John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
Two companies, one week. Booking.com quietly forced PIN resets after unauthorized access to reservation data. Basic-Fit, Europe’s largest budget gym chain, disclosed a breach affecting roughly one million members across Belgium, Netherlands, Luxembourg, France, Spain, and Germany. Exposed data includes bank account details, names, dates of birth, and contact info.
Neither breach involved stolen passwords. Both companies say they responded quickly. On paper, that sounds fine.
Here’s why it isn’t.
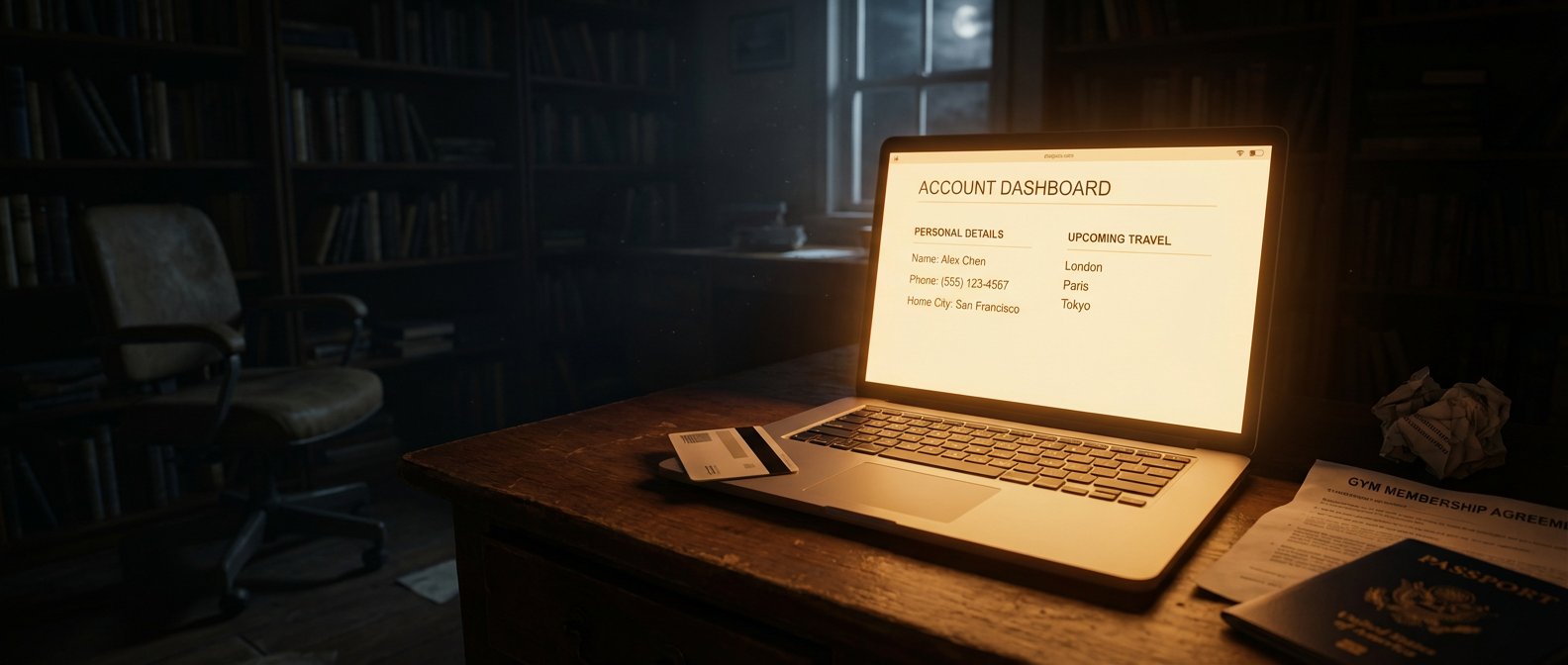
“No passwords stolen” is the metric attackers doing credential stuffing care about. Attackers running fraud calls and social engineering schemes care about something else entirely. Your name. Your booking reference. Your check-in dates. Your gym membership tied to a bank account. That’s not the key to your front door. It’s enough to make a convincing knock.
The Booking.com fraud pattern is well-documented at this point. Someone calls claiming to be customer support, says there’s a payment issue with your upcoming reservation, and asks you to confirm the card on file. They already know your destination, your hotel, your dates. It sounds completely legitimate. It isn’t.
The Basic-Fit version runs through SMS. A message arrives about a direct debit problem, knows your name, knows you’re a member, asks you to update your banking details via a link. That link goes somewhere it shouldn’t.
One million people. Six countries. GDPR’s 72-hour notification windows in play across multiple jurisdictions. The breach is the event. The fraud window it opens is the actual problem.
If you have an active Booking.com reservation: verify anything through the app directly, not through inbound calls or links. If you’re a Basic-Fit member in an affected country: ignore any SMS or email about billing problems. Go to the app or official site yourself.
Basic advice, genuinely worth following.
Read the full breakdown of how this fraud pattern works and what to watch for.