John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com

The Infrastructure House of Cards: Vercel, cPanel, and Outsourced Risk
Managed hosting is great until it isn't. This week cPanel got bypassed, Vercel leaked 100,000 .env secret files, and Virtualizor handed over the keys to your VPS.
Read More
The Printing Provider Pivot: Concentration Risk Hits US Banks
Citizens Bank and Frost Bank customers had their data stolen through outsourced printing and tax fulfillment vendors. Everest ransomware is targeting the boring middle layer.
Read More
The Billion-Dollar Bill: Why the Cost of a Breach Never Ends
A major breach cycle only lasts a week in the news but can last five years on the balance sheet. UnitedHealth spent $3.1 billion before the SEC fine even landed.
Read More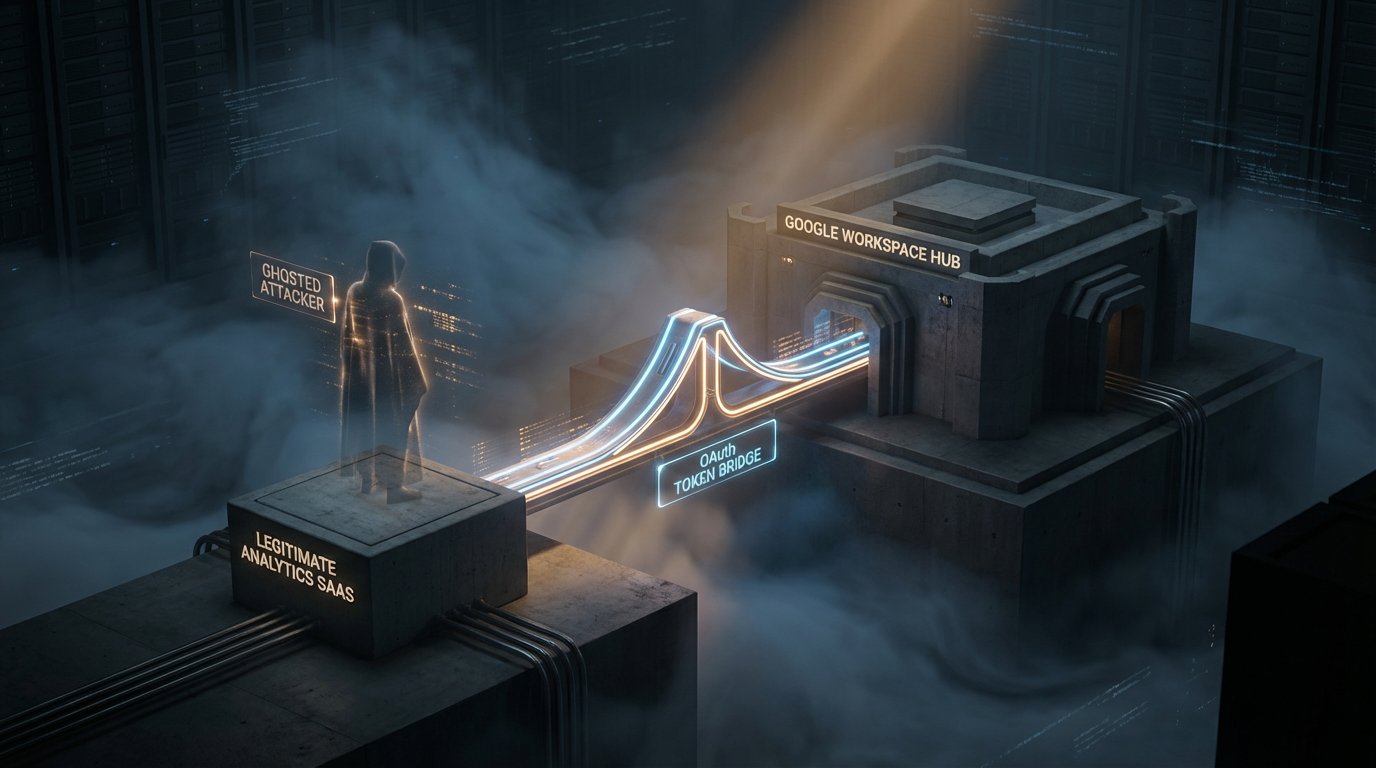
The 22-Month Window: How Vercel's Upstream Analytics Bridge Was Compromised
Vercel recently disclosed a major security incident via Context.ai that began in June 2024. For nearly two years, an invisible door was held open into the core of their cloud identity. It is a masterclass in the hidden risks of 'harmless' SaaS analytics.
