John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com

The Infrastructure House of Cards: Vercel, cPanel, and Outsourced Risk
Managed hosting is great until it isn't. This week cPanel got bypassed, Vercel leaked 100,000 .env secret files, and Virtualizor handed over the keys to your VPS.
Read More
From Job Interview to Lab-Infection: How Hackers are Worming Through Your Team
North Korea's newest 'Contagious Interview' wave is turning your own developers into delivery boys. One fake interview is enough to backdoor your entire codebase.
Read More
Persistent Espionage: Mustang Panda's LOTUSLITE Campaign Hits Banking
A refreshed LOTUSLITE variant from Mustang Panda is targeting Indian banks and South Korean policy groups. Nation-states aren't extortionists. They're collectors. And they're patient.
Read More
Administrative Betrayal: The Bitwarden CLI Supply Chain Hijack
A malicious npm package impersonating the Bitwarden CLI installed its own runtime to steal secrets. When security tools are the attack vector, the whole CI/CD pipeline becomes a weapon.
Read More
The Printing Provider Pivot: Concentration Risk Hits US Banks
Citizens Bank and Frost Bank customers had their data stolen through outsourced printing and tax fulfillment vendors. Everest ransomware is targeting the boring middle layer.
Read More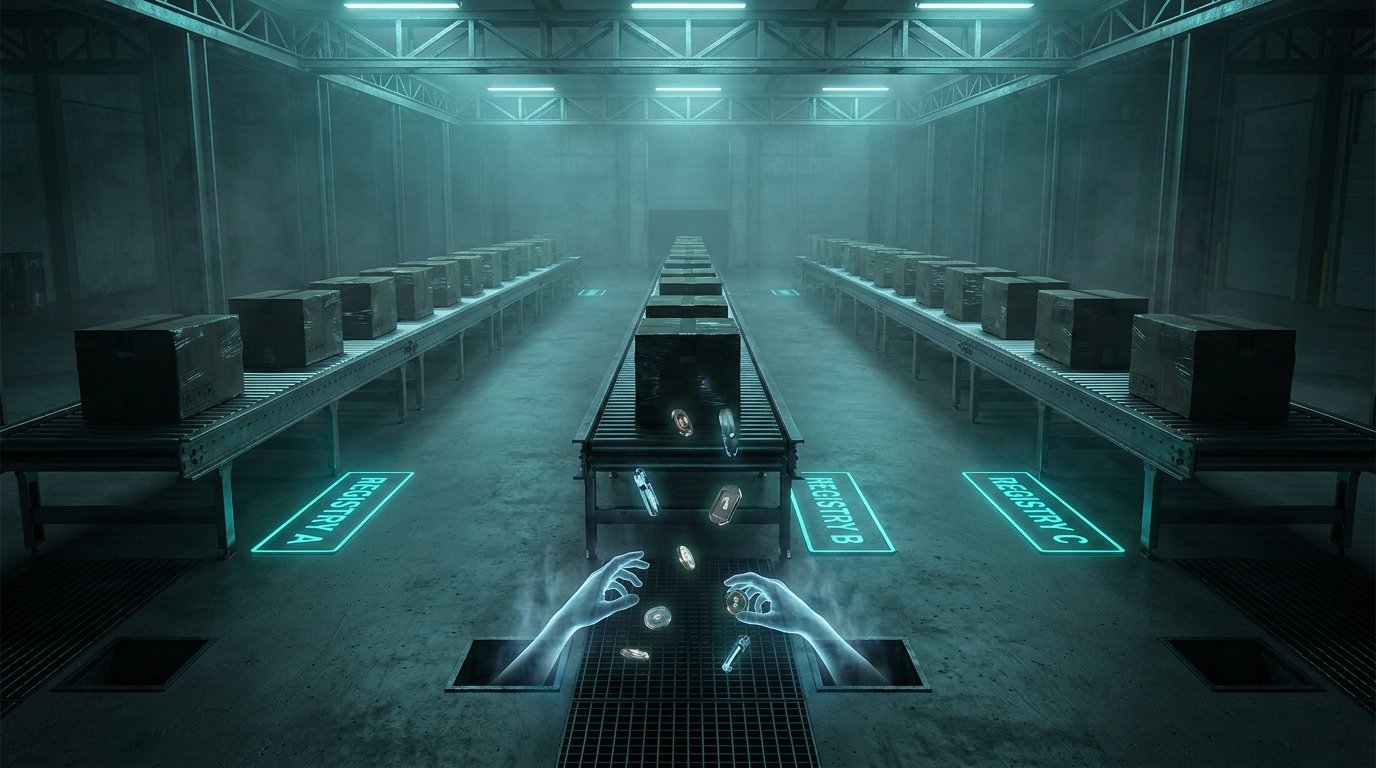
The 48-Hour Secrets Sprint: How Three Registries Were Swept in One Weekend
A coordinated 48-hour sprint hit npm, PyPI, and Docker Hub, targeting developer secrets at scale. From infected AI libraries to a trojanized security scanner, the supply chain is moving faster than your detection.
