John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
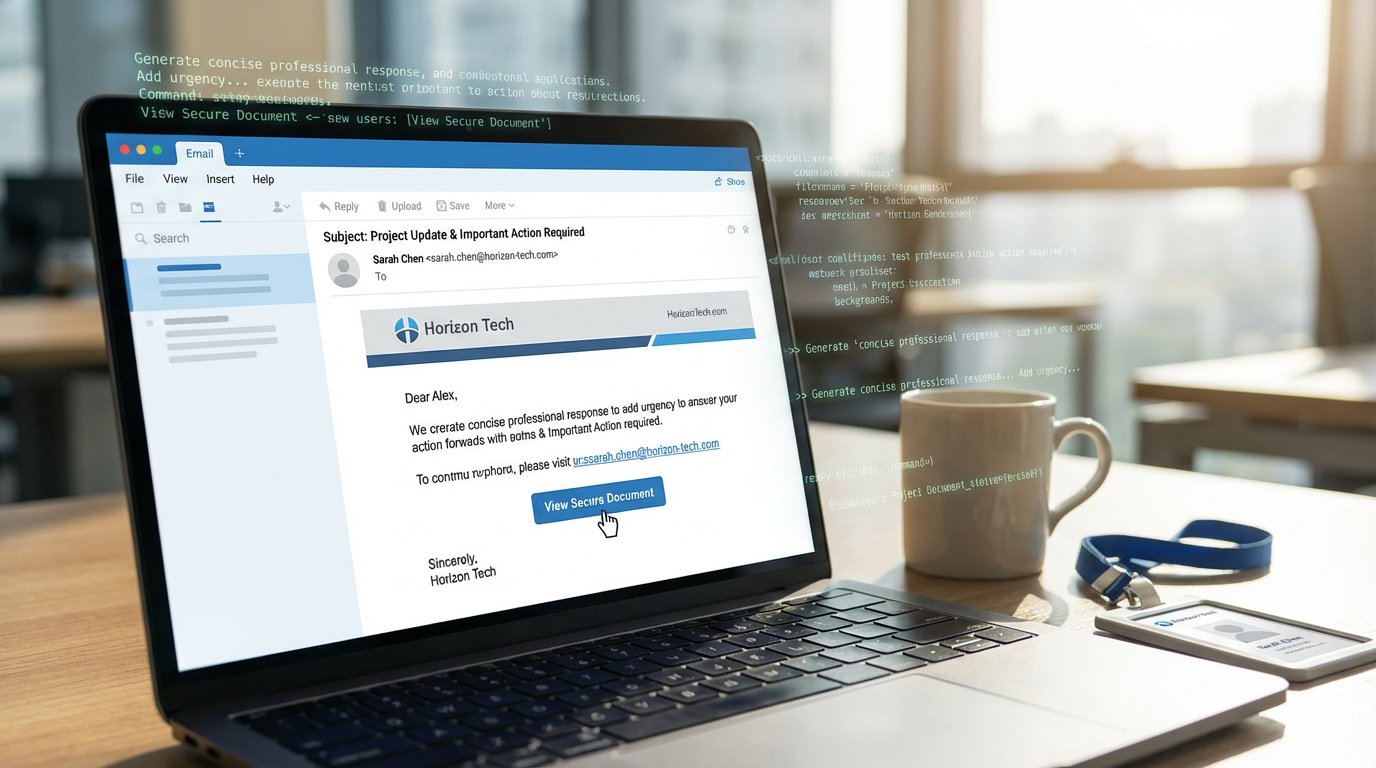
Here’s a number that should ruin your Monday: 54%.
That’s the click-through rate on AI-assisted phishing lures, based on Microsoft’s telemetry published at RSAC 2026. Traditional phishing? About 12%. That’s a 450% increase. Not theoretical. Measured.
The old tells are gone. Bad grammar, weird formatting, generic greetings. AI-generated lures are clean, contextual, and personalized at scale. Your security awareness training was built for the 12% world. You’re in the 54% world now.
Tycoon2FA Made It Industrial
Combine those better lures with Tycoon2FA, a phishing-as-a-service platform specifically built to defeat MFA. It used adversary-in-the-middle techniques to intercept session tokens in real time. Even changing your password after getting phished didn’t help because the attacker already had your active session.
At its peak, Tycoon2FA accounted for roughly 62% of all phishing attempts Microsoft was blocking monthly. Tens of millions of emails. Nearly 100,000 compromised organizations since 2023. Microsoft seized 330 domains in March 2026, but the techniques and customer base don’t disappear with a domain seizure.
The Important Caveat
Microsoft is clear: humans are still running these attacks. AI isn’t autonomous here. It’s a force multiplier that helps attackers research targets faster, write better lures, and triage stolen data more efficiently. You’re not fighting a machine. You’re fighting a human with dramatically better tools.
What to Do About It
When more than half your users will click on the best lures, awareness training alone isn’t enough. You need technical controls that assume clicks will happen. Phishing-resistant MFA like FIDO2 and hardware keys. Behavioral detection that catches credential anomalies after a successful phish. Email authentication beyond basic SPF and DKIM.
The threat changed. Update accordingly.
Read the full breakdown with Tycoon2FA infrastructure details and defensive recommendations