Read More
The Megaleak Stage: Why the Standard Bank Breach is 2026's Scariest Proof-of-Failure
Standard Bank South Africa's breach just hit the 154-million-row stage. This is no longer an investigation. It is a permanent intelligence library for identity thieves. When negotiations fail, the consumer picks up the bill.
Read More
The Checkbook Crisis: How Small-Town Cyber-Heists Hit Your Property Tax
A cyberthief tricked a small New Jersey town out of millions with just a phone call. Now, the homeowners are paying for it on their tax bills. This is what happens when cybersecurity becomes a line item on your property assessment.
Read More
Smart Ships, Dumb Attack Surface
Maritime cyber incidents doubled in 2025. Attackers are now fabricating commands through satellite links. When the network goes down, the ship goes with it.
Read More
When the Breach Isn't at Your Bank: Third-Party Risk Hits Healthcare and Finance in the Same Week
A hospital email account, a fintech ransomware attack still sending notifications eight months later, and a Lapsus$ claim against a financial vendor. Third-party concentration risk landed in two sectors at once this week.
Read More
Two Breaches Today. One Was Careful. One Was a Unlocked Door. Both Were Catastrophic.
ShinyHunters dumped 78.6 million Rockstar records after the ransom deadline expired. They never touched Rockstar directly. They went through a cloud analytics vendor. Meanwhile, a French email provider left an Elasticsearch cluster open to the internet and exposed 40 million records across L'Oreal, Renault, and French government embassies.
Read More
The Breach Happened in February 2025. Patients Are Just Hearing About It Now.
DermCare Management, which handles billing and records for dozens of dermatology practices, suffered a breach in February 2025. They confirmed it in March 2026. Patients are getting notified now. The exposed data includes Social Security numbers, financial account info, and medical records.
Read More
They Didn't Get Your Password. They Got Everything Else.
Booking.com forced PIN resets. Basic-Fit disclosed a breach hitting roughly one million EU gym members. No passwords were stolen, both companies say. That's not the reassurance it sounds like.
Read More
The LAPD Was Not Hacked. But 7.7 Terabytes of Its Data Leaked Anyway.
World Leaks didn't touch LAPD's network. They breached a third-party file-sharing app connected to the LA City Attorney's Office that apparently had no password protecting it. 337,000 files including Internal Affairs records and witness names are now in an extortion group's hands.
Read More
A Hacker Claims the Biggest Military Breach in History. Experts Think It Might Be Real.
FlamingChina claims to have stolen 10 petabytes from China's National Supercomputing Center in Tianjin, including missile schematics and weapons testing data. CNN showed samples to cybersecurity experts. They declined to dismiss it. This has not been confirmed.
Read More
Syria's Government Got Hacked. The Method Was Probably 'No Password Policy.'
Multiple Syrian government X accounts fell at the same time in March 2026. The likely method wasn't a sophisticated attack. It was shared credentials and no MFA. Your organization has a version of this story too.
