John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com

From Job Interview to Lab-Infection: How Hackers are Worming Through Your Team
North Korea's newest 'Contagious Interview' wave is turning your own developers into delivery boys. One fake interview is enough to backdoor your entire codebase.
Read More
Administrative Betrayal: The Bitwarden CLI Supply Chain Hijack
A malicious npm package impersonating the Bitwarden CLI installed its own runtime to steal secrets. When security tools are the attack vector, the whole CI/CD pipeline becomes a weapon.
Read More
Patch and Pray Failed: FIRESTARTER Proves Cisco Devices Can Stay Owned
A federal agency followed the rules, patched the CVE, and still got owned. FIRESTARTER is a specialized Cisco backdoor designed to survive the remediation cycle. It’s time to stop assuming a patch equals a clean network.
Read More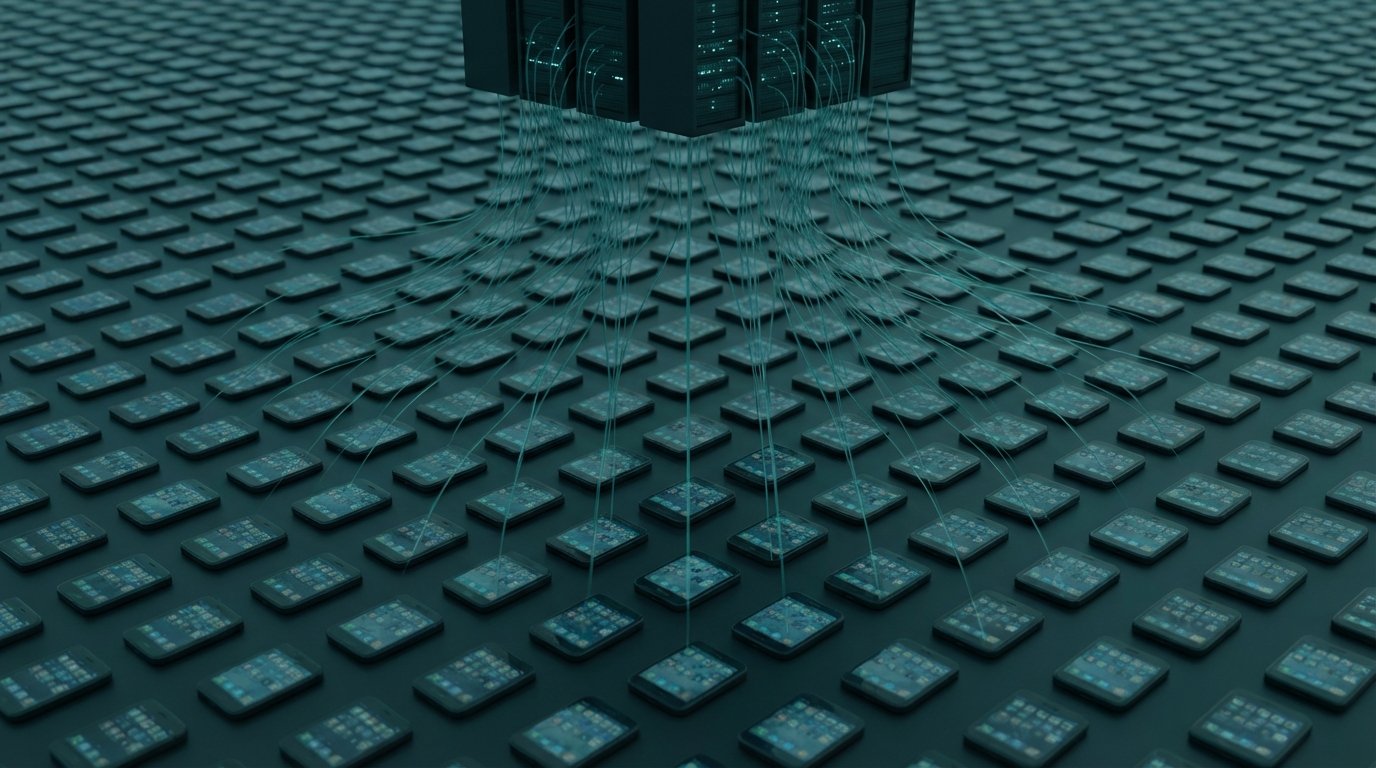
Your Phone, Your Browser, Your Router. All Still Working. All Compromised.
