John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
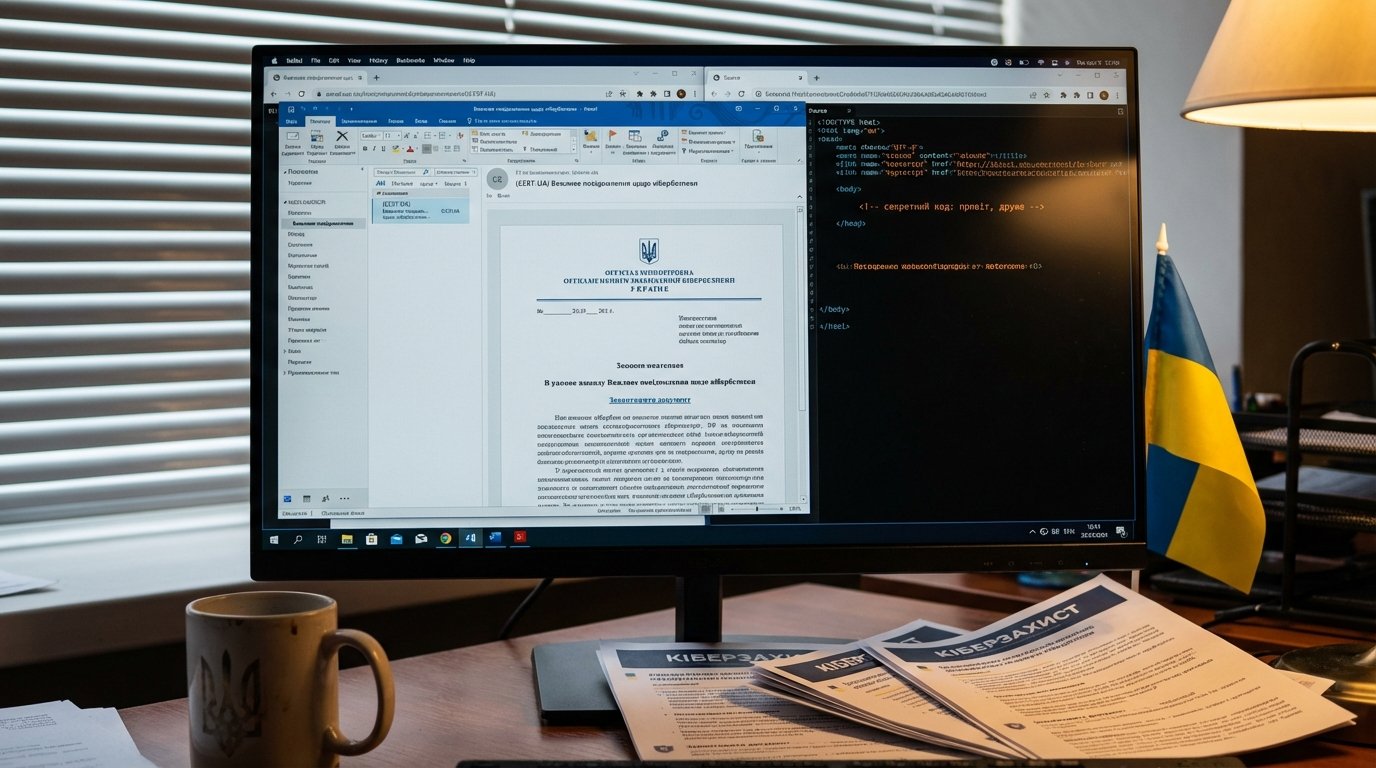
Pro-Russia hacktivist group Cyber Serp impersonated Ukraine’s CERT-UA and sent emails carrying malware disguised as a “protection tool.” The emails came from a lookalike domain (cert-ua[.]tech vs. the real cert.gov.ua) and linked to a password-protected ZIP on Files.fm containing AGEWHEEZE, a Go-based RAT.
The payload is capable enough: command execution, file manipulation, screenshots, clipboard grabbing, persistence through scheduled tasks and registry mods. They targeted state orgs, hospitals, universities, financial institutions, and security companies.
Then came the bragging. Cyber Serp hit Telegram claiming a million emails sent and 200,000 devices compromised. CERT-UA’s actual assessment? “Largely unsuccessful.” A handful of infections, mostly at educational institutions.
That gap matters. Hacktivist groups inflate numbers to recruit members and impress sponsors. Those claims get repeated uncritically all the time. Always check who’s counting.
The technique itself is the real story here. Impersonating a trusted national CERT flips the phishing dynamic. Victims aren’t clicking out of fear or greed. They’re clicking because they think their country’s security team told them to install something. They’re trying to do the right thing. That playbook works in any country. Swap the logo, change the domain, and you’ve got the same attack targeting CISA, NCSC, or BSI.
Defend against it the boring way: verify through official channels, flag lookalike domains in your email security, and treat password-protected ZIPs from unexpected sources as suspicious by default.