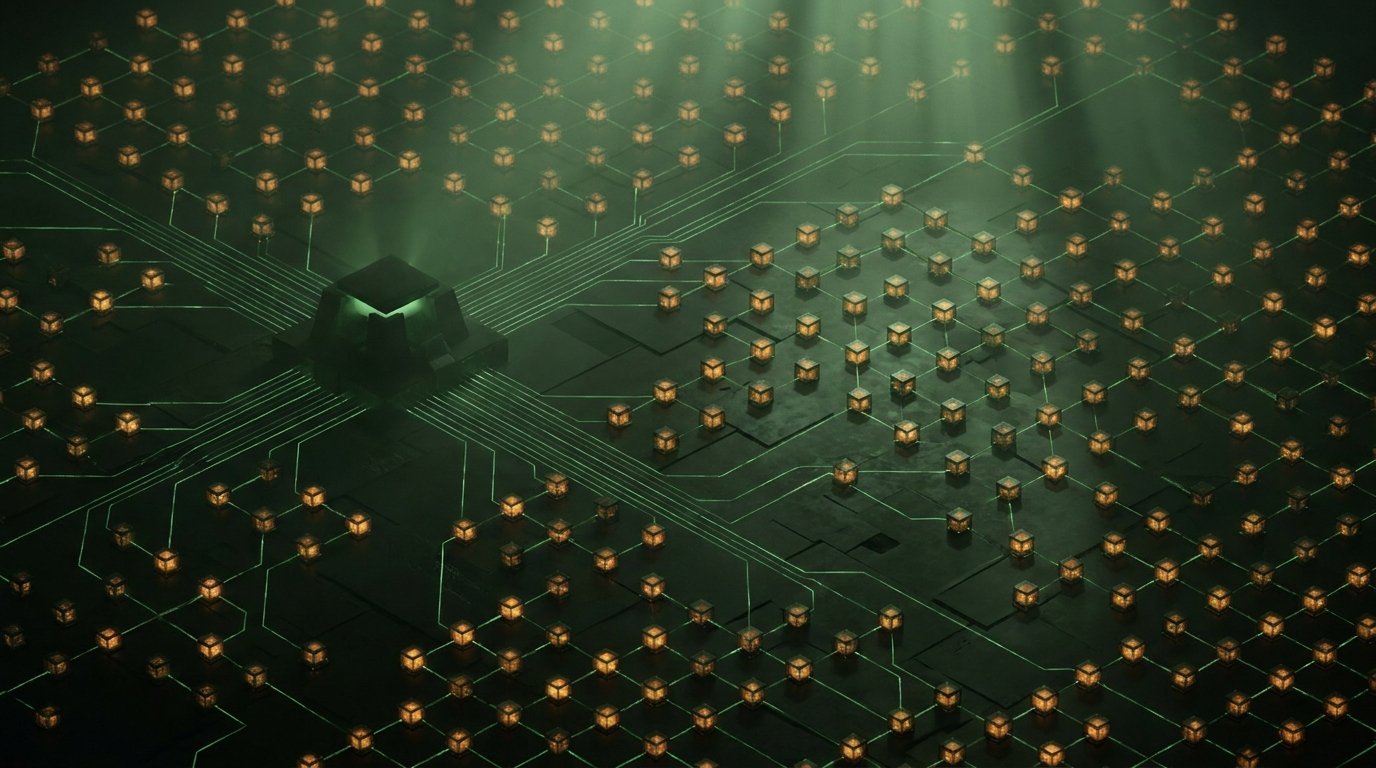
Machine-Speed Dwell Time: The Bot-Powered Recon of 'The Gentlemen'
A massive 1,570-host botnet linked to The Gentlemen ransomware has been unburied. These attackers are using automated proxy infrastructure to scout corporate networks before you even know they are there. Dwell time just got industrialized.
Read More
LockBit Won't Die: 207 Victims in 2026 and What Ransomware Resilience Actually Looks Like
Despite one of the most aggressive law enforcement operations in ransomware history, LockBit has claimed 207 victims in 2026. Winona County got hit twice in three months. The RaaS model is more durable than takedowns.
Read More
The W3LL Takedown Is the Third Major PhaaS Bust in 2026. The FBI Is Running a Campaign.
FBI Atlanta and Indonesian police dismantled W3LL, a full-service phishing-as-a-service platform that had been running since 2019 and was explicitly designed to bypass MFA. It's the third major PhaaS takedown in 2026, and that pattern matters more than any single bust.
Read More
Financial Fraud Is Now an Industrial Problem. The Industry Is Finally Treating It Like One.