220,000 Android phones recruited into a criminal proxy network via Facebook ads. 108 Chrome extensions in the official Web Store harvesting Google and Telegram credentials. Russia's GRU running DNS hijacks through 18,000 home routers until law enforcement shut it down. Three campaigns, one pattern: your device keeps working while someone else uses it.
Read More
The Trusted Download Is the Attack Vector
CPUID's official site served a malicious installer for hours. A fake WakaTime extension has been spreading across dev machines for months. Two separate campaigns, one shared trick: they got inside the thing you already trusted.
Read More
Apple Patched the Door. Attackers Used the Window.
macOS 26.4 added Terminal security scanning to block ClickFix attacks. Within 48 hours, Atomic Stealer was back, running through Script Editor instead. One click. No warning.
Read More
A Full Android Rootkit Hid in Google Play for Months. 2.3 Million Downloads.
McAfee found a full rootkit hiding in 50+ Google Play apps. It roots your phone, survives factory resets, and hijacks WhatsApp sessions. 2.3 million devices already got it.
Read More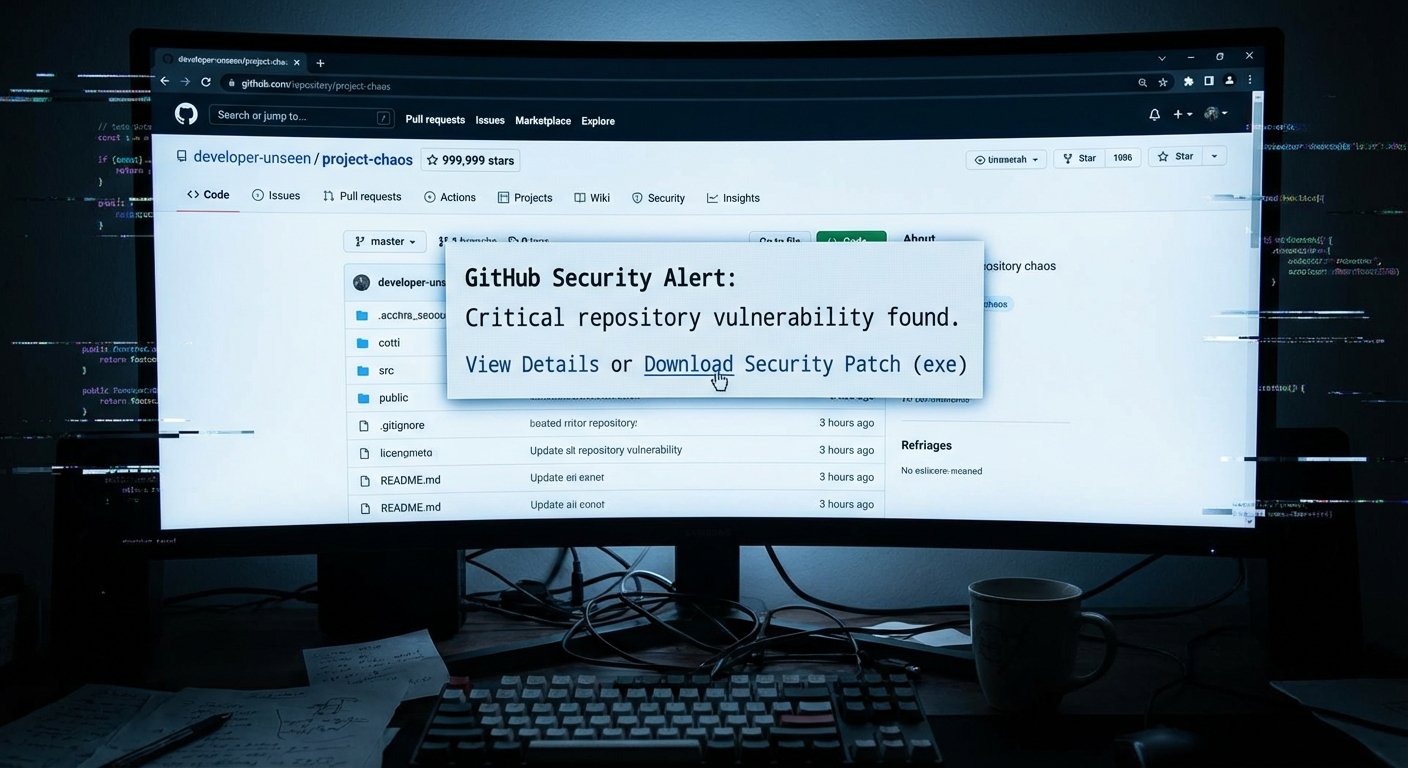
GitHub Is Becoming a Minefield for Developers. Most of Them Have No Idea.