Read More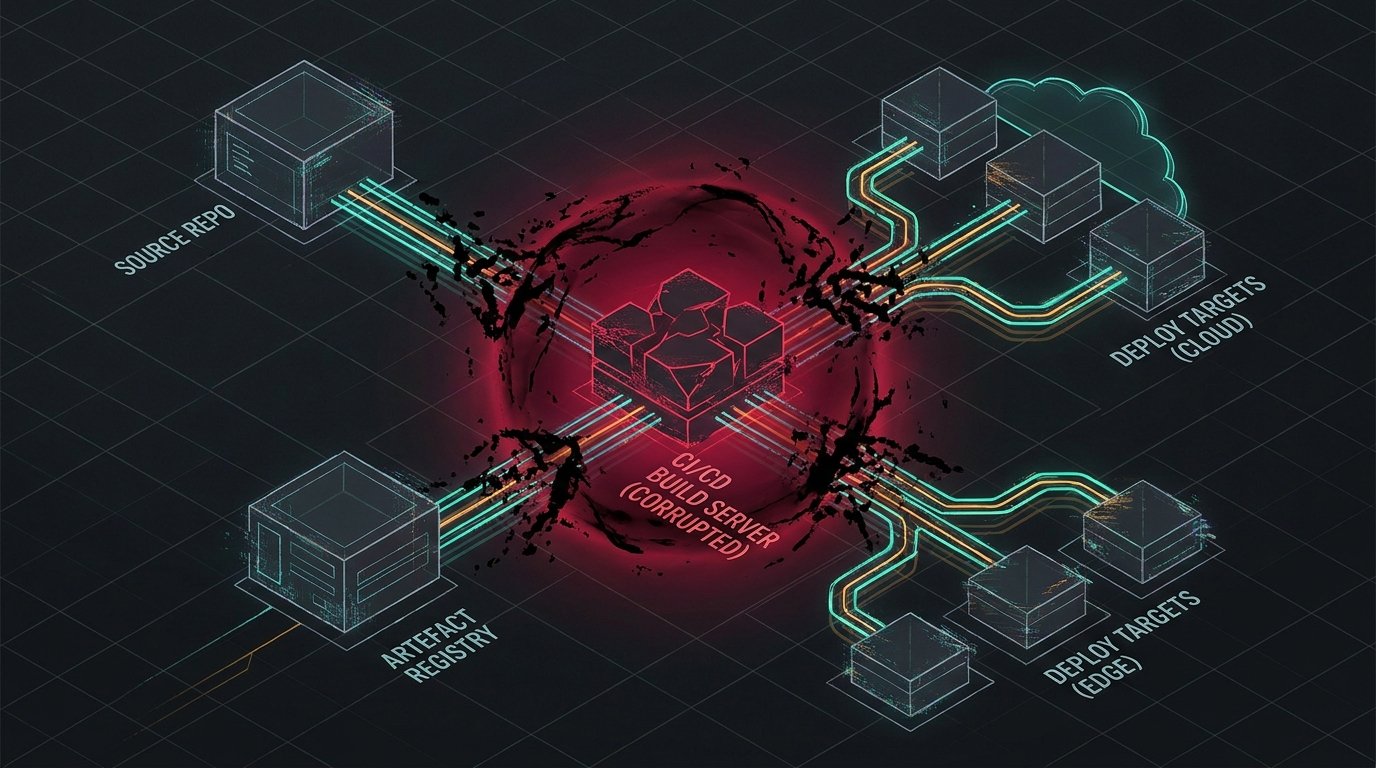
The CI/CD Supply Chain Crisis: Poisoning the Well at the Source
Attackers are ignoring the database and going for the person writing the code. Bamboo, GitLab, and Spinnaker are facing critical flaws that turn your build tools into weapons.
Read More
The Mythos Breach: Your AI Is Only as Secure as Its Weakest Integration
Unauthorized access to Anthropic's Mythos model via a compromised OAuth app exposes the real security threat in the agentic AI era: third-party integrations that inherit trust they haven't earned.
Read More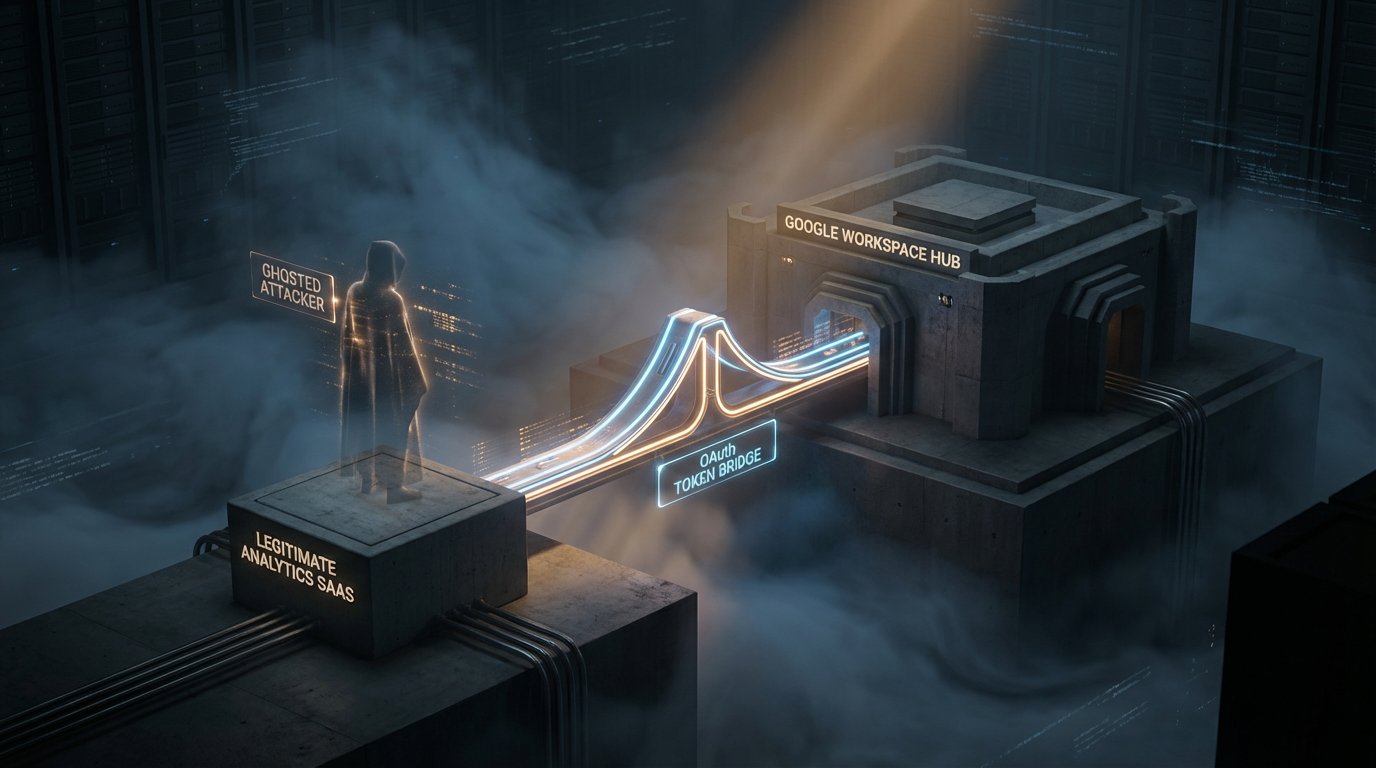
The 22-Month Window: How Vercel's Upstream Analytics Bridge Was Compromised
Vercel recently disclosed a major security incident via Context.ai that began in June 2024. For nearly two years, an invisible door was held open into the core of their cloud identity. It is a masterclass in the hidden risks of 'harmless' SaaS analytics.
