John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com

The Visible Hand: How AI is Already Breaking the Security Model
Central banks are panicking over unreleased AI models while hackers are already using them to backdoor Hugging Face and close $100k crypto heists. The weaponized AI era is officially here.
Read More
The Attack Isn't Coming From a Stranger. It's Coming From Your GitHub Notifications.
Four active campaigns documented today share one design principle: the attack arrives from something the target already trusts. APT37 builds friendships on Facebook first. Attackers abuse GitHub and Jira notifications to deliver phishing links that pass SPF, DKIM, and DMARC. A fake rocket alert app spies on people in a conflict zone. AI-generated articles seed Google Discover with scareware.
Read More
The W3LL Takedown Is the Third Major PhaaS Bust in 2026. The FBI Is Running a Campaign.
FBI Atlanta and Indonesian police dismantled W3LL, a full-service phishing-as-a-service platform that had been running since 2019 and was explicitly designed to bypass MFA. It's the third major PhaaS takedown in 2026, and that pattern matters more than any single bust.
Read More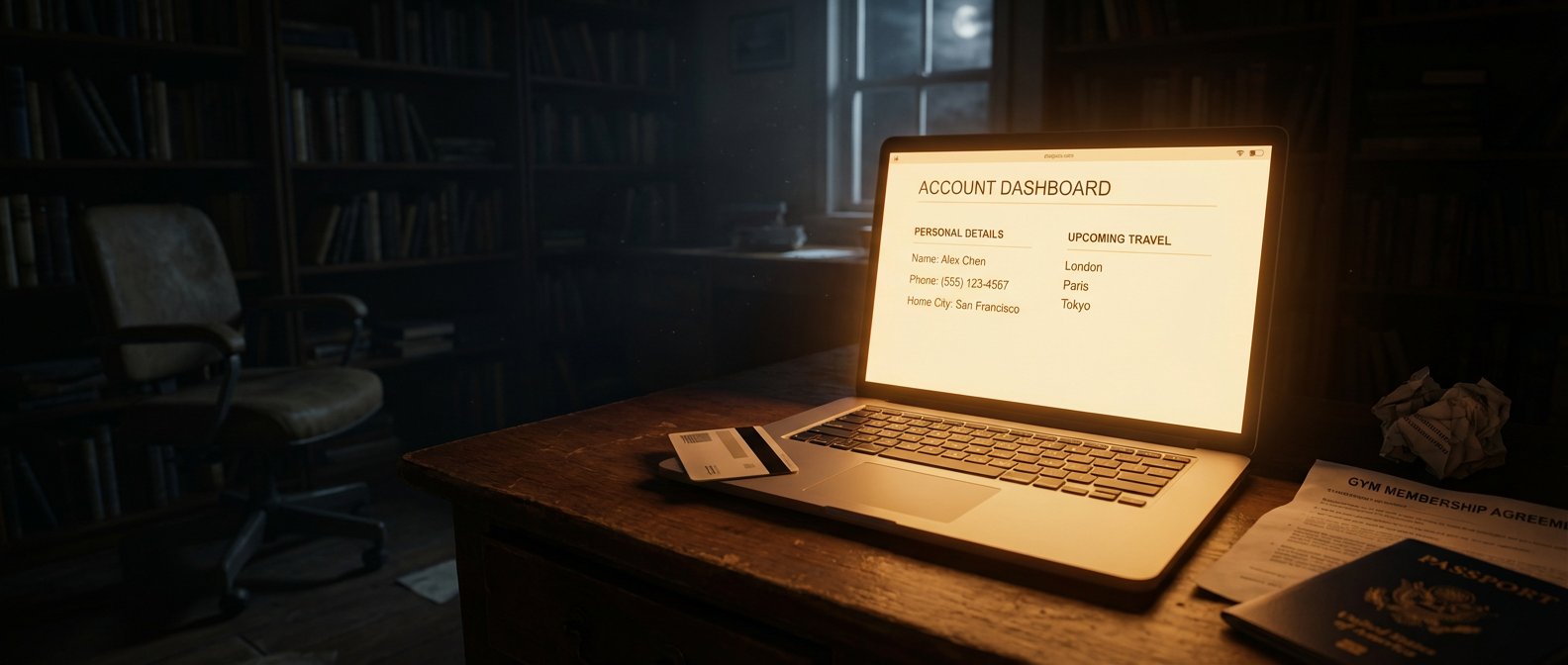
They Didn't Get Your Password. They Got Everything Else.