Read More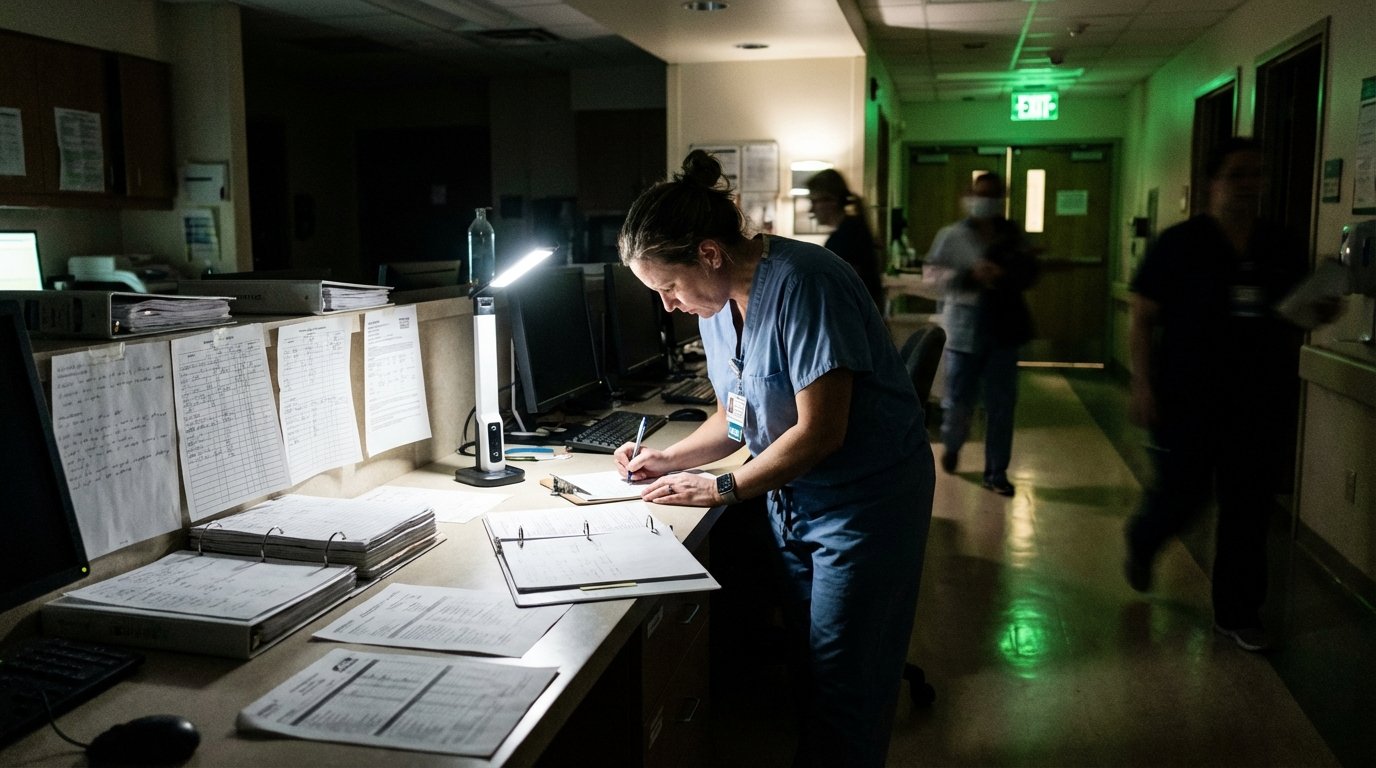
A Massachusetts Hospital Is Diverting Ambulances and Cancelling Chemo. The Attacks You Haven't Heard About Are Worse.
Brockton Hospital is running on paper after a cyberattack forced ambulance diversions and chemo cancellations. Health ISAC says multiple undisclosed incidents are hitting healthcare right now.
Read More
The AI Training Pipeline Just Became a High-Value Target
A trojanized LiteLLM package hit Mercor, the AI training vendor shared by OpenAI, Anthropic, and Meta, exposing the massive concentration risk in the AI supply chain.
Read More
TeamPCP Hacked the European Commission Through a Security Scanner
TeamPCP breached the European Commission via a poisoned version of Trivy. Data from 30+ EU entities got exposed. ShinyHunters leaked it all. The irony of a security tool being the attack vector writes itself.
