John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com

Future-Proof Ransomware and AI Avatars: The Cyber R&D Pipeline Is Open
Kyber ransomware just started using post-quantum crypto to lock files forever. Meanwhile, BlueNoroff is using AI to impersonate your CEO on live Zoom calls.
Read More
Helpdesk Squeeze: BlackFile and the Vishing Revival
A new extortion group called BlackFile is making millions by doing something shockingly low-tech: calling your helpdesk and asking them to hand over access.
Read More
The Printing Provider Pivot: Concentration Risk Hits US Banks
Citizens Bank and Frost Bank customers had their data stolen through outsourced printing and tax fulfillment vendors. Everest ransomware is targeting the boring middle layer.
Read More
The Billion-Dollar Bill: Why the Cost of a Breach Never Ends
A major breach cycle only lasts a week in the news but can last five years on the balance sheet. UnitedHealth spent $3.1 billion before the SEC fine even landed.
Read More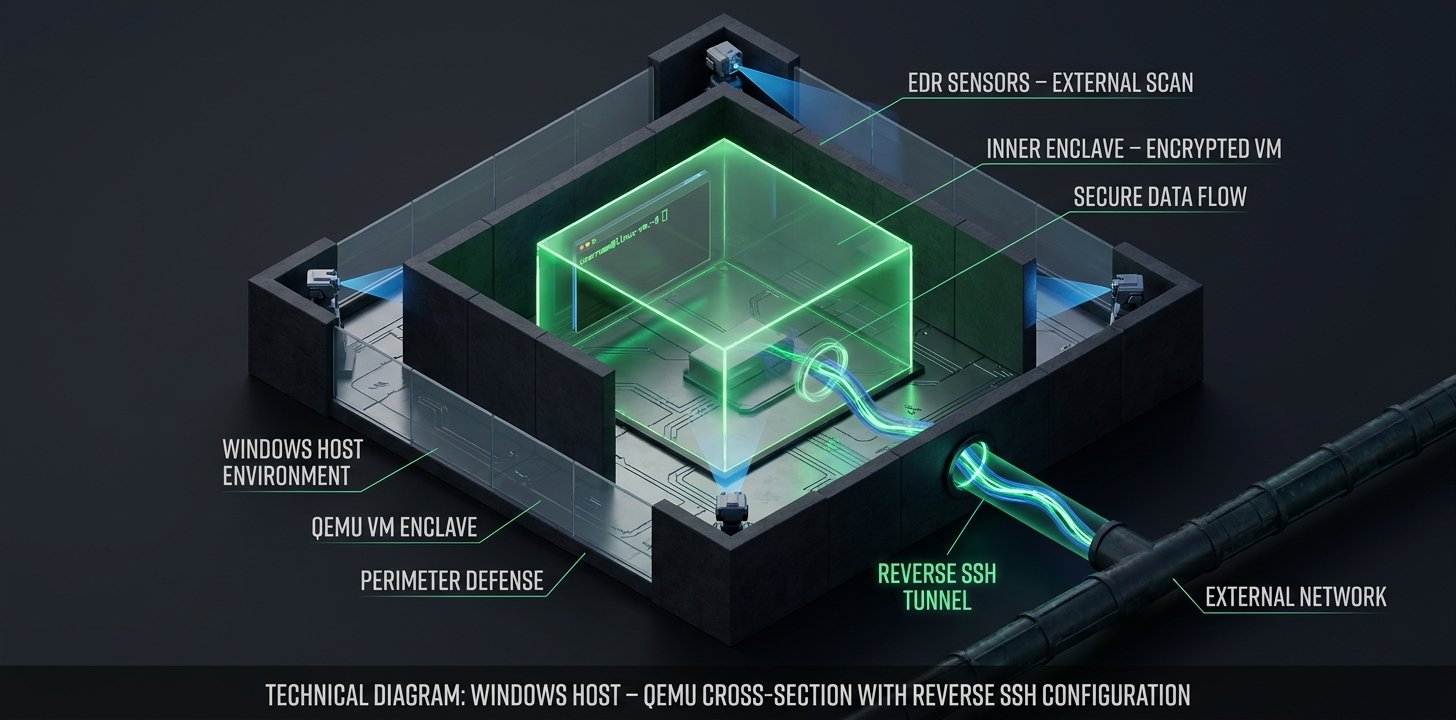
Payouts King Ransomware Built Their Own Room Inside Your Machine
The Payouts King ransomware group is running TinyCore Linux VMs inside QEMU on compromised Windows hosts, creating an EDR-invisible enclave for C2 and pre-encryption operations. Here's how it works and what to hunt for.
