John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com

Unwinding the Deal: China Blocks Meta's Manus AI Acquisition
China reversed a completed Meta acquisition of AI startup Manus on national security grounds. We're now in the era of strategic AI protectionism.
Read More
Adversarial Distillation: The Industrial-Scale Theft of Frontier AI
The White House has officially flagged 'adversarial distillation' as a major threat. China is using tens of thousands of fake accounts to clone U.S. AI capabilities by strip-mining model outputs. This is model theft through the front door.
Read More
The Devices China Already Owns: Pre-Positioning for Future Conflict
China's state actors aren't just hacking networks; they're acquiring real estate. A massive joint advisory reveals how covert device networks are being pre-positioned inside everyday hardware like routers and NAS devices, waiting for the right moment to be activated.
Read More
China Is Running Two Operations Against Taiwan at Once
Cisco Talos found Lua-based malware targeting Taiwanese NGOs and universities. Taiwan's intelligence service identified 13,000 AI-amplified influence accounts and 860,000 posts. These are not separate stories.
Read More
A Hacker Claims the Biggest Military Breach in History. Experts Think It Might Be Real.
FlamingChina claims to have stolen 10 petabytes from China's National Supercomputing Center in Tianjin, including missile schematics and weapons testing data. CNN showed samples to cybersecurity experts. They declined to dismiss it. This has not been confirmed.
Read More
China's Ransomware Groups Are Using Zero-Days Now. That Changes the Math.
Microsoft links China-based Storm-1175 to Medusa ransomware using zero-day exploits, while Qilin deploys EDR-killing techniques before encryption.
Read More
China's TA416 Is Back in Europe After Two Years. They Brought New Tricks.
TA416 has resumed targeting EU government and diplomatic organizations with PlugX malware, now abusing OAuth redirects to slip past traditional phishing defenses.
Read More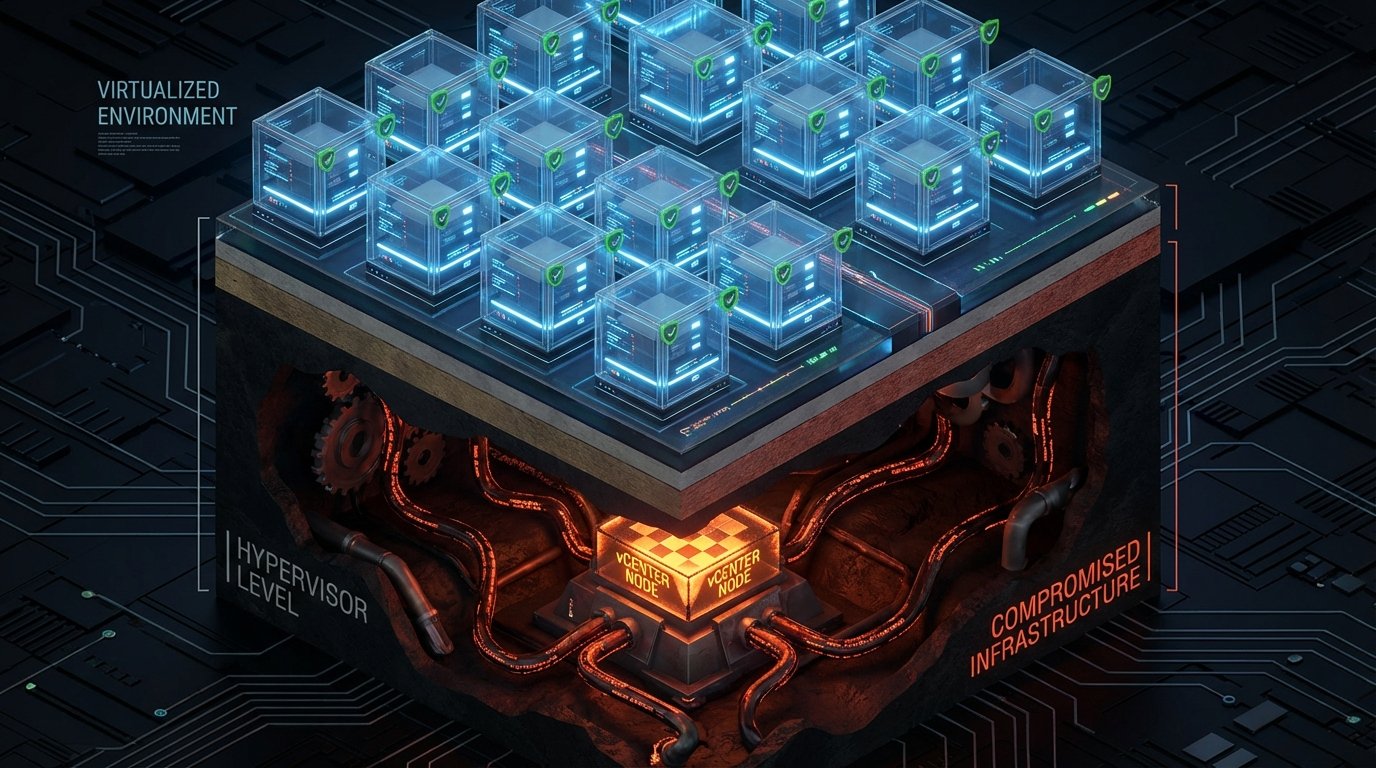
BRICKSTORM Hides Where Your EDR Can't See It
A suspected China-nexus espionage operation targets VMware vCenter and ESXi hypervisors, persisting at the virtualization layer where endpoint security is blind.
Read More
A Zero-Day Turned TrueConf's Update Channel Into a Malware Delivery System
Chinese-nexus actors exploited a zero-day in TrueConf to hijack the update mechanism and push trojanized updates to Southeast Asian government agencies.
Read More
FBI Says China Hacked Its Surveillance Systems, Triggers 'Major Incident' Classification
The FBI classified a suspected Chinese intrusion into law enforcement surveillance infrastructure as a FISMA major incident, forcing Congressional notification within days.
Read More
China's BPFDoor Got an Upgrade. Passive Defenses Still Can't See It.
Red Menshen's upgraded BPFDoor backdoor now hides even better inside telecom backbone networks, and the only way to find it is active threat hunting that most carriers aren't doing.
Read More
China Is Running Three Cyber Operations Against the West Simultaneously. Here's What They Look Like.
BPFDoor sleeping inside telecom networks, US officials blaming Beijing for enabling billion-dollar fraud, and a $20B Telegram black market just sanctioned by the UK. Three fronts, one picture.
Read MoreSmuggled Silicon: The DOJ Case That Puts AI Export Controls in the Spotlight
Three men charged with smuggling US AI hardware to China represent the first major criminal test of export control law applied to high-performance compute. The era of treating AI export controls as background noise is over.
Read More
Two Spy Campaigns, Two Completely Different Playbooks
A Chinese APT has been sitting inside Southeast Asian military networks for six years. Meanwhile, Russian hackers are stealing Signal accounts with fake support messages. Same goal, wildly different approaches.
Read More
China's Been Quietly Spying on Southeast Asian Militaries for Years
Unit 42 documented a suspected Chinese state-sponsored espionage campaign with years of undetected access to military networks across Southeast Asia. This is what patient intelligence collection looks like.
Read More
After the 'Worst Telecom Hack in History,' Washington Is Already Moving On
Salt Typhoon was called the most significant cyberattack on US telecom infrastructure ever. Policy reform momentum is stalling. Congress is more interested in restricting FBI surveillance than fixing the infrastructure that got hacked.
Read More