Read More
Two Breaches Today. One Was Careful. One Was a Unlocked Door. Both Were Catastrophic.
ShinyHunters dumped 78.6 million Rockstar records after the ransom deadline expired. They never touched Rockstar directly. They went through a cloud analytics vendor. Meanwhile, a French email provider left an Elasticsearch cluster open to the internet and exposed 40 million records across L'Oreal, Renault, and French government embassies.
Read More
The Week the Clock Ran Out
Defenders got squeezed this week. AI sped up vuln discovery, OT attacks stayed active, and trusted update channels turned into incident response events.
Read More
The Week the Clock Ran Out
Defenders got squeezed this week. AI sped up vuln discovery, OT attacks stayed active, and trusted update channels turned into incident response events.
Read More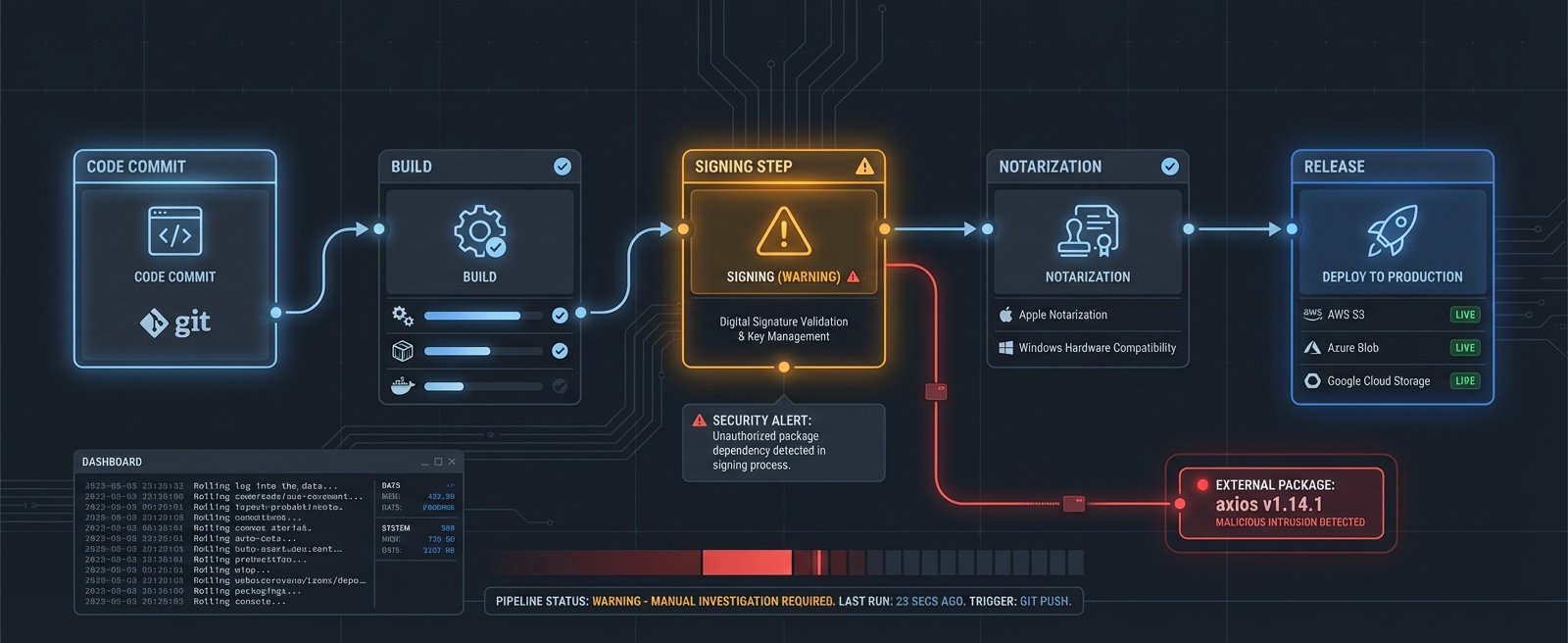
OpenAI Rotated Its macOS Signing Certs After the Axios Attack. No Proof of Key Theft. They Rotated Anyway.
A malicious Axios npm package executed inside OpenAI's GitHub Actions signing workflow. Their investigation found no evidence keys were stolen. They revoked and rotated the certificates anyway. That decision is the interesting part.
Read More
Your WordPress Plugin Auto-Updated. Now You Have Six Backdoors.
Attackers hijacked the Smart Slider 3 Pro update server and pushed a six-layer backdoor to 900,000 sites. The must-use plugin it installed doesn't show up in your WordPress dashboard. Deleting the plugin doesn't remove it.
Read More
The Trusted Download Is the Attack Vector
CPUID's official site served a malicious installer for hours. A fake WakaTime extension has been spreading across dev machines for months. Two separate campaigns, one shared trick: they got inside the thing you already trusted.
Read More
Apple Patched the Door. Attackers Used the Window.
macOS 26.4 added Terminal security scanning to block ClickFix attacks. Within 48 hours, Atomic Stealer was back, running through Script Editor instead. One click. No warning.
Read More
Your AI Coding Tools Have an Invisible Attack Surface. One Model Falls for It Every Time.