Read More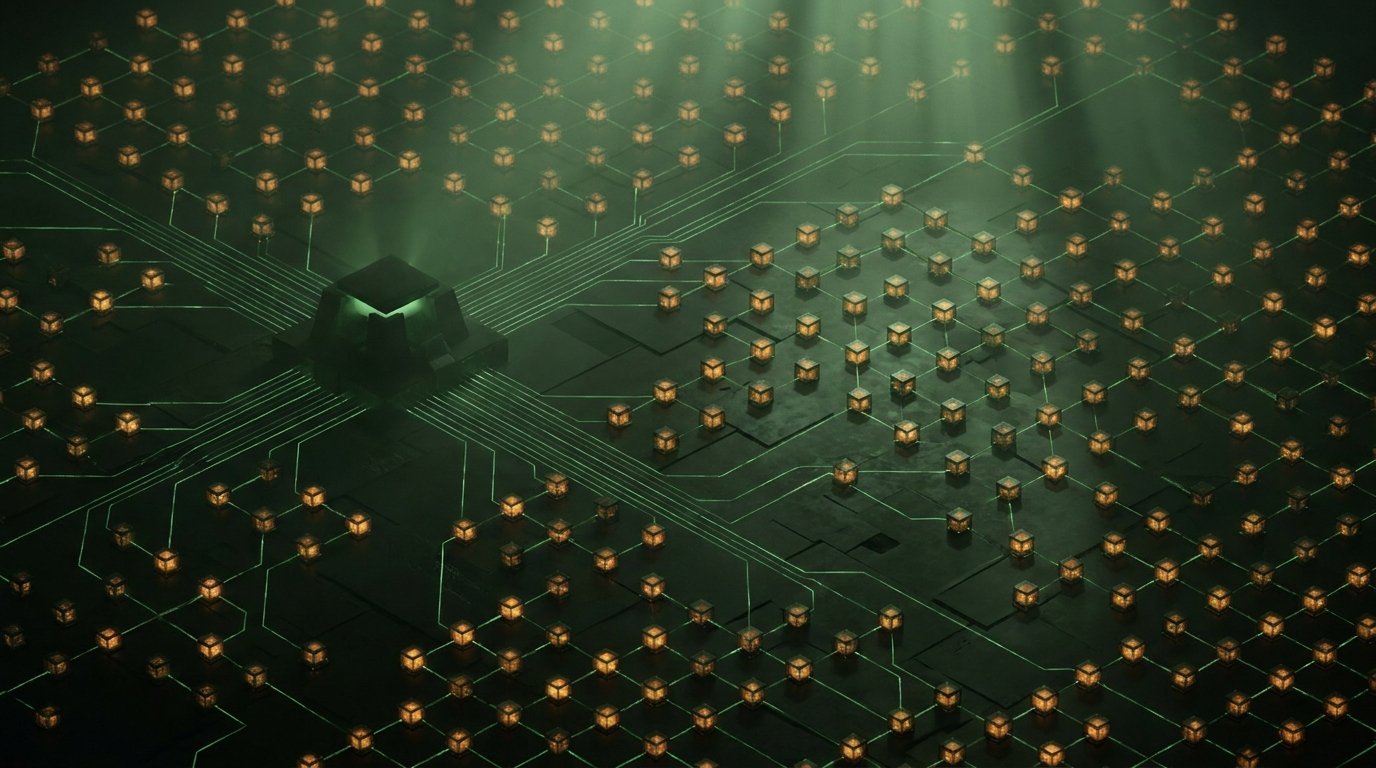
Machine-Speed Dwell Time: The Bot-Powered Recon of 'The Gentlemen'
A massive 1,570-host botnet linked to The Gentlemen ransomware has been unburied. These attackers are using automated proxy infrastructure to scout corporate networks before you even know they are there. Dwell time just got industrialized.
Read More
LockBit Won't Die: 207 Victims in 2026 and What Ransomware Resilience Actually Looks Like
Despite one of the most aggressive law enforcement operations in ransomware history, LockBit has claimed 207 victims in 2026. Winona County got hit twice in three months. The RaaS model is more durable than takedowns.
Read More
Your 2012 Security Debt Is Someone Else's 2026 Attack Vector
CISA added seven CVEs to its Known Exploited Vulnerabilities catalog. One of them was first patched in 2012. Attackers don't need zero-days when your backlog does the work for them.
