John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
Three stories landed this week that look unrelated. They’re not. Together they show how China operates across multiple domains at once: state-linked hackers buried in telecom backbone networks, Washington formally accusing Beijing of enabling industrial-scale fraud against American consumers, and the UK sanctioning a $20 billion Telegram marketplace that keeps the whole scam ecosystem running.
Three fronts. One strategic portrait.
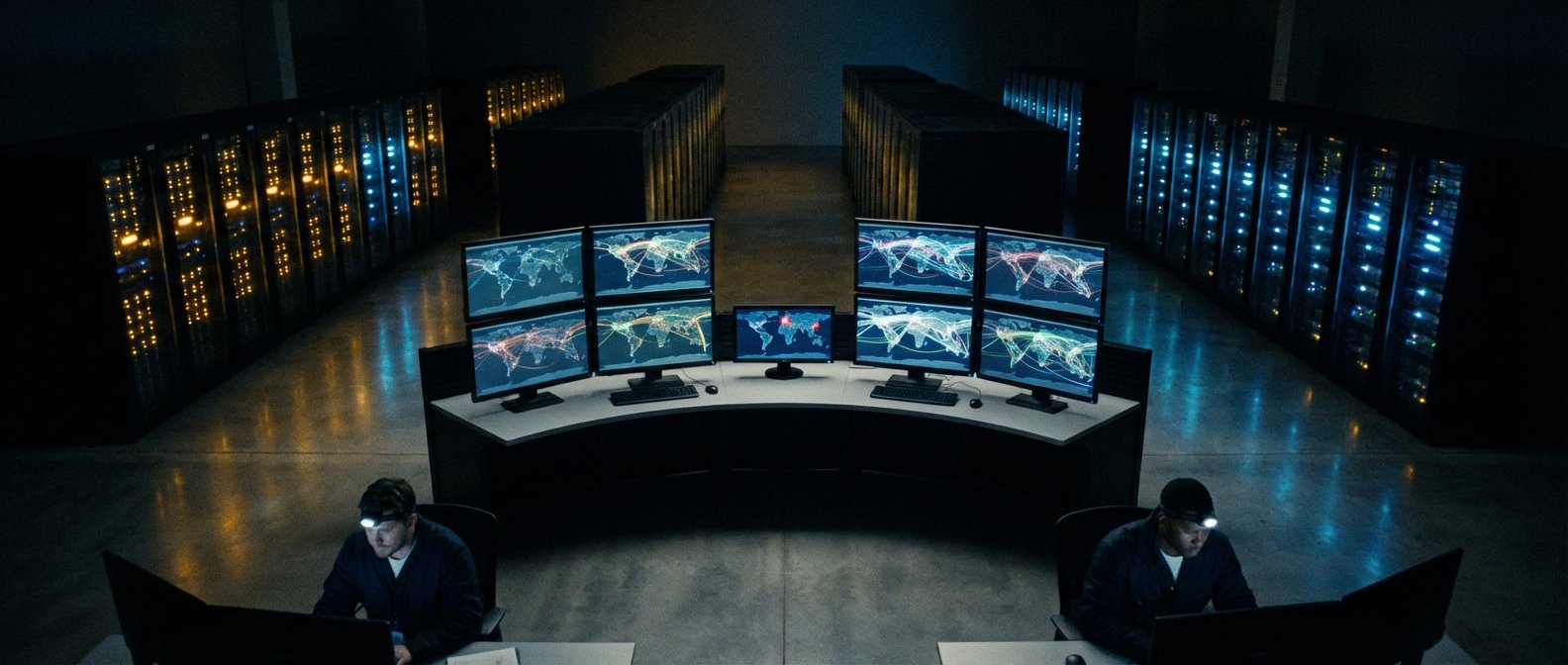
The Sleeper in the Switch
BPFDoor doesn’t open a port. It doesn’t beacon home. It does nothing visible until it receives a specific “magic” packet, at which point it hands over shell access. It hooks into the Linux kernel at the lowest level of the operating system, invisible to standard port scans and conventional monitoring.
A China-linked group tracked as Red Menshen has been using this technique to maintain persistent access inside telecom providers across the Middle East and Asia since at least 2021. These aren’t small ISPs. Telecom backbone networks carry the traffic of governments, militaries, and banks. Getting into the switch means you can reach practically anyone who flows through it.
Rapid7 called what they found “some of the stealthiest digital sleeper cells ever encountered in telecommunications networks.” That’s not marketing copy. These implants are designed to survive reboots, evade detection, and provide on-demand access years after the initial breach.
The Accusation Washington Finally Said Out Loud
While Red Menshen runs silent long-term espionage ops, a different operation has been bleeding Americans dry in broad daylight. This week, a senior US official said it plainly: the Chinese government is implicitly backing the criminal syndicates running cyber scam compounds across Southeast Asia.
These compounds, concentrated in Myanmar, Cambodia, and Laos, use trafficked workers to run pig butchering scams and investment fraud targeting victims in the US and Europe. Billions stolen every year. They’re geographically fixed, large-scale, and well-documented. The US argument is that China’s non-action is itself a form of support.
That’s a diplomatic accusation with real weight behind it. What comes next, sanctions, visa restrictions, secondary sanctions, matters a lot. The statement is the opening move.
The Infrastructure Behind the Scams
The third piece snaps the picture together. The UK sanctioned Xinbi Guarantee, a Telegram-based marketplace that processed roughly $20 billion in transactions while selling money laundering services, fraud toolkits, and support infrastructure for scam operations. It operated openly on Telegram, which has been comfortable enough cover that these platforms don’t need the dark web.
What You’re Actually Looking At
State-linked hackers with persistent access to the world’s communications infrastructure. Criminal networks with implicit state tolerance draining billions from Western consumers. Shadow financial infrastructure on Telegram laundering the proceeds and keeping the machine running.
Not three unrelated stories. Three expressions of the same tolerance for hostile activity directed at Western targets, each operating at a different layer of the stack.
The UK sanctioned a marketplace. The US made an accusation. Researchers published a detailed breakdown of a backdoor that’s been sitting inside telecom networks for years.
That’s where things stand.