Booking.com forced PIN resets. Basic-Fit disclosed a breach hitting roughly one million EU gym members. No passwords were stolen, both companies say. That's not the reassurance it sounds like.
Read More
MFA Isn't the Final Barrier Anymore. It Hasn't Been for a While.
Three research teams this week documented MFA failures at login, at the helpdesk layer, and post-session. The answer isn't more MFA. It's hardware-bound authentication.
Read More
China's TA416 Is Back in Europe After Two Years. They Brought New Tricks.
TA416 has resumed targeting EU government and diplomatic organizations with PlugX malware, now abusing OAuth redirects to slip past traditional phishing defenses.
Read More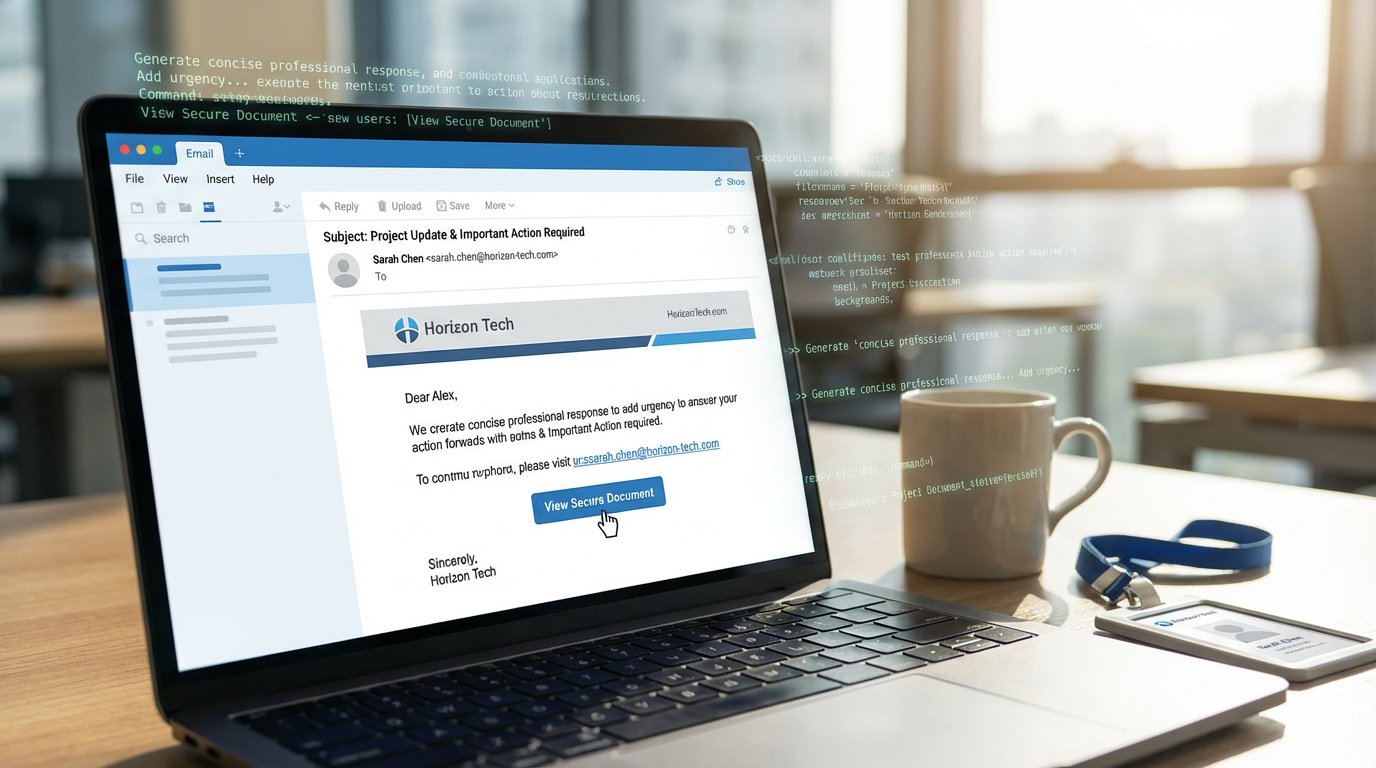
AI-Written Phishing Emails Get Clicked 450% More Often. The Data Is In.