Read More
The Healthcare Multiplier: One Ransomware Attack, Dozens of Hospitals
Ransomware hit ChipSoft, the EHR vendor behind HiX. One intrusion took down clinical systems across hospitals in the Netherlands and Belgium at the same time. That's the geometry attackers are after.
Read More
$20.88 Billion Gone: What the FBI's New Cybercrime Report Actually Says
The FBI's IC3 report crossed $20 billion for the first time. Crypto fraud, AI-enabled scams, and elder exploitation tell a story the headline number doesn't capture.
Read More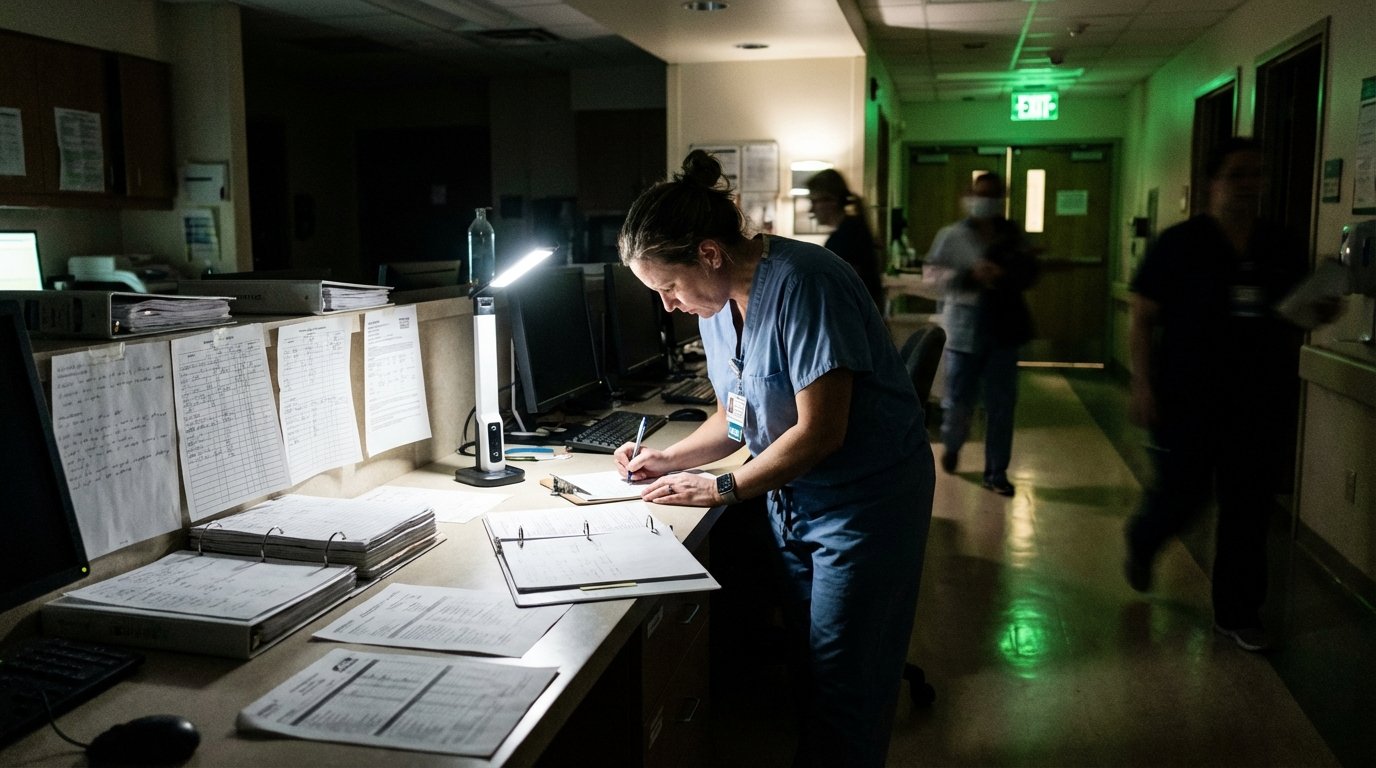
A Massachusetts Hospital Is Diverting Ambulances and Cancelling Chemo. The Attacks You Haven't Heard About Are Worse.
Brockton Hospital is running on paper after a cyberattack forced ambulance diversions and chemo cancellations. Health ISAC says multiple undisclosed incidents are hitting healthcare right now.
Read More
China's Ransomware Groups Are Using Zero-Days Now. That Changes the Math.