Three simultaneous attacks on GitHub's trust signals -- fake stars, weaponized security alerts, and a scanning bug that let 72 malicious extensions slip through -- show the reputation infrastructure developers rely on is broken.
Read More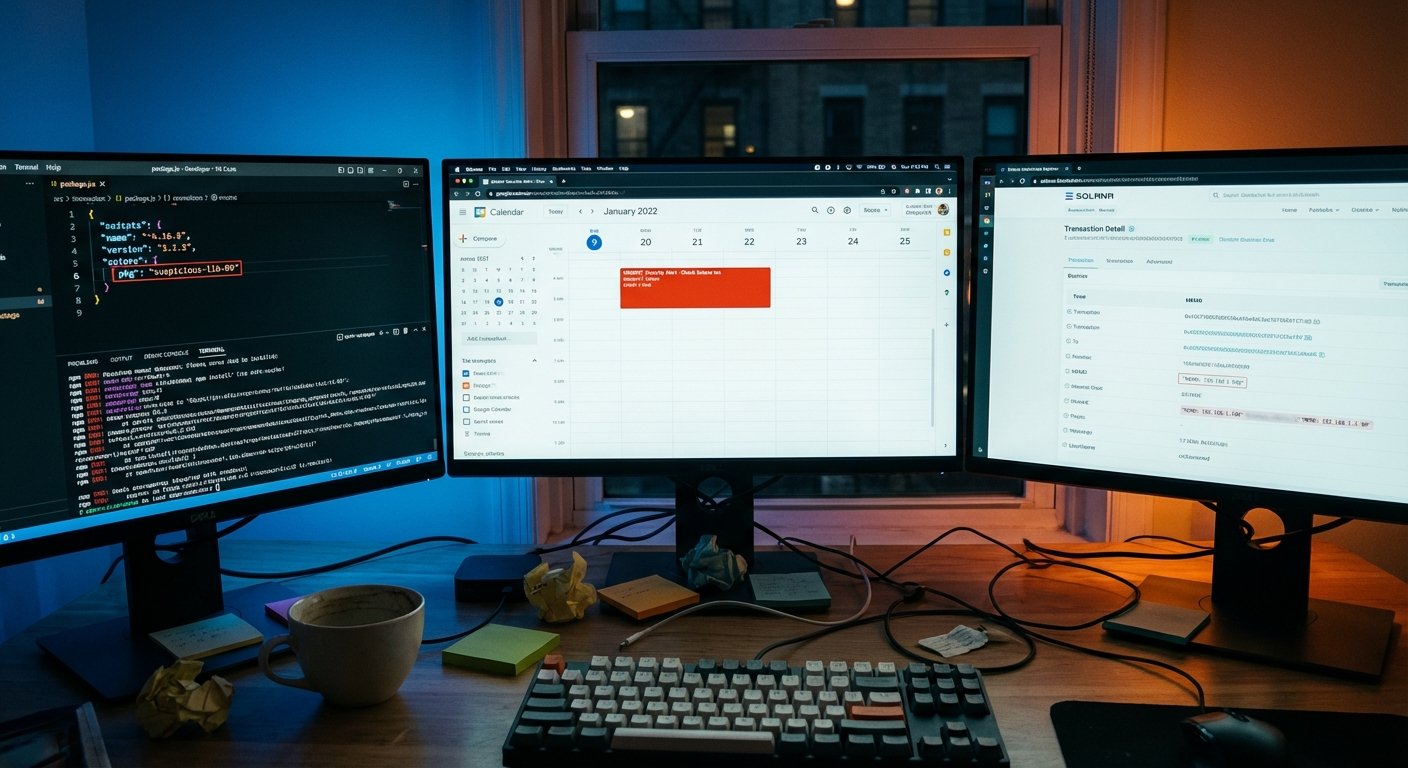
This Malware Hides Its Command Server in the Blockchain, and Borrows Google Calendar Too
GlassWorm targets developers through compromised npm, PyPI, and GitHub packages. Its C2 address is hidden in a Solana blockchain memo. You can't take down a blockchain transaction.