Researchers find 63 MCP servers with hidden Unicode characters in tool descriptions, and GPT-5.4 follows the invisible instructions with 100% compliance.
Read More
The AI Training Pipeline Just Became a High-Value Target
A trojanized LiteLLM package hit Mercor, the AI training vendor shared by OpenAI, Anthropic, and Meta, exposing the massive concentration risk in the AI supply chain.
Read More
TeamPCP's Criminal Empire Is Growing and Nobody Agrees Who's Running It
TeamPCP has evolved from cloud extortion to a criminal franchise operation with a wiper targeting Iran, a ransomware partnership with 300K affiliates, and public feuds with other threat actors.
Read More
TeamPCP Hacked the European Commission Through a Security Scanner
TeamPCP breached the European Commission via a poisoned version of Trivy. Data from 30+ EU entities got exposed. ShinyHunters leaked it all. The irony of a security tool being the attack vector writes itself.
Read More
OpenClaw's Sixth Pairing Bug in Six Weeks Is a Full Admin Takeover
CVE-2026-33579 lets anyone with the lowest access level become full admin on OpenClaw. It's the sixth pairing CVE in six weeks, and 63% of instances run without auth.
Read More
Hackers Built a SaaS-Style Dashboard to Loot Next.js Apps at Scale
UAT-10608 built an automated framework that exploits a CVSS 10.0 React flaw to compromise Next.js apps, harvest credentials, and display the loot in a searchable dashboard.
Read More
A Zero-Day Turned TrueConf's Update Channel Into a Malware Delivery System
Chinese-nexus actors exploited a zero-day in TrueConf to hijack the update mechanism and push trojanized updates to Southeast Asian government agencies.
Read More
Claude Code's Leaked Source Spawned Malware and a DMCA Disaster
Threat actors turned Anthropic's leaked source into a Vidar infostealer campaign within 24 hours. Then Anthropic's DMCA response nuked 8,100 innocent repos.
Read More
TeamPCP's First Confirmed Victim Lost Passport Scans and Video Interviews
AI hiring platform Mercor confirmed a breach tied to the LiteLLM compromise. The stolen data includes passport scans and video interviews you can't exactly rotate like a password.
Read More
North Korea Backdoored Axios for Three Hours. That Was Enough.
DPRK hackers hijacked the Axios npm package, deploying a self-erasing backdoor across 100 million weekly downloads. Three hours was all they needed.
Read More
The Week Toolchain Trust Collapsed, Again
TeamPCP kept hitting developer tooling. AI attack surfaces went from theoretical to exploited. Attackers logged in instead of breaking in. And Iran went after the FBI director's personal inbox.
Read More
TeamPCP Is Back. Now It's Deploying Ransomware Through Your AI Libraries.
The supply-chain group that poisoned Trivy last week just hit LiteLLM and the Telnyx SDK, hid their payload in WAV audio files, and announced a ransomware affiliate partnership.
Read More
Crunchyroll Got Breached. Their Systems Were Never Touched.
6.8 million Crunchyroll users had their data stolen through a three-hop attack chain that went from a vendor's infected laptop through Okta into Crunchyroll's customer service platform, without ever touching Crunchyroll's own systems.
Read More
TeamPCP Is Not a Hacker Group Anymore. It's a Cloud Crime Platform.
TeamPCP has graduated from opportunistic attacker to full-spectrum criminal platform -- with blockchain C2 that law enforcement can't seize and a live ransomware affiliate program that costs $250 to join.
Read More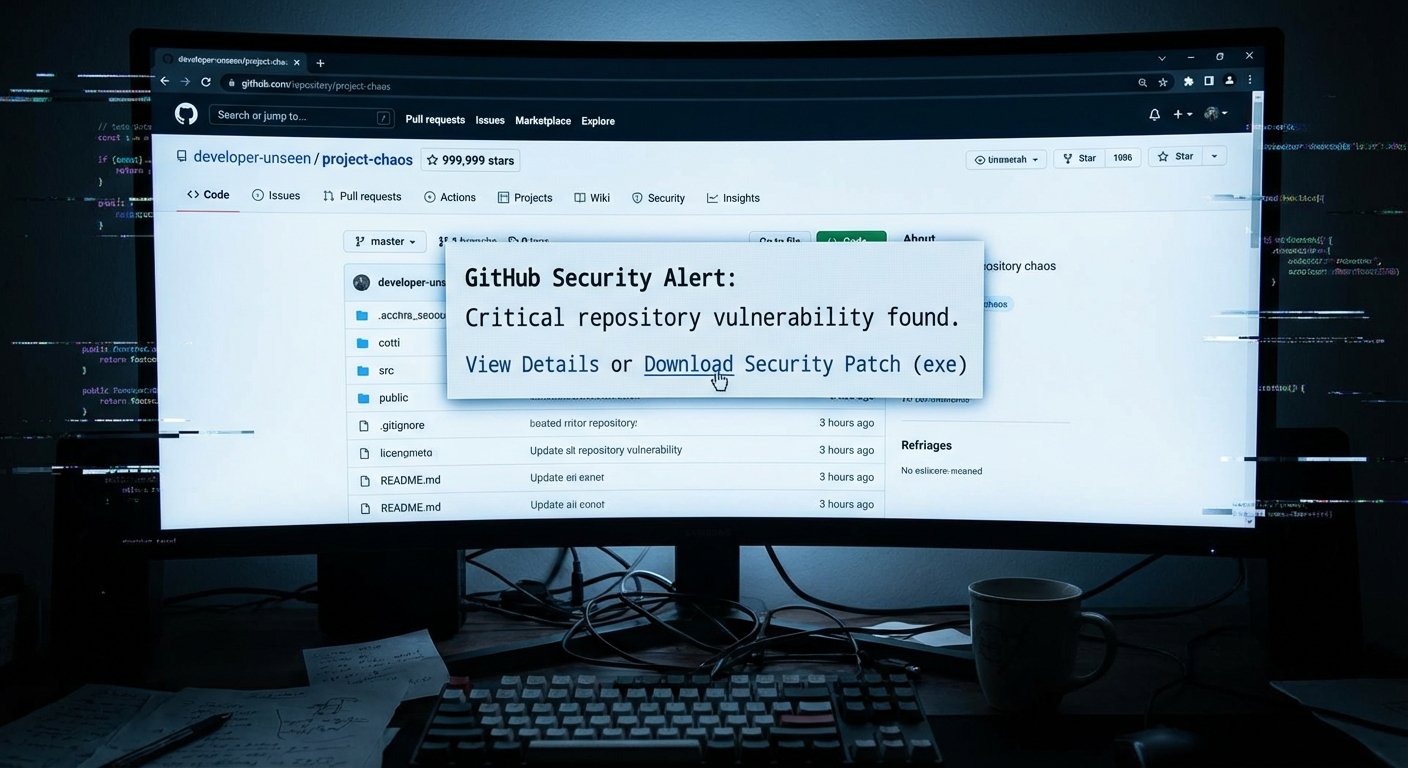
GitHub Is Becoming a Minefield for Developers. Most of Them Have No Idea.