Microsoft links China-based Storm-1175 to Medusa ransomware using zero-day exploits, while Qilin deploys EDR-killing techniques before encryption.
Read More
The Man Behind REvil and GandCrab Finally Has a Name. He's Still Free.
Germany's BKA publicly identifies the leader behind GandCrab and REvil ransomware, confirming years of researcher suspicion.
Read More
TeamPCP's Criminal Empire Is Growing and Nobody Agrees Who's Running It
TeamPCP has evolved from cloud extortion to a criminal franchise operation with a wiper targeting Iran, a ransomware partnership with 300K affiliates, and public feuds with other threat actors.
Read More
Akira Ransomware Can Encrypt Your Network in Under an Hour
Akira ransomware completes full attack lifecycles in under an hour, making traditional detect-and-respond strategies basically useless.
Read More
LA Metro Is Still Rebuilding 1,400 Servers After a March Cyberattack
Two weeks after detecting unauthorized access, LA Metro is checking 1,400 servers one by one. WorldLeaks claims 160GB stolen. Trains and buses never stopped.
Read More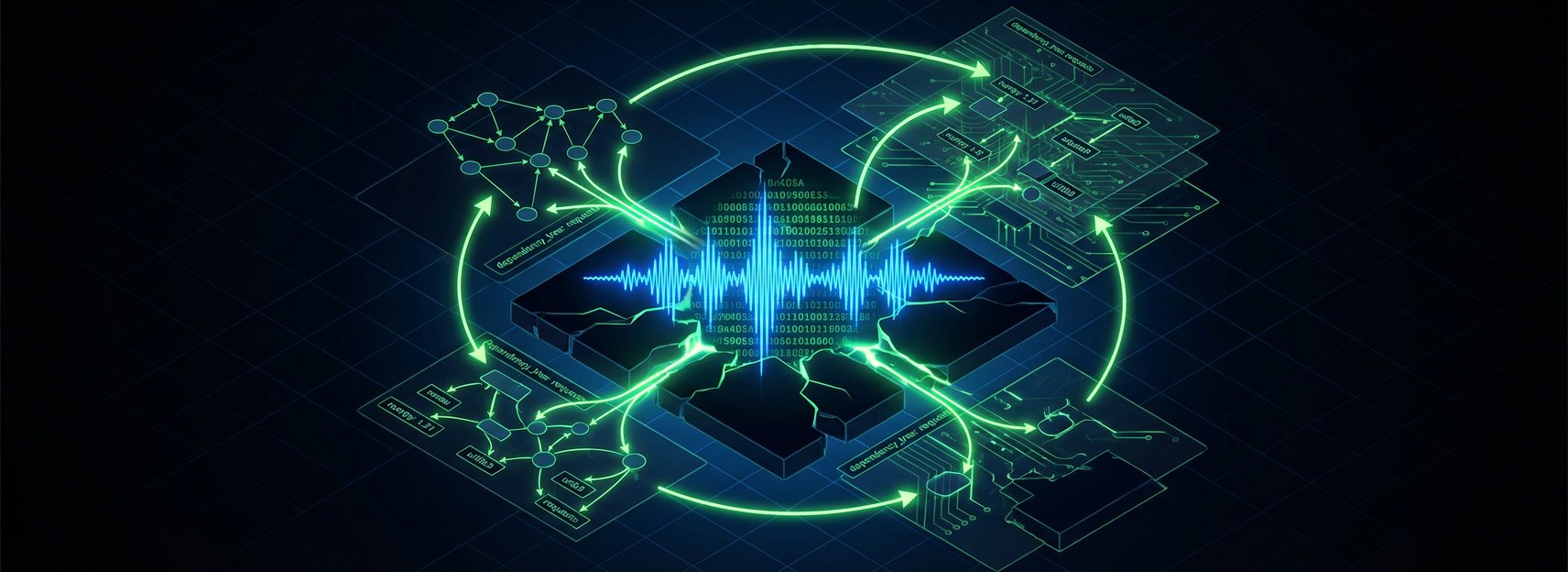
TeamPCP Is Back. Now It's Deploying Ransomware Through Your AI Libraries.
The supply-chain group that poisoned Trivy last week just hit LiteLLM and the Telnyx SDK, hid their payload in WAV audio files, and announced a ransomware affiliate partnership.
