John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
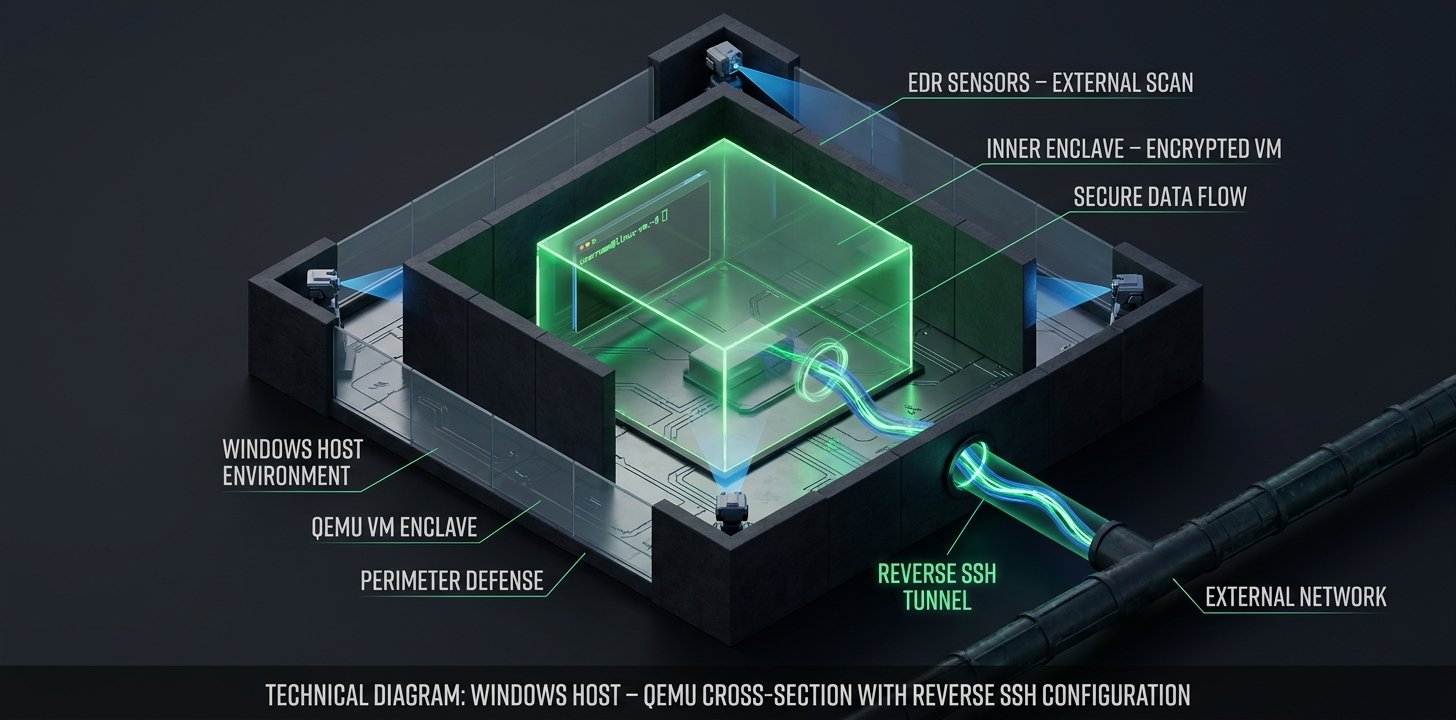
Defenders are used to looking for malicious scripts and binary signatures. But what if the entire attack is running inside a legitimate virtual machine that your security software cannot see?
The Payouts King ransomware group is doing exactly that. They gain initial access and then install QEMU, a trusted virtualization tool. Inside QEMU, they boot a tiny Linux OS that sets up a reverse SSH tunnel.
To your EDR, it just looks like a signed virtualization binary doing its job. Inside that container, the attackers are free to move laterally and prepare their encryption routine without tripping any alarms.
It is “Living off the Land” taken to the extreme. If you see QEMU running on a server that has no business hosting virtual machines, you need to treat it as a critical priority alert. The attackers have built their own room inside your house, and they have already locked the door.
Learn how to detect the QEMU virtualization backdoor before the encryption starts