John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
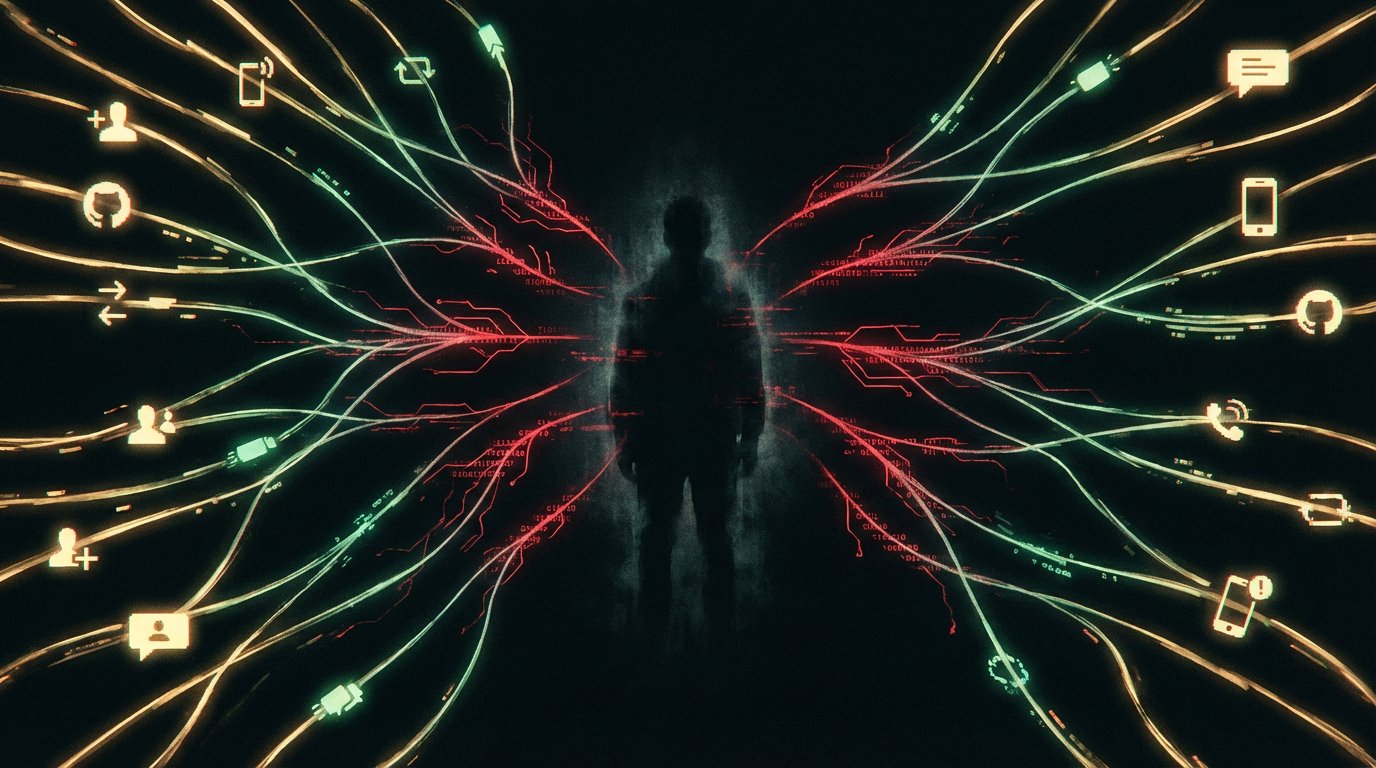
Four campaigns in the news today with nothing obvious in common. Except they’re all built on the same idea: find something the target already trusts and use it as the delivery mechanism.
North Korea’s APT37 adds people on Facebook. Builds a real-feeling relationship over weeks. Then delivers RokRAT. The friendship is the attack.
Cisco Talos documented a technique where attackers post phishing links inside GitHub issues and Jira tickets, then let GitHub and Atlassian send the notification email. Those emails pass SPF. They pass DKIM. They pass DMARC. Because they’re genuinely from GitHub. On a single day in February, about 2.89% of all observed GitHub emails were tied to this abuse.
In a conflict zone, a fake app impersonating Israel’s rocket alert system installs spyware. The urgency of a war zone is the lure. People install it because not installing feels more dangerous.
And Pushpaganda uses AI-generated fake news articles to infiltrate Google Discover, the personalized feed on every Android home screen. Gets users to enable push notifications. Then runs scareware and ad fraud indefinitely.
Different actors. Different targets. Same logic: defenses are built to stop strangers, not the things you already let in.
How all four campaigns exploit trust as the primary attack surface