Read More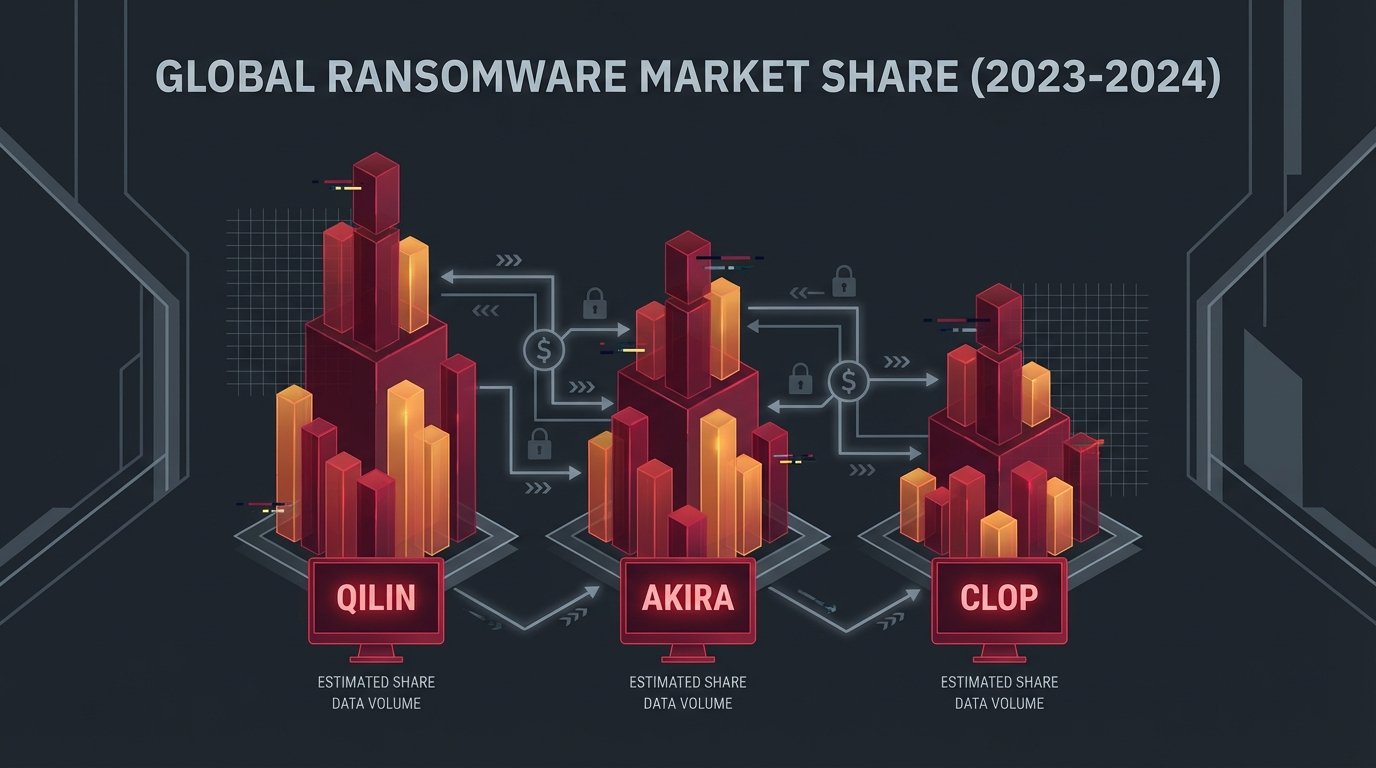
Three Ransomware Gangs Own a Third of North America's Cybercrime. What That Means for Your Risk Model.
Qilin, Akira, and Clop together claimed roughly 34% of all recorded North American ransomware incidents in 2025 -- and that concentration is actually something defenders can use.
Read More
The Progress We Thought We Were Making Against Hackers? It Just Went Backward.
Dwell time reversed in 2025, and the reason why tells you exactly which threats most security programs are not built to catch.
Read More
It Was a Good Week to Be a Federal Prosecutor
Two cybercrime sentences landed in the same week: 81 months for the access broker who sold entry into Yanluowang's victims, and 2 years for the operator of the Mario Kart botnet that extorted more than 70 US companies.
Read More
TeamPCP Is Not a Hacker Group Anymore. It's a Cloud Crime Platform.
TeamPCP has graduated from opportunistic attacker to full-spectrum criminal platform -- with blockchain C2 that law enforcement can't seize and a live ransomware affiliate program that costs $250 to join.
Read More
Mario Kart Got Two Years. The Guy Who Sold the Keys Got Nearly Seven.
