John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
Someone has been inside Vercel’s Google Workspace for the better part of two years. This was not a failure of their firewall. It was a failure of the upstream supply chain.
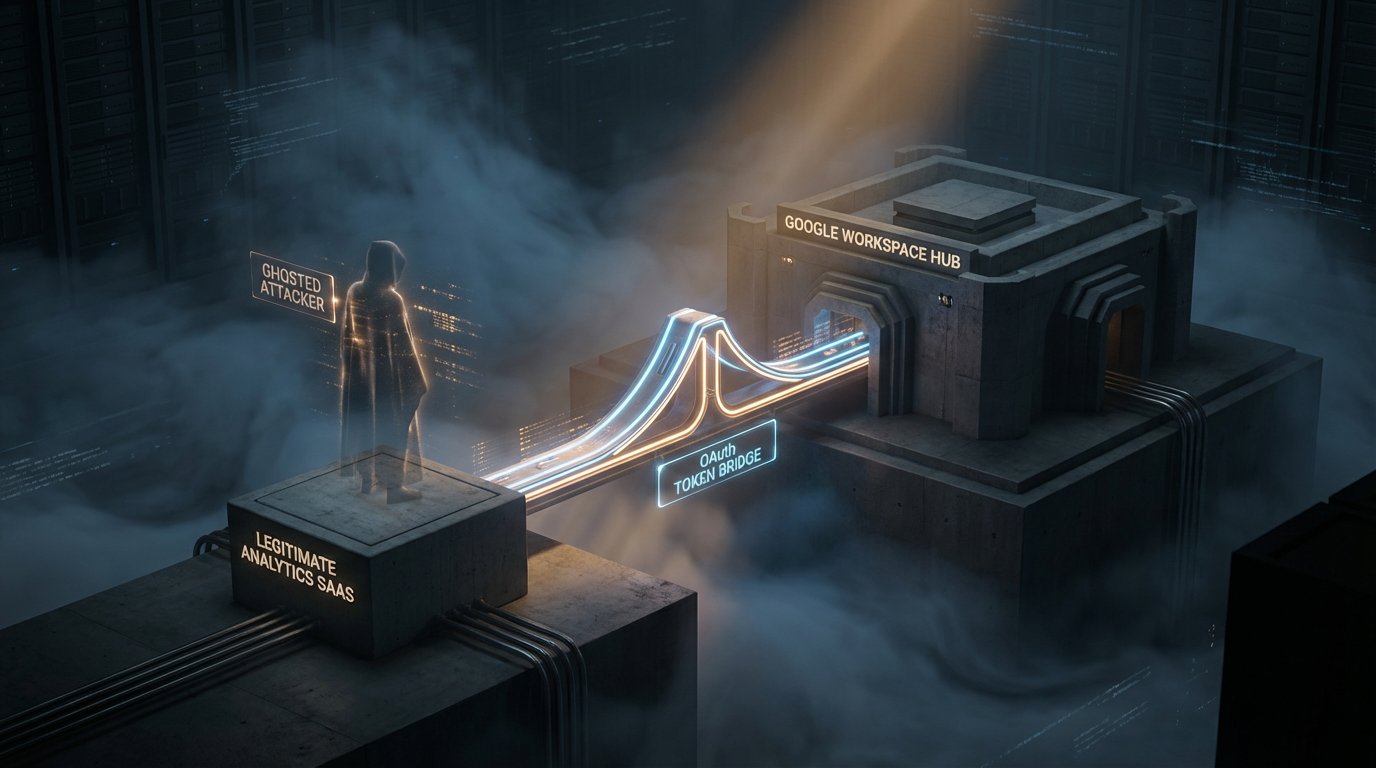
A third-party analytics provider called Context.ai was breached. Because a Vercel employee had integrated this vendor into their environment with broad OAuth permissions, the attacker inherited that access. The intrusion began in June 2024 and was only disclosed this month.
That length of dwell time should make any security team feel sick.
Vercel is the infrastructure backbone for hundreds of thousands of companies. An attacker holding a quiet, privileged position for 22 months has enormous value for credential harvesting and pipeline observation. Platform environment variables were exposed. For a deployment platform, those variables often hold the keys to client database credentials and API secrets.
The analytics trap is real. We often approve these tools because they only watch data. But when you grant an analytics or AI tool OAuth access to your workspace, you are creating a persistent, credentialed relationship. You are trusting their security with your identity layer.
Audit your OAuth permissions today. Deleting an account does not fix this. You need to rotate every secret and environment variable that those tools ever had access to. Your perimeter is the sum of every credentialed relationship in your stack.
Check the official bulletin for the specific OAuth application ID you need to block.