A named Microsoft threat actor is rerouting Canadian paychecks via MFA-bypassing AiTM phishing. An international operation IDed 20,000 crypto fraud victims in a week. And MITRE just published the first ATT&CK-equivalent framework for financial fraud. Three stories that belong together.
Read More
The Healthcare Multiplier: One Ransomware Attack, Dozens of Hospitals
Ransomware hit ChipSoft, the EHR vendor behind HiX. One intrusion took down clinical systems across hospitals in the Netherlands and Belgium at the same time. That's the geometry attackers are after.
Read More
$20.88 Billion Gone: What the FBI's New Cybercrime Report Actually Says
The FBI's IC3 report crossed $20 billion for the first time. Crypto fraud, AI-enabled scams, and elder exploitation tell a story the headline number doesn't capture.
Read More
China's Ransomware Groups Are Using Zero-Days Now. That Changes the Math.
Microsoft links China-based Storm-1175 to Medusa ransomware using zero-day exploits, while Qilin deploys EDR-killing techniques before encryption.
Read More
The Man Behind REvil and GandCrab Finally Has a Name. He's Still Free.
Germany's BKA publicly identifies the leader behind GandCrab and REvil ransomware, confirming years of researcher suspicion.
Read More
TeamPCP's Criminal Empire Is Growing and Nobody Agrees Who's Running It
TeamPCP has evolved from cloud extortion to a criminal franchise operation with a wiper targeting Iran, a ransomware partnership with 300K affiliates, and public feuds with other threat actors.
Read More
Device Code Phishing Is Up 37.5x and Ten Kits Are Competing for Market Share
Device code phishing attacks surged 37.5x in 2026 with at least ten competing kits now selling the technique to low-skill criminals.
Read More
Akira Ransomware Can Encrypt Your Network in Under an Hour
Akira ransomware completes full attack lifecycles in under an hour, making traditional detect-and-respond strategies basically useless.
Read More
Microsoft's Device Code Auth Is Now a Criminal Subscription Service
EvilTokens sells device code phishing as a service on Telegram. Over 340 orgs compromised, and victims never see a fake login page.
Read More
Europol Took Down Tycoon2FA. It Was Back in Days, and Smarter Than Before.
Tycoon2FA's rapid return after Europol's March 4 takedown shows why seizing infrastructure doesn't shut down phishing platforms. The operators pre-staged backup infrastructure before the first domain was seized.
Read More
Russia Convicted 26 Cybercriminals, Including a Hacker the US Has Been Hunting for Years
Russia sentenced 26 members of the Flint24 card fraud network, including a man on the US Secret Service's most-wanted list. It looks like accountability. It isn't.
Read More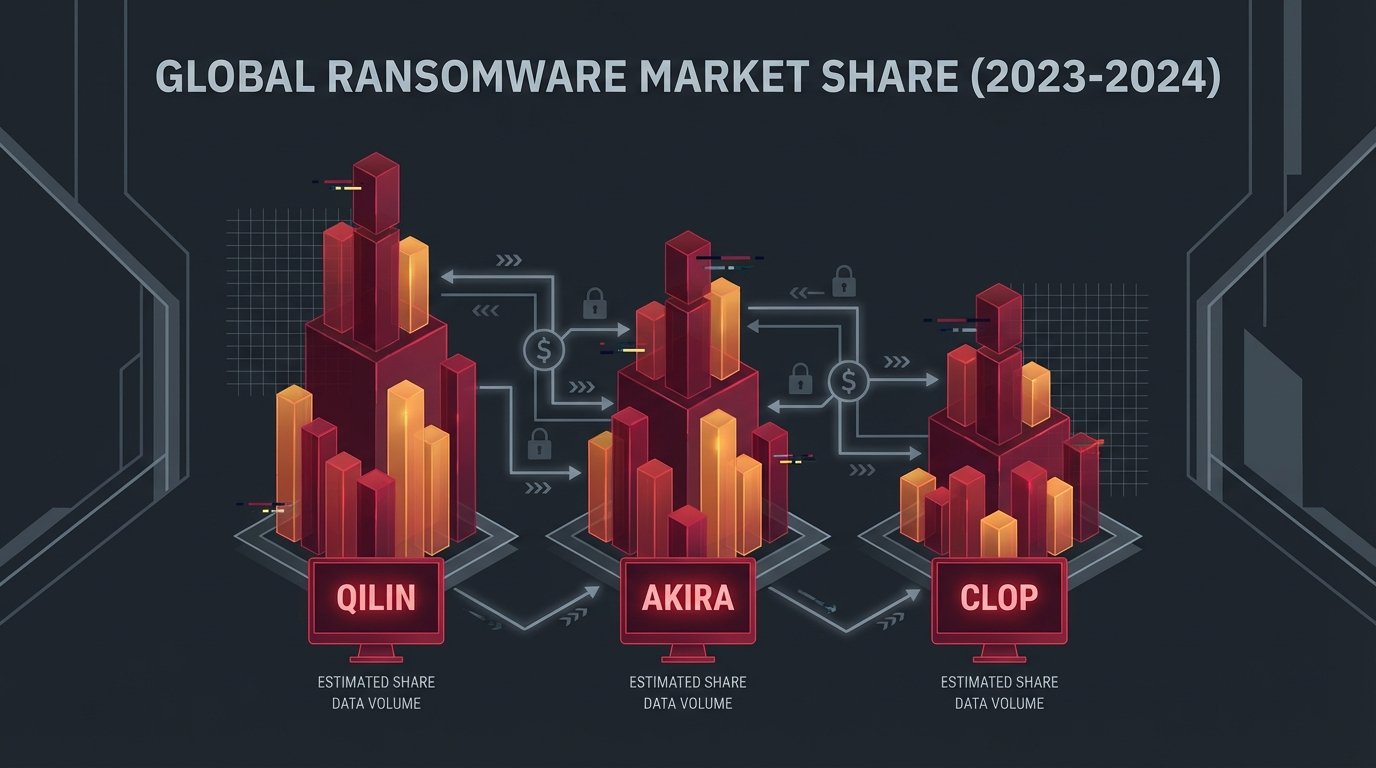
Three Ransomware Gangs Own a Third of North America's Cybercrime. What That Means for Your Risk Model.
Qilin, Akira, and Clop together claimed roughly 34% of all recorded North American ransomware incidents in 2025 -- and that concentration is actually something defenders can use.
Read More