Read More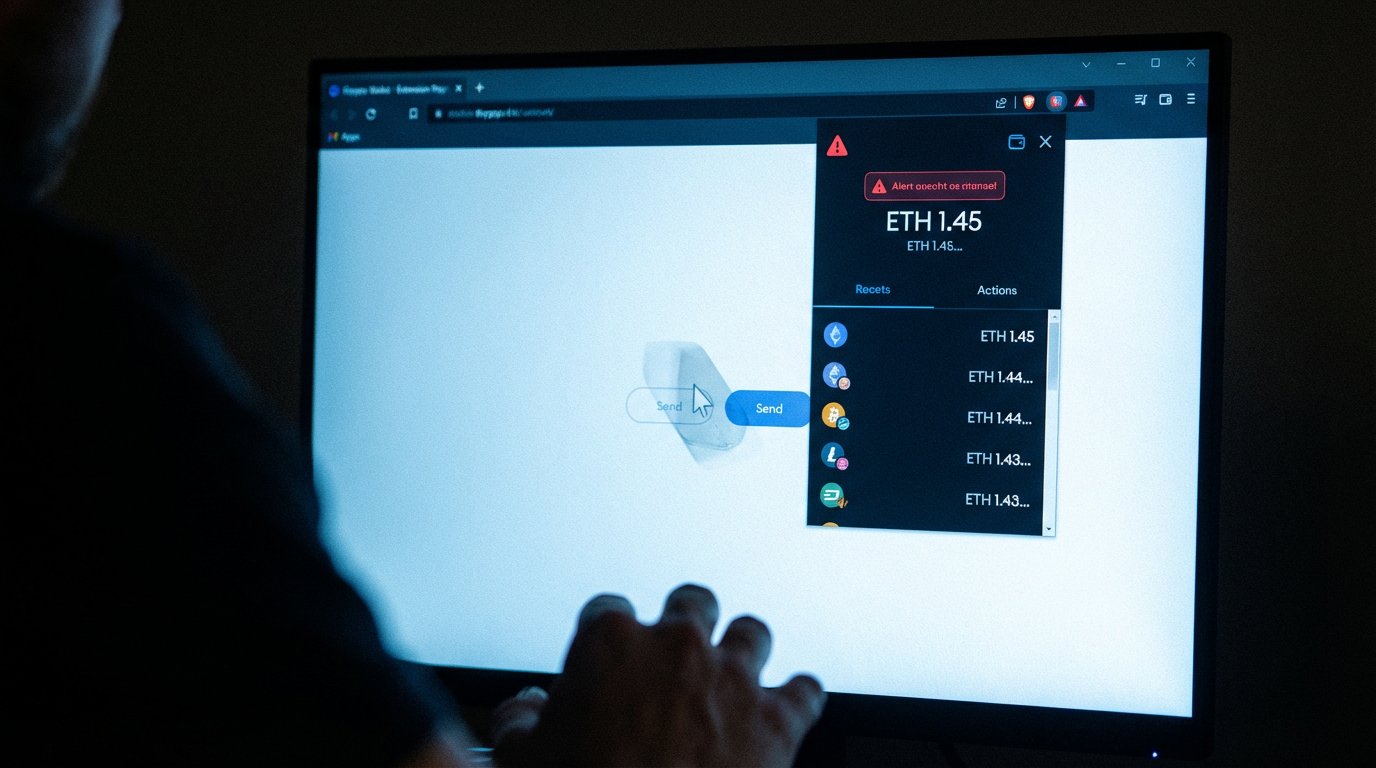
Torg Grabber Is Coming for Your Crypto Wallet Extensions
Torg Grabber is a new infostealer targeting 728 cryptocurrency browser wallet extensions, including MetaMask, Phantom, Exodus, and Coinbase. It's a full MaaS operation with real victims.
Read More
CanisterWorm: TeamPCP Hides Its C2 on a Blockchain You Can't Take Down
TeamPCP's new wiper, CanisterWorm, uses an ICP blockchain canister as its C2 resolver -- no domain to seize, no server to kill. And it now runs on any system, not just Kubernetes.
Read More
The npm Ghost: That Install Log Looked Normal Because It Was Built to Fool You
Seven malicious npm packages have been stealing sudo passwords and crypto wallet data from developer machines since February. The trick: they generate fake terminal output so convincing that developers don't look twice.