Three simultaneous attacks on GitHub's trust signals -- fake stars, weaponized security alerts, and a scanning bug that let 72 malicious extensions slip through -- show the reputation infrastructure developers rely on is broken.
Read More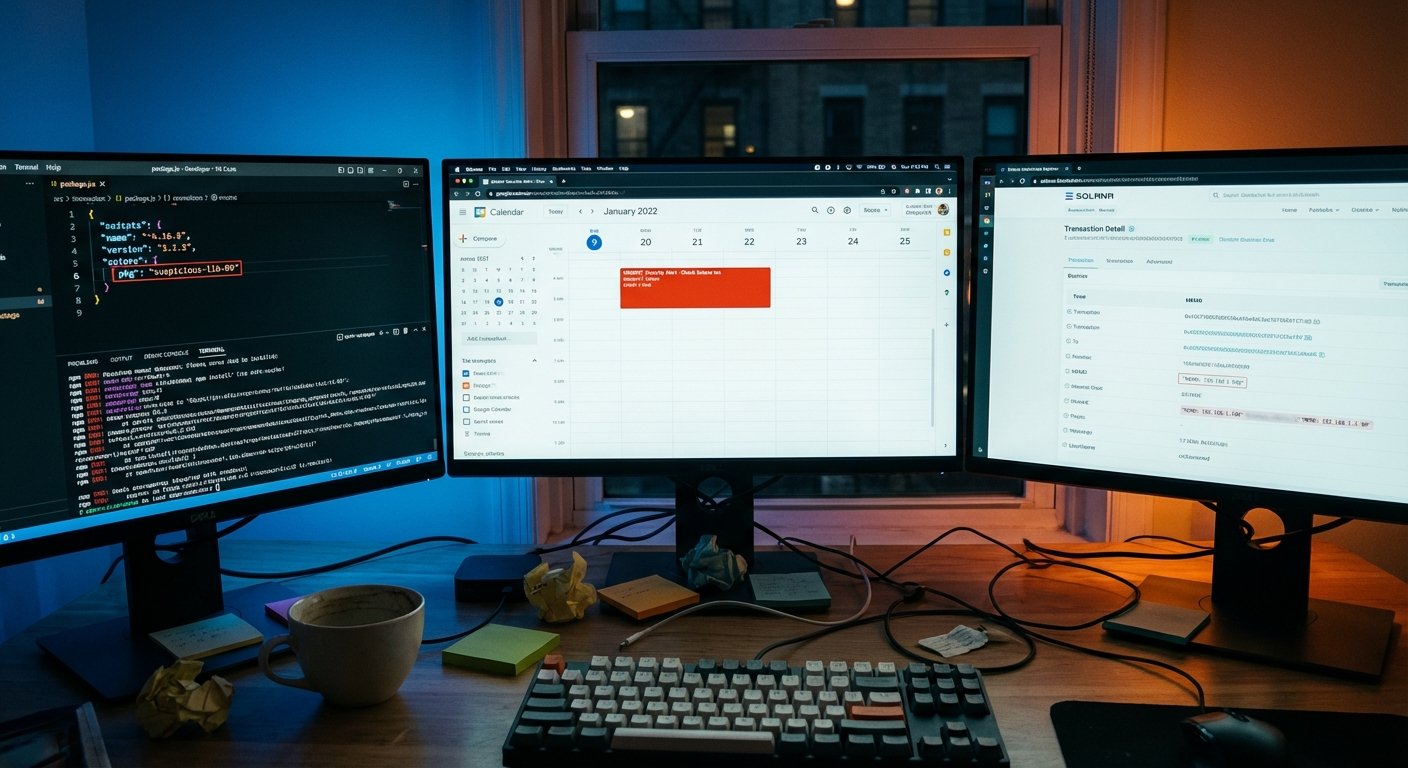
This Malware Hides Its Command Server in the Blockchain, and Borrows Google Calendar Too
GlassWorm targets developers through compromised npm, PyPI, and GitHub packages. Its C2 address is hidden in a Solana blockchain memo. You can't take down a blockchain transaction.
Read More
CanisterWorm: TeamPCP Hides Its C2 on a Blockchain You Can't Take Down
TeamPCP's new wiper, CanisterWorm, uses an ICP blockchain canister as its C2 resolver -- no domain to seize, no server to kill. And it now runs on any system, not just Kubernetes.
Read More
The Trivy Domino: How One Poisoned Security Tool Spread to a Thousand Cloud Environments
A poisoned Trivy Docker image grew into one of the year's worst CI/CD compromises. Thousands of pipelines ran the payload, LiteLLM got backdoored on PyPI, and the attackers built a three-part kit designed to hit Kubernetes clusters and stay.
Read More
The npm Ghost: That Install Log Looked Normal Because It Was Built to Fool You
Seven malicious npm packages have been stealing sudo passwords and crypto wallet data from developer machines since February. The trick: they generate fake terminal output so convincing that developers don't look twice.