Two Russian cybercriminals were sentenced the same week. One ran a botnet that hit 72 US companies and got 2 years. The other sold network access to ransomware crews and got nearly 7. The gap says something real about how DOJ views the ransomware supply chain.
Read More
Ransomware Hits Spain's Largest Fishing Port, Forcing Manual Operations
A ransomware attack knocked out digital systems at the Port of Vigo on March 24, 2026, forcing staff to revert to paper logs and phone calls. No group has claimed the attack.
Read More
Russian 'Key Seller' Who Helped Ransomware Gangs Break Into Victims Gets Nearly 7 Years
Aleksei Volkov, a 26-year-old Russian initial access broker for the Yanluowang ransomware gang, was sentenced to 81 months in federal prison and ordered to pay over $9 million in restitution. He made one mistake: he left Russia.
Read More
M-Trends 2026: The 22-Second Stat Everyone Is Misreading
Mandiant's M-Trends 2026 report is getting misquoted everywhere. The 22-second ransomware handoff is real -- but it's not what you think, and the dwell time stat buried in the report is scarier.
Read More
Operation Synergia III: 45,000 Malicious IPs Down, 94 Arrested, 72 Countries In
Interpol's Operation Synergia III ran six months across 72 countries, sinkholed 45,000 malicious IPs, and made 94 arrests. International cybercrime enforcement is getting better at this.
Read More
The Week the Infrastructure Fought Back (and Lost)
The week of March 16-22 hit management planes, identity infrastructure, and security tooling itself -- and North Korea kept hiring.
Read More
Interlock Ransomware Had a Cisco Firewall Zero-Day Before Anyone Knew It Existed
The Interlock ransomware group exploited a critical Cisco ASA/FTD zero-day for weeks before disclosure, marking a real shift as criminal groups gain access to capabilities once reserved for nation-states.
Read More
He Hacked Companies, Then Billed Them $75 Million to Recover From His Own Attacks
Angelo Martino allegedly orchestrated ransomware attacks and then helped victims pay ransoms through DigitalMint -- the firm where he worked. Federal charges now implicate the co-founder too.
Read More
Breach Disclosure Lag Is Becoming the Real Story in Financial Supply Chains
The Marquis breach started with a ransomware attack. The damage is still accumulating months later -- not because of what happened technically, but because of how disclosure was handled.
Read More
Zero-Day by Default: Why Cisco FMC Should Reorder This Week's Patch Queue
Interlock operators have been exploiting a Cisco FMC zero-day since January. If you're still sorting patch queues by CVSS score, that's the problem.
Read More
Ransomware Is Getting Less Profitable and More Prolific
Mandiant's latest report shows ransomware payments declining while victim counts hit record highs. The ecosystem isn't dying. It's fragmenting faster than defenders can track.
Read More
The Week Trust Kept Breaking
Iranian wipers, poisoned dev tools, AI agents as attack surfaces, patches that never stopped coming, and a ransomware negotiator working for the bad guys. Trust fell apart in every direction this week.
Read More
INTERPOL Just Sinkholed 45,000 Criminal IPs and Arrested 94 People Across 72 Countries
Operation Synergia III was one of the biggest cybercrime infrastructure takedowns ever. 45,000 malicious IPs redirected, 94 arrests, 72 countries involved. Here's what that actually means.
Read More
The Insider No One Suspected: DOJ Says a Ransomware "Helper" Was Running the Attack
A ransomware negotiator was secretly feeding BlackCat operators confidential victim data to jack up ransom payments. The DOJ just charged him.
Read More
AI Is Now Both the Weapon and the Target
Slopoly is AI-generated malware used in a live ransomware attack. Microsoft Copilot can be hijacked through emails you just receive. AI security isn't future-tense anymore.
Read More
The Ransomware 'Negotiator' Was Running the Attack: DigitalMint's $75M Double Cross
Federal charges reveal DigitalMint's ransomware negotiators were allegedly running the attacks themselves. The second employee charged in the same operation. This wasn't a rogue employee. It was the business model.
Read More
Veeam Has Seven Critical RCE Flaws and Ransomware Operators Are Paying Attention
Seven simultaneous unauthenticated RCE vulnerabilities in Veeam Backup & Replication. This is a ransomware operator's wishlist, and it all dropped at once. Patch now.
Read More
ClickFix Is the Social Engineering Trick That Took Over 2026
A dead-simple social engineering trick is showing up everywhere in 2026. Users paste a command into PowerShell or a Run dialog and boom, malware runs. Three separate campaigns hit this week alone.
Read More