John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
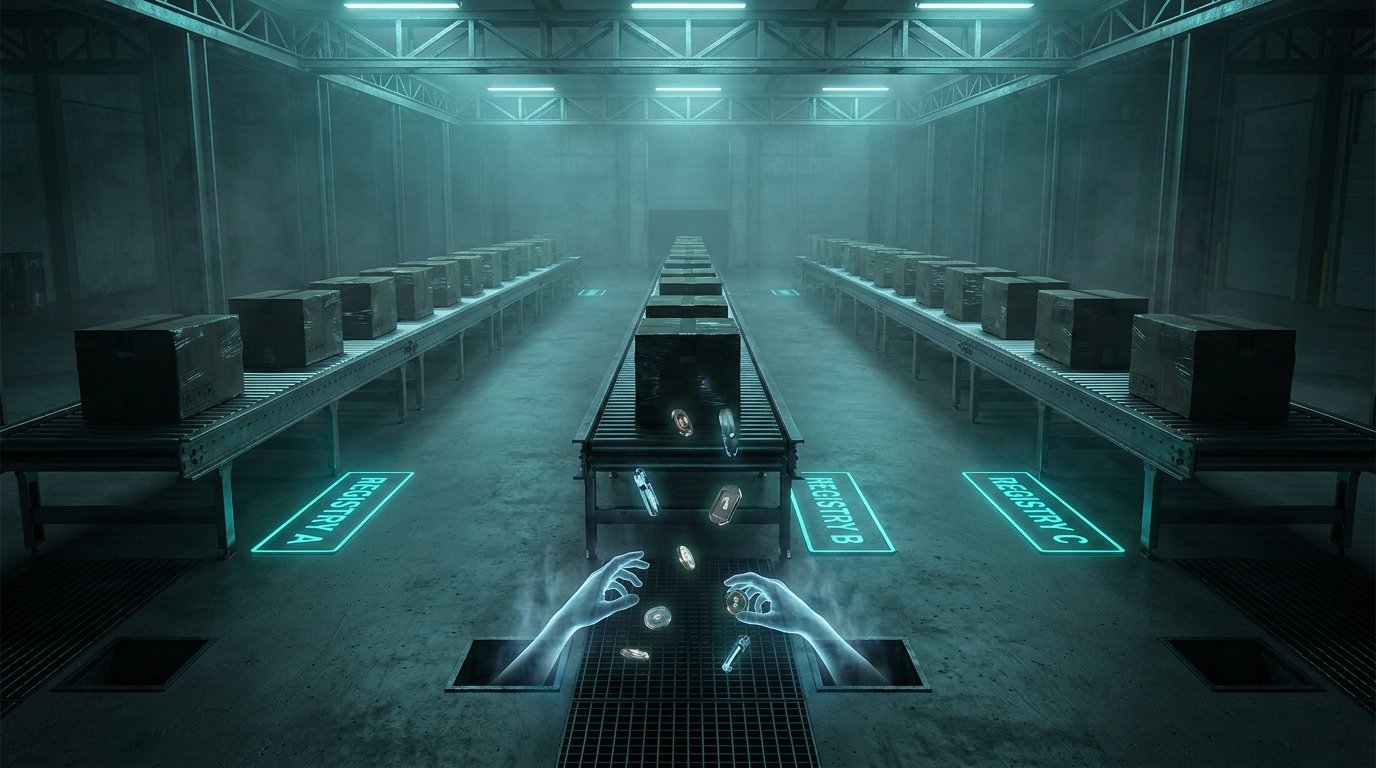
In a single 48-hour window, attackers didn’t just target one platform. They hit npm, PyPI, and Docker Hub at the same time. This was a coordinated, industrial-scale harvest for secrets—cloud keys, crypto wallets, and CI/CD tokens.
The highlight of the mess? The popular AI library Xinference was poisoned on PyPI. The attackers compromised a bot account that had been sitting dormant for months and used it to inject malware into the __init__.py file. That means the second you import the library, your AWS and Kubernetes credentials are out the door. It’s a targeted strike on AI/ML environments, which are usually swimming in high-value credentials.
Then there’s the Docker Hub irony: someone trojanized the Checkmarx KICS scanner. Imagine pulling a security tool to scan your code for leaks, only to have that tool steal your secrets instead.
We’re also seeing self-propagating worms on npm that steal your tokens and then try to push malicious code into every other repo you can reach. It turns your own CI/CD pipeline into a delivery system for the malware.
If you haven’t rotated your developer keys in the last couple of days, you should start there. Lock your dependencies by hash, not just version, and don’t trust a tool just because it has a “security” label on it.