Read More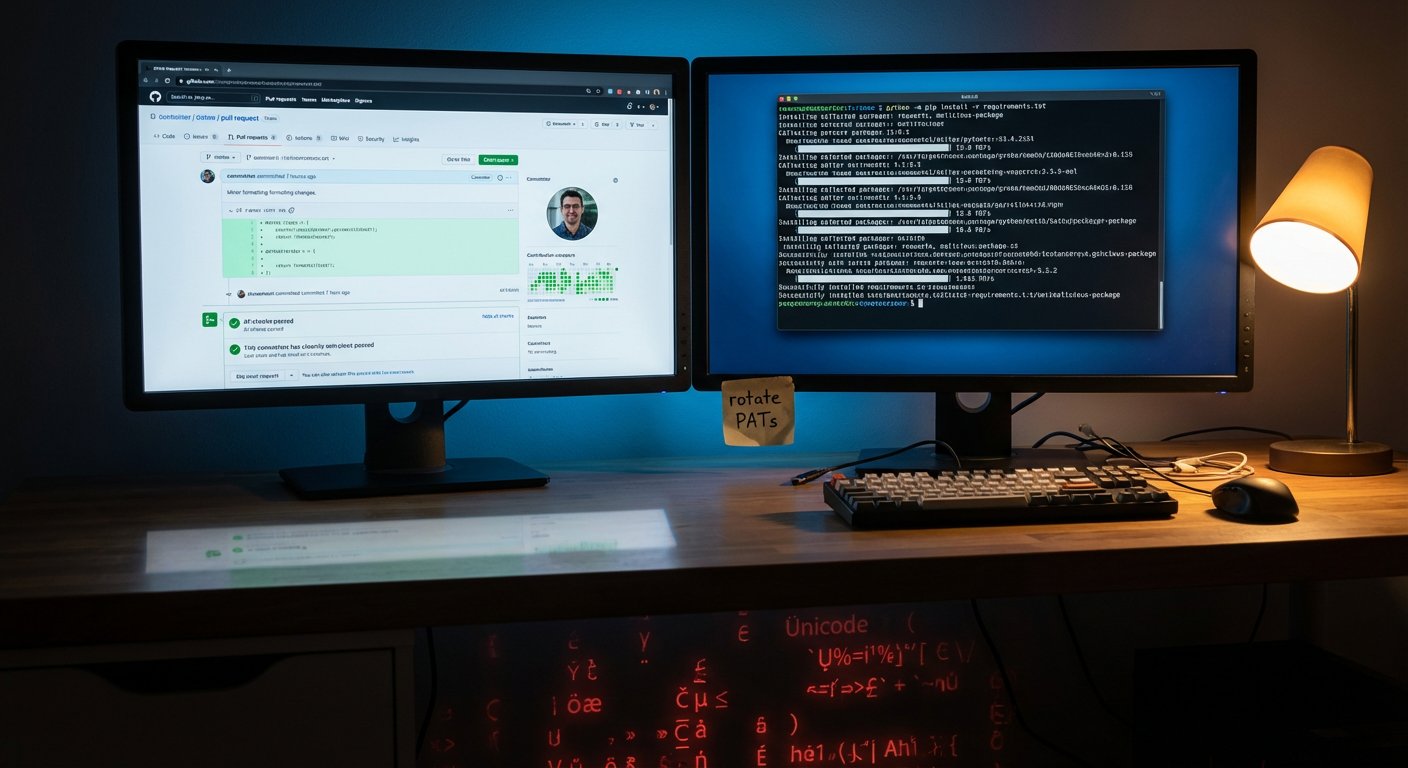
GlassWorm Is Hiding Malware in Invisible Code and Pushing It Into Your Python Repos
GlassWorm steals GitHub tokens, then injects malicious code written in invisible Unicode characters into repos developers already trust. 151 packages hit in one week.
Read More
ClickFix Went Cross-Platform This Week. Mac Users, You're Not Safe.
Three separate campaigns are using ClickFix to trick people into installing malware themselves. macOS, Windows, enterprise VPN users. No exploit needed. Just copy, paste, execute.
Read More
The Software You Trust Is Becoming the Attack: Two Supply-Chain Strikes in One Week
GlassWorm hijacked VS Code extension dependencies. AppsFlyer's SDK got compromised to serve crypto stealers. Both attacks exploited trust, not carelessness.