Read More
One IT Admin Locked 254 Servers. T-Mobile Lost Another Insider. Same Day.
A Kansas City engineer held his employer hostage for 20 bitcoin while T-Mobile quietly filed yet another insider breach. Privileged access is still the hardest problem in security.
Read More
ShinyHunters Popped a Telehealth Giant Through Its Help Desk
Two employees tricked out of their Okta creds. Millions of telehealth support tickets stolen. And Hims says no medical records were exposed. Sure.
Read More
LA Metro Is Still Rebuilding 1,400 Servers After a March Cyberattack
Two weeks after detecting unauthorized access, LA Metro is checking 1,400 servers one by one. WorldLeaks claims 160GB stolen. Trains and buses never stopped.
Read More
FBI Says China Hacked Its Surveillance Systems, Triggers 'Major Incident' Classification
The FBI classified a suspected Chinese intrusion into law enforcement surveillance infrastructure as a FISMA major incident, forcing Congressional notification within days.
Read More
Drift Protocol Lost $285M Because Two People Signed the Wrong Thing
Attackers social-engineered two multisig signers and used Solana's durable nonce feature to pre-sign transactions that drained Drift Protocol. No code exploit needed.
Read More
TeamPCP's First Confirmed Victim Lost Passport Scans and Video Interviews