Read More
The FCC Just Banned Foreign Routers. Almost Every Router You Own Is Foreign.
The FCC has declared foreign-made consumer routers a national security threat and blocked new ones from entering the US market. Here's what the rule actually covers, what it doesn't, and why the hard question about firmware goes unanswered.
Read More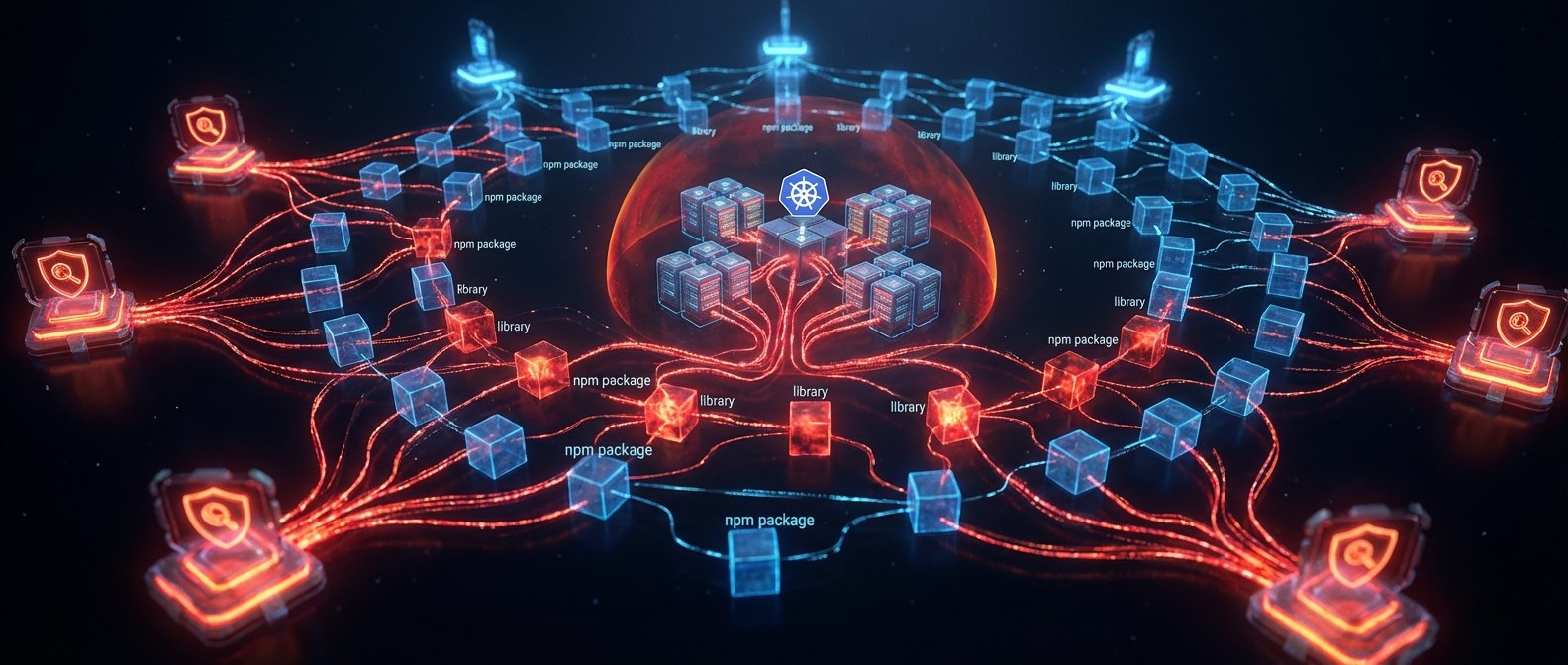
CanisterWorm: How TeamPCP Hijacked Your Security Scanners and Built an Untakeable Botnet
TeamPCP compromised Trivy and KICS CI/CD scanner tags, spread CanisterWorm to 47 npm packages, and deployed a Kubernetes wiper targeting Iranian timezones -- all controlled via blockchain C2 that can't be taken down.
Read More
The Week the Infrastructure Fought Back (and Lost)
The week of March 16-22 hit management planes, identity infrastructure, and security tooling itself -- and North Korea kept hiring.
Read More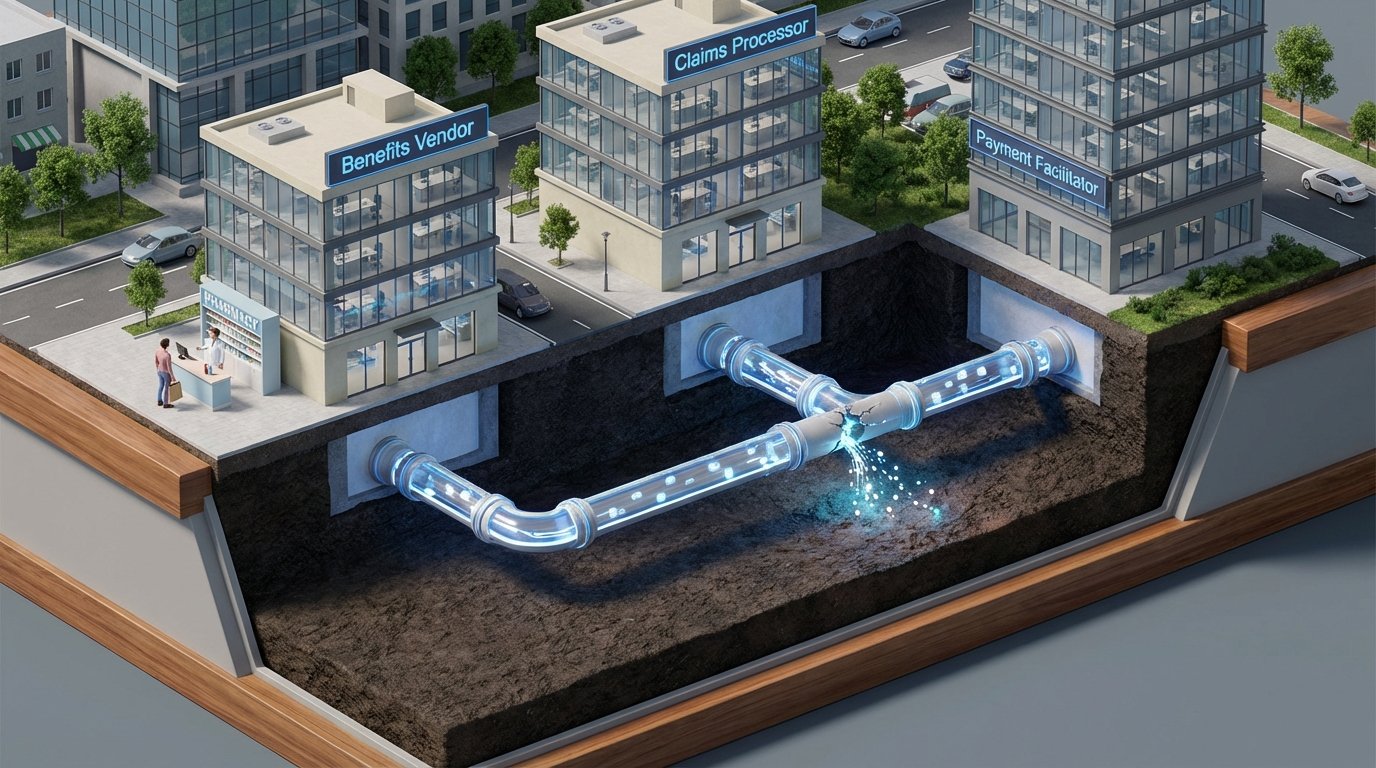
The Healthcare Benefits Breach You Haven't Heard About (or the One After It, or the One After That)
Three healthcare and benefits data breaches disclosed in the same week -- TriZetto (3.4M), Navia (2.7M), and Marquis (672K) -- follow the same disturbing pattern: your most sensitive data lives with vendors you've never heard of, and you find out months later.
Read More
The Toolchain Turned Hostile: Trivy and Langflow Show Security Pipeline Fragility
