John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
Most supply chain attacks trick you into installing the wrong thing. GlassWorm doesn’t bother. It steals your GitHub credentials and injects malicious code directly into repos you already trust.
And the code it injects? You literally can’t see it.
Not hidden in a binary. Not obfuscated. Written in Unicode characters that render as nothing on screen. You can review the diff line by line and see absolutely nothing wrong. But the payload is there, and it runs just fine.
Between March 3 and 9, researchers found 151 malicious packages pushed across GitHub repos, PyPI, npm, and Open VSX. Django apps, ML research repos, Streamlit dashboards, popular Python packages. All hit.
Here’s why this is so nasty. It stacks two deception layers, and either one alone would be bad enough.
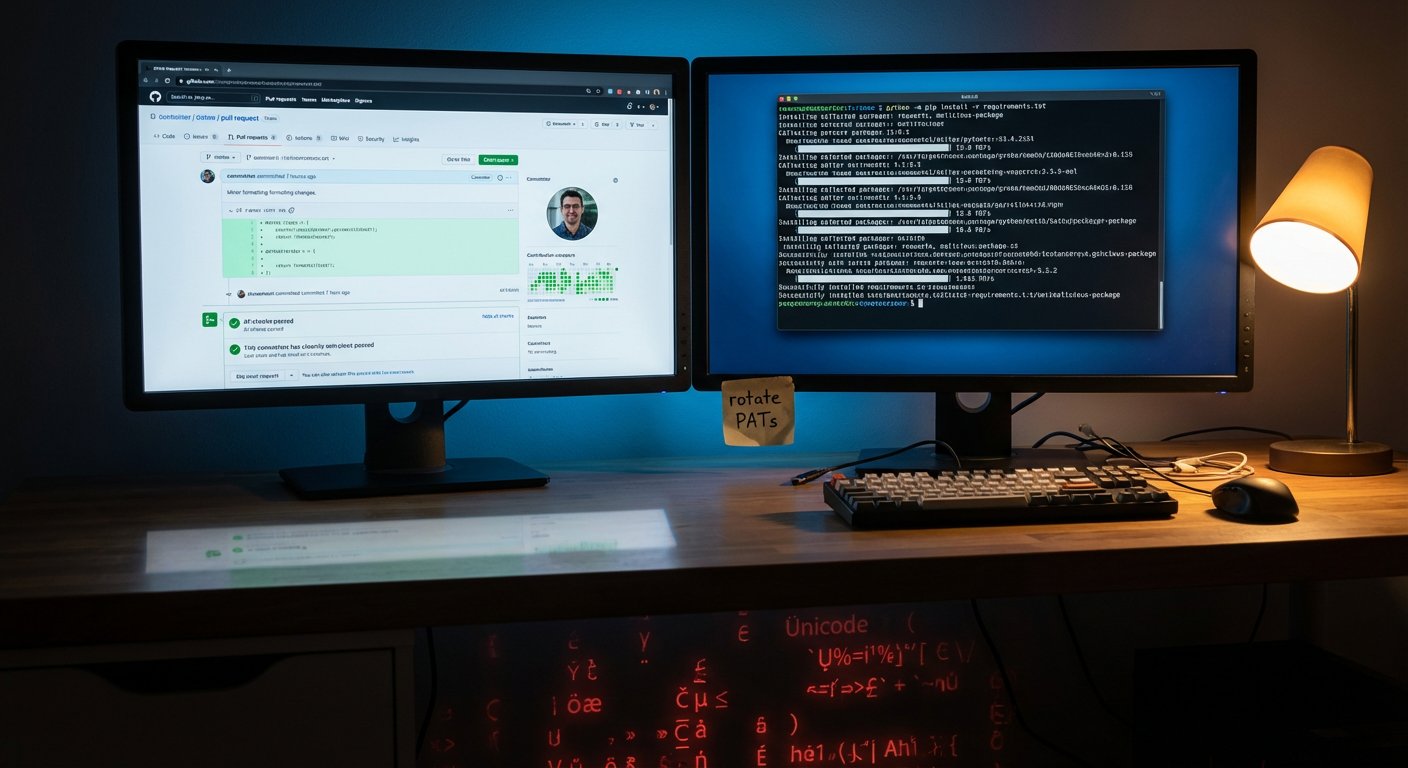
First, credential theft. GlassWorm grabs GitHub personal access tokens from compromised dev machines. With a valid PAT, it pushes commits as the developer. GitHub sees a trusted account making authorized changes. Nothing looks wrong.
Second, the invisible payloads. The injected code uses Unicode characters with no visible representation. Editors and diff viewers show empty space or nothing at all. But interpreters process them fine. The backdoor executes without a trace in the source.
So you’ve got commits from real accounts with real histories, containing code changes that look like harmless whitespace. Good luck catching that in a PR review.
This isn’t GlassWorm’s first rodeo. But this campaign is an escalation. They’ve moved past just uploading sketchy packages to public registries. Now they’re compromising legitimate accounts and modifying code inside trusted repos. That sidesteps most of the defenses orgs have built against supply chain attacks, things like lockfiles, hash verification, and allowlists.
If you maintain Python repos on GitHub or pull from public repos:
Rotate your PATs now. Especially any active during that March 3-9 window. And if you’re still on classic PATs instead of fine-grained tokens, switch. Fine-grained tokens limit blast radius.
Scan your repos for invisible Unicode. There are tools for detecting non-printable and zero-width characters in source files. If you haven’t been checking for this, you’ve had a blind spot.
Enable commit signing. It won’t stop a stolen PAT from pushing code, but unsigned commits from accounts that normally sign will stick out.
Review recent commits. Look for whitespace-only changes, formatting tweaks, or commits touching files without clear functional purpose. Those are the hiding places.
The bigger takeaway: developer credentials are high-value targets that need the same protection as production infrastructure credentials. In a supply chain attack, they’re the same thing.