Microsoft telemetry shows AI-assisted phishing lures hit a 54% click-through rate versus 12% for traditional campaigns, a 450% increase that breaks conventional security awareness training.
Read More
Microsoft's Device Code Auth Is Now a Criminal Subscription Service
EvilTokens sells device code phishing as a service on Telegram. Over 340 orgs compromised, and victims never see a fake login page.
Read More
Hackers Impersonated Ukraine's CERT to Push Malware as a 'Security Tool'
Pro-Russia group Cyber Serp sent fake CERT-UA emails carrying a RAT disguised as a protection tool. They claimed 200K infections. Reality was a handful.
Read More
Europol Took Down Tycoon2FA. It Was Back in Days, and Smarter Than Before.
Tycoon2FA's rapid return after Europol's March 4 takedown shows why seizing infrastructure doesn't shut down phishing platforms. The operators pre-staged backup infrastructure before the first domain was seized.
Read More
Thirty Seconds. That Is All FAUX#ELEVATE Needs to Own an Enterprise Machine.
FAUX#ELEVATE skips consumer targets entirely, checks for corporate domain membership first, then steals Chrome credentials and starts mining Monero in about 30 seconds.
Read More
Your MFA Isn't Enough. (And Most Places Don't Even Have That.)
A phishing campaign bypassed MFA at 340+ organizations using legitimate OAuth flows, while 76% of companies are still relying on passwords in the first place.
Read More
340+ Organizations Hit by M365 Phishing That Bypasses MFA Without Touching Your Password
A device code OAuth phishing campaign has compromised 340+ organizations since February 2026, bypassing MFA and surviving password resets. It's still running.
Read More
Operation Synergia III: 45,000 Malicious IPs Down, 94 Arrested, 72 Countries In
Interpol's Operation Synergia III ran six months across 72 countries, sinkholed 45,000 malicious IPs, and made 94 arrests. International cybercrime enforcement is getting better at this.
Read More
Two Tools Published This Week Just Broke Chrome's Encryption and Bypassed Your MFA
VoidStealer cracked Chrome's Application-Bound Encryption via a debugger trick, while Astaroth defeats SMS, TOTP, and push MFA in real time -- and the only method that survives both is FIDO2.
Read More
Coinbase Is Asking You to Type Your Crypto Wallet Key Into a Website. Don't.
Coinbase Commerce shuts down March 31 and its migration tool asks users to enter their seed phrase into a web form. Security researchers are alarmed -- and they should be.
Read More
Your Encrypted Chat Is Fine. Your Trust Model Isn't.
The FBI and CISA warn that Russian intelligence compromised thousands of Signal and WhatsApp accounts -- not by breaking encryption, but by tricking users into handing over access. Here's what that means and what to do.
Read More
Attacker Scale in 2026: Botnets, EDR Killers, and Phishing-as-Operations
From BYOVD-based EDR suppression to tax-season phishing pipelines and botnet disruption, attacker scale now comes from operational integration, not one breakthrough trick.
Read More
Your Data This Week: Starbucks Employee Breach, Loblaw Customer Data, Steam Malware, and How to Respond to Each
Three breaches hit this week through platforms people already trust. Starbucks employee data, Loblaw customer accounts, and FBI-flagged malware hiding in Steam games.
Read More
INTERPOL Just Sinkholed 45,000 Criminal IPs and Arrested 94 People Across 72 Countries
Operation Synergia III was one of the biggest cybercrime infrastructure takedowns ever. 45,000 malicious IPs redirected, 94 arrests, 72 countries involved. Here's what that actually means.
Read More
Your MFA and Your ZIP Scanner Both Have Blind Spots Attackers Are Already Using
Adversary-in-the-Middle phishing beats standard MFA in real time. Zombie ZIP tricks archive scanners into waving malware through. Two trusted security controls, two systematic bypasses already in the wild.
Read More
BlackSanta Kills Your EDR Before You Even Know You're Hit — and It's Coming Through HR
New malware called BlackSanta disables your endpoint detection, and it's getting in through HR inboxes. That combo is nastier than it sounds.
Read More
ClickFix Is the Social Engineering Trick That Took Over 2026
A dead-simple social engineering trick is showing up everywhere in 2026. Users paste a command into PowerShell or a Run dialog and boom, malware runs. Three separate campaigns hit this week alone.
Read More