A compromised Trivy vulnerability scanner and an AI pipeline builder exploited within 20 hours of disclosure reveal a deepening problem: the tools developers trust for security are becoming high-value attack targets.
Read More
Security Below the OS: Why Device Integrity Is Becoming a Boardroom Topic
Eclypsium raised $25M for firmware security. A compromised security scanner and ongoing IoT campaigns add context. Enterprise security that stops at the OS is leaving a meaningful gap below it.
Read MoreSmuggled Silicon: The DOJ Case That Puts AI Export Controls in the Spotlight
Three men charged with smuggling US AI hardware to China represent the first major criminal test of export control law applied to high-performance compute. The era of treating AI export controls as background noise is over.
Read More
Robots Are Moving Into Sensitive Environments. Security Gets Decided at Procurement.
U.S. robotics firms are pushing Congress for procurement barriers against Chinese suppliers. Robot dogs are already patrolling data centers. The security posture is decided before install day, during sourcing and contract language.
Read More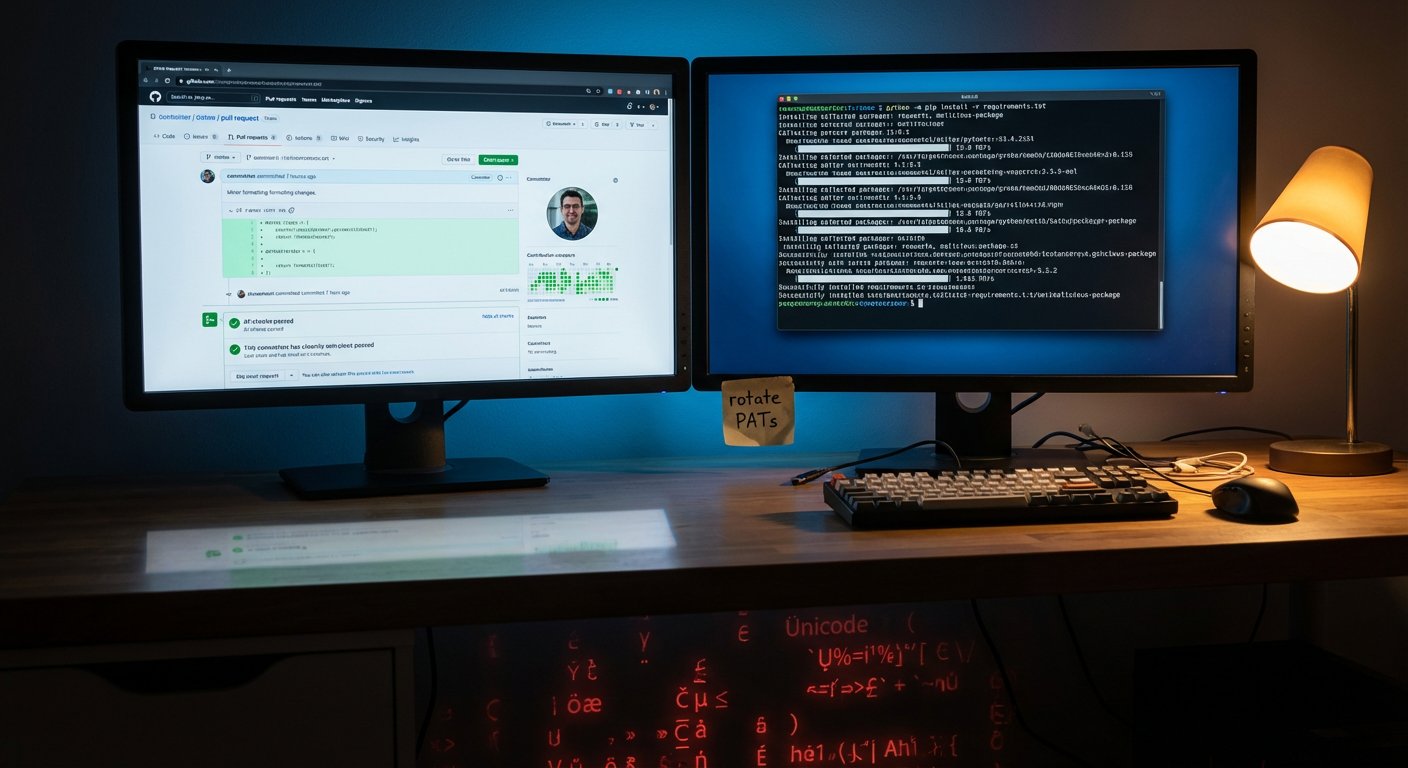
GlassWorm Is Hiding Malware in Invisible Code and Pushing It Into Your Python Repos
GlassWorm steals GitHub tokens, then injects malicious code written in invisible Unicode characters into repos developers already trust. 151 packages hit in one week.