AI hiring platform Mercor confirmed a breach tied to the LiteLLM compromise. The stolen data includes passport scans and video interviews you can't exactly rotate like a password.
Read More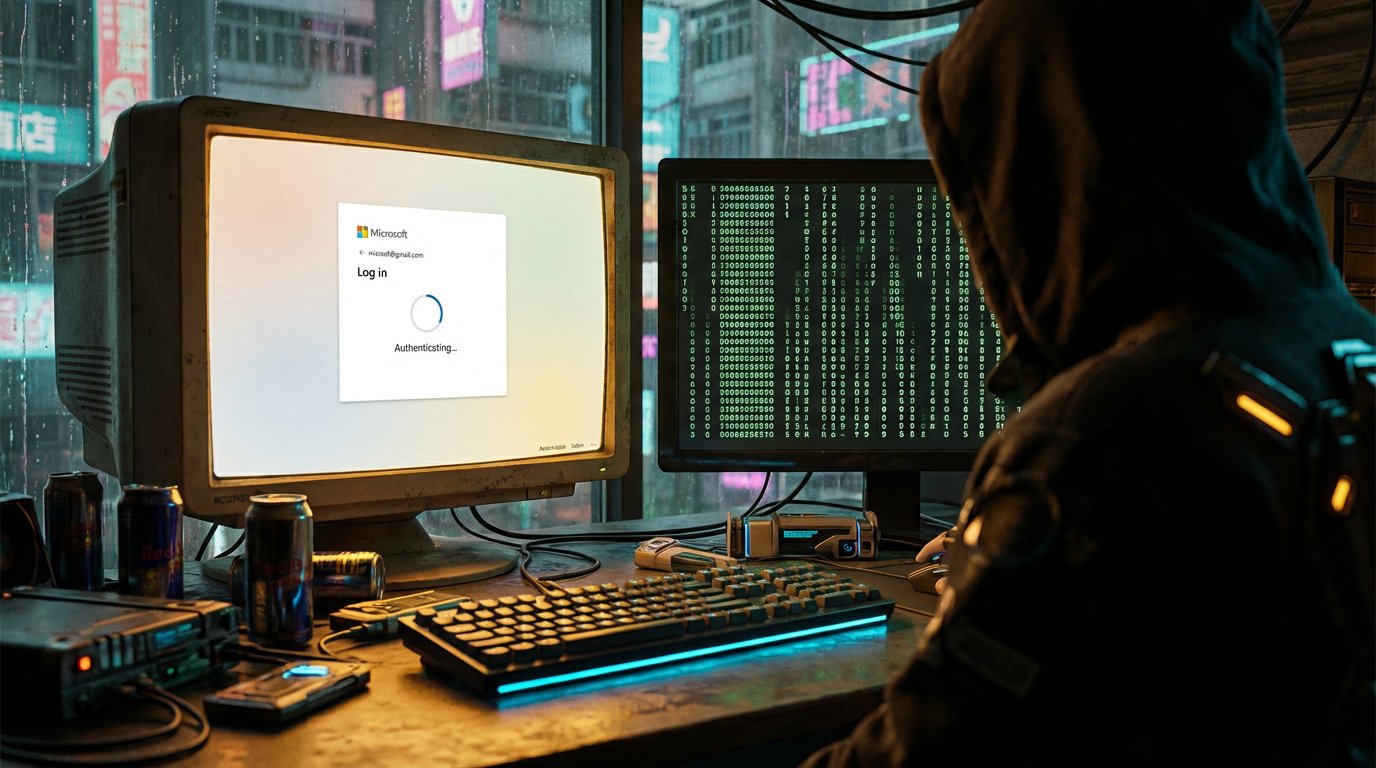
Your MFA Isn't Enough. (And Most Places Don't Even Have That.)
A phishing campaign bypassed MFA at 340+ organizations using legitimate OAuth flows, while 76% of companies are still relying on passwords in the first place.
Read More
Healthcare Had a Bad Week. A Really, Really Bad Week.
Three healthcare breaches in one week, all tracing back to the same problem: third-party vendors with access to patient data and not enough security around it.
Read More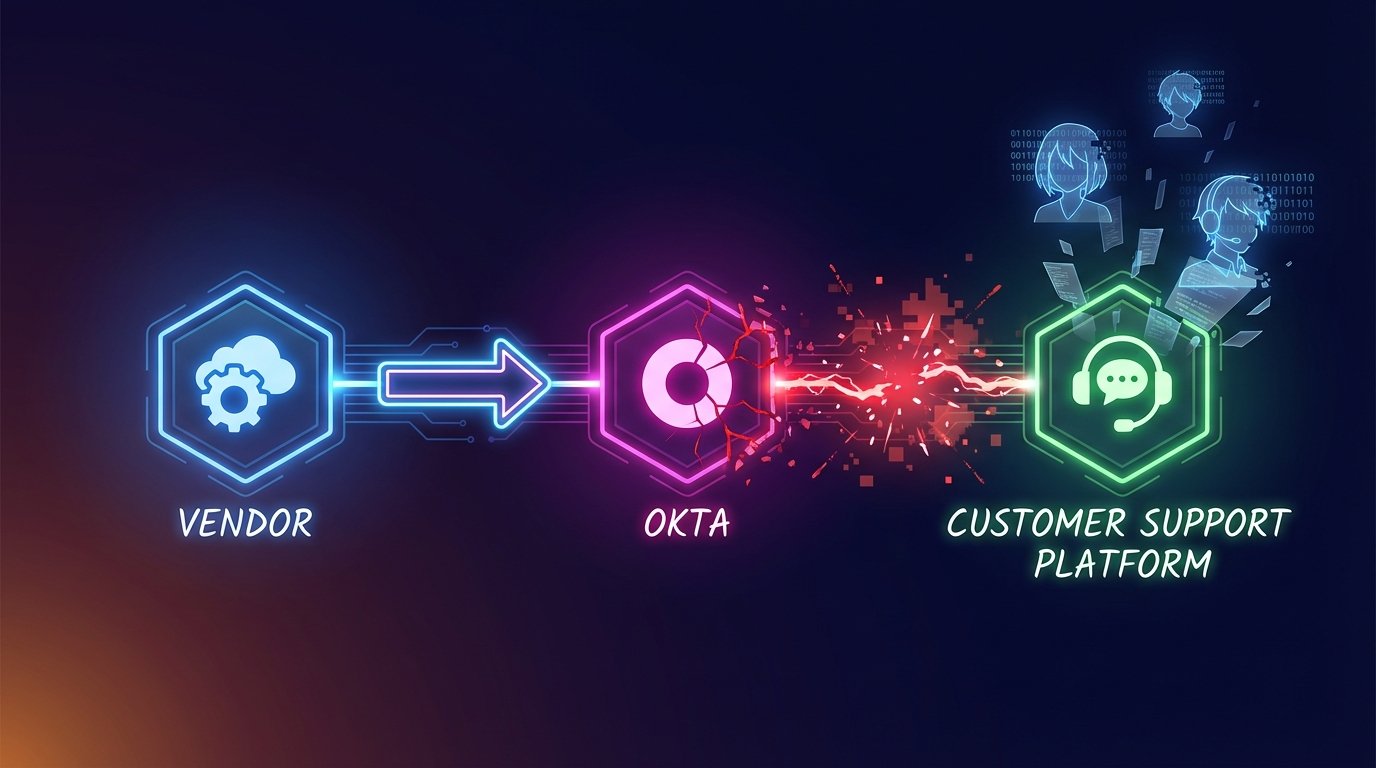
Crunchyroll Got Breached. Their Systems Were Never Touched.
6.8 million Crunchyroll users had their data stolen through a three-hop attack chain that went from a vendor's infected laptop through Okta into Crunchyroll's customer service platform, without ever touching Crunchyroll's own systems.
Read More
The Hack That Broke the Promise of Anonymity: 8 Million Crime Tips Stolen from P3 Intel
P3 Global Intel, which powers Crime Stoppers tip lines worldwide, was hacked. 8 million anonymous tips are now in criminal hands. The parent company still hasn't confirmed a thing.
Read More
Ransomware Hits Spain's Largest Fishing Port, Forcing Manual Operations
A ransomware attack knocked out digital systems at the Port of Vigo on March 24, 2026, forcing staff to revert to paper logs and phone calls. No group has claimed the attack.
Read More
Stryker Finds a Malicious File in Its Systems. Production Is Coming Back Online.
Stryker's forensic investigation with Palo Alto Networks Unit 42 found a malicious file used to run commands and conceal activity, a separate finding from the initial Handala attack. Production recovery is underway.
Read More
Hackers Claim an AstraZeneca Breach. Here's What We Know (Which Isn't Much Yet).
Lapsus$ is claiming they stole 3GB of AstraZeneca data including source code and credentials. AstraZeneca hasn't responded. Nothing's been independently verified. Here's why it's still worth watching.
Read More
Kaplan and Mazda Both Disclosed Breaches This Week. Both Happened Months Ago.
Kaplan's breach exposed SSNs for 173,000+ people in October 2025. Victims found out in March 2026. Mazda disclosed a December breach the same week. Both timelines are legal. That's the problem.
Read More
A Hack You Never Heard Of Just Stranded Thousands of People Who Had No Say in Any of It
A cyberattack on a court-ordered breathalyzer company left thousands of DUI-monitored drivers stranded and potentially facing legal consequences through no fault of their own.