Read More
Your Data This Week: Starbucks Employee Breach, Loblaw Customer Data, Steam Malware, and How to Respond to Each
Three breaches hit this week through platforms people already trust. Starbucks employee data, Loblaw customer accounts, and FBI-flagged malware hiding in Steam games.
Read More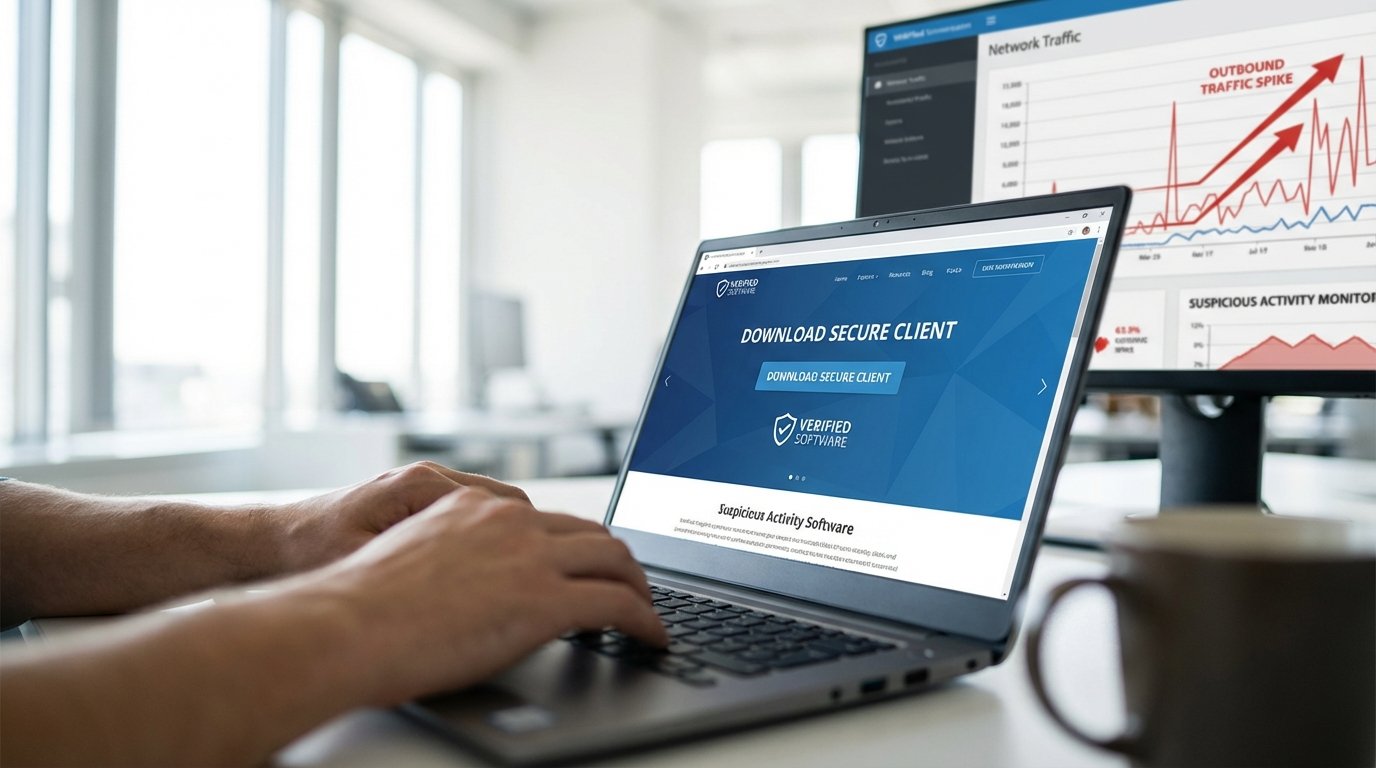
Storm-2561: Googling Your VPN Download Just Became a Security Risk
Microsoft exposed Storm-2561, a threat actor using SEO poisoning to serve fake VPN downloads that steal corporate credentials. The attack requires zero phishing emails. Just a search engine.
Read More
AI Is Now Both the Weapon and the Target
Slopoly is AI-generated malware used in a live ransomware attack. Microsoft Copilot can be hijacked through emails you just receive. AI security isn't future-tense anymore.
Read More
BlackSanta Kills Your EDR Before You Even Know You're Hit — and It's Coming Through HR
New malware called BlackSanta disables your endpoint detection, and it's getting in through HR inboxes. That combo is nastier than it sounds.
Read More