Read More
The Week Trust Kept Breaking
Iranian wipers, poisoned dev tools, AI agents as attack surfaces, patches that never stopped coming, and a ransomware negotiator working for the bad guys. Trust fell apart in every direction this week.
Read More
The Software You Trust Is Becoming the Attack: Two Supply-Chain Strikes in One Week
GlassWorm hijacked VS Code extension dependencies. AppsFlyer's SDK got compromised to serve crypto stealers. Both attacks exploited trust, not carelessness.
Read More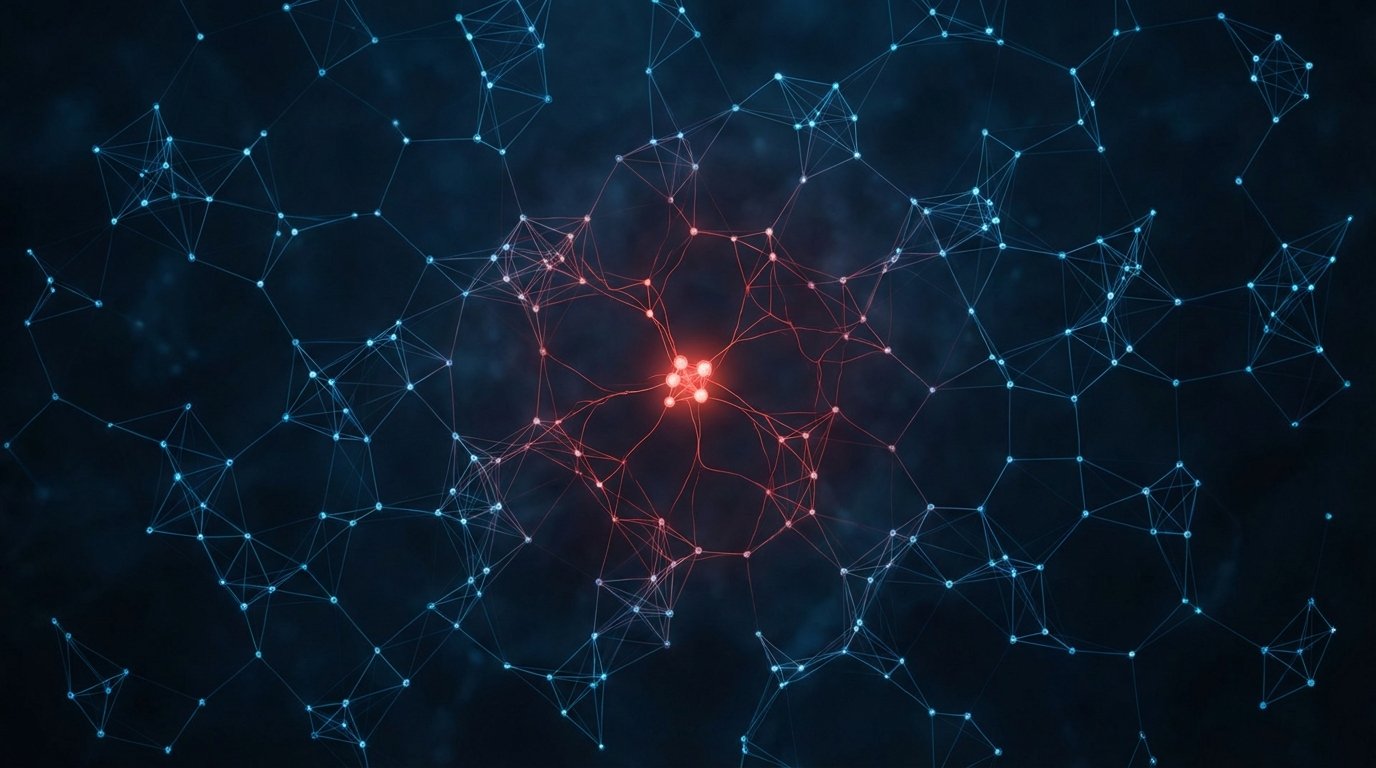
North Korea Behind Polyfill.io? Supply Chain Poisoning Just Got a State Sponsor
Forensic research links the Polyfill.io supply chain attack to a North Korean operative. The same week, a CVSS 9.8 RCE hits the simple-git npm library. Your dependency graph is your attack surface.
Read More
Developer Supply Chains Under Coordinated Assault: 88 Malicious npm Packages and a CVSS 9.8 in simple-git
PhantomRaven dropped 88 malicious npm packages targeting AWS credentials and CI secrets. A critical RCE in simple-git threatens millions of dev environments. Your developer toolchain is a target.
Read More
Your Vendors Got Hacked: Supply Chain Breaches Keep Piling Up
ShinyHunters hit 400 companies through Salesforce misconfigs. Cognizant lost 3.4 million patient records. Ericsson got popped via a vendor. The supply chain is the perimeter now, and it's breaking.
Read More
Your AI Assistant Is an Attack Surface Now
Exposed admin panels leaking API keys, prompt injection as a supply chain weapon, fake installer packages on npm, and nation-states using AI to hack at scale. AI agents just became everyone's security problem.
Read More