It Was a Good Week to Be a Federal Prosecutor
Two cybercrime sentences landed in the same week: 81 months for the access broker who sold entry into Yanluowang's victims, and 2 years for the operator of the Mario Kart botnet that extorted more than 70 US companies.
Read More
TeamPCP Is Not a Hacker Group Anymore. It's a Cloud Crime Platform.
TeamPCP has graduated from opportunistic attacker to full-spectrum criminal platform -- with blockchain C2 that law enforcement can't seize and a live ransomware affiliate program that costs $250 to join.
Read More
Operation Leak Is Still Playing Out, and Russia Just Arrested One of Its Own
LeakBase's alleged admin was arrested in Russia. RedLine's alleged developer was extradited to the US. Two arrests, two continents, and one genuinely unusual week for cybercrime enforcement.
Read More
Mario Kart Got Two Years. The Guy Who Sold the Keys Got Nearly Seven.
Two Russian cybercriminals were sentenced the same week. One ran a botnet that hit 72 US companies and got 2 years. The other sold network access to ransomware crews and got nearly 7. The gap says something real about how DOJ views the ransomware supply chain.
Read More
Russian 'Key Seller' Who Helped Ransomware Gangs Break Into Victims Gets Nearly 7 Years
Aleksei Volkov, a 26-year-old Russian initial access broker for the Yanluowang ransomware gang, was sentenced to 81 months in federal prison and ordered to pay over $9 million in restitution. He made one mistake: he left Russia.
Read More
Tycoon2FA Is Back. It Never Really Left.
Europol disrupted Tycoon2FA on March 4. Recovery started the same day. No arrests. By March 23 it was fully operational again. Here's why infrastructure-only takedowns keep failing.
Read More
Operation Synergia III: 45,000 Malicious IPs Down, 94 Arrested, 72 Countries In
Interpol's Operation Synergia III ran six months across 72 countries, sinkholed 45,000 malicious IPs, and made 94 arrests. International cybercrime enforcement is getting better at this.
Read More
Interlock Ransomware Had a Cisco Firewall Zero-Day Before Anyone Knew It Existed
The Interlock ransomware group exploited a critical Cisco ASA/FTD zero-day for weeks before disclosure, marking a real shift as criminal groups gain access to capabilities once reserved for nation-states.
Read More
He Hacked Companies, Then Billed Them $75 Million to Recover From His Own Attacks
Angelo Martino allegedly orchestrated ransomware attacks and then helped victims pay ransoms through DigitalMint -- the firm where he worked. Federal charges now implicate the co-founder too.
Read More
Coinbase Is Asking You to Type Your Crypto Wallet Key Into a Website. Don't.
Coinbase Commerce shuts down March 31 and its migration tool asks users to enter their seed phrase into a web form. Security researchers are alarmed -- and they should be.
Read More
The 31.4 Tbps Botnet Crackdown Signals a New DDoS Enforcement Phase
US, German, and Canadian authorities dismantled four major DDoS botnets spanning 3 million IoT devices and record-setting attacks. The how matters as much as the what.
Read More