Read More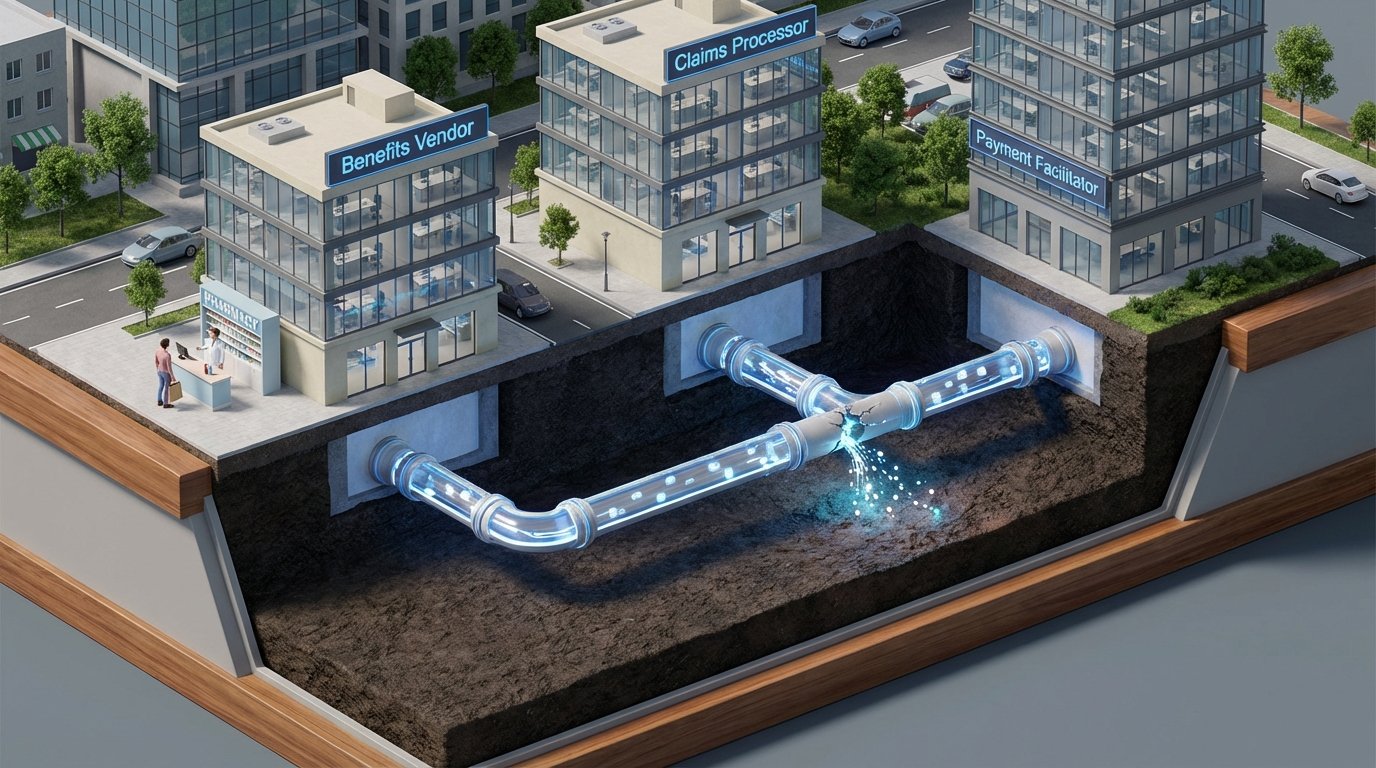
The Healthcare Benefits Breach You Haven't Heard About (or the One After It, or the One After That)
Three healthcare and benefits data breaches disclosed in the same week -- TriZetto (3.4M), Navia (2.7M), and Marquis (672K) -- follow the same disturbing pattern: your most sensitive data lives with vendors you've never heard of, and you find out months later.
Read More
An Identity Theft Protection Company Was Just Hacked by a Phone Scammer
Aura sells identity protection. A scammer called one employee, said the right things, and walked out with data on 900,000 people. The irony is real, but the lesson is bigger.
Read More
The Insider Front Door: How Legitimate Access Keeps Becoming Extortion
A data analyst extorted his employer for $2.5M using access his job gave him. Three Americans helped North Korean operatives infiltrate US companies as fake IT workers. Different crimes, same root problem.
Read More
Breach Impact Without a Single Archetype: Vendor, Insider, and Nation-State Pressure
Navia, Aura, an insider ransomware conviction, and Lazarus attribution show why breach readiness should be built around resilient process, not assumptions about attacker type.
Read More
Breach Disclosure Lag Is Becoming the Real Story in Financial Supply Chains
The Marquis breach started with a ransomware attack. The damage is still accumulating months later -- not because of what happened technically, but because of how disclosure was handled.
Read More