John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
Your EDR isn’t broken. It’s just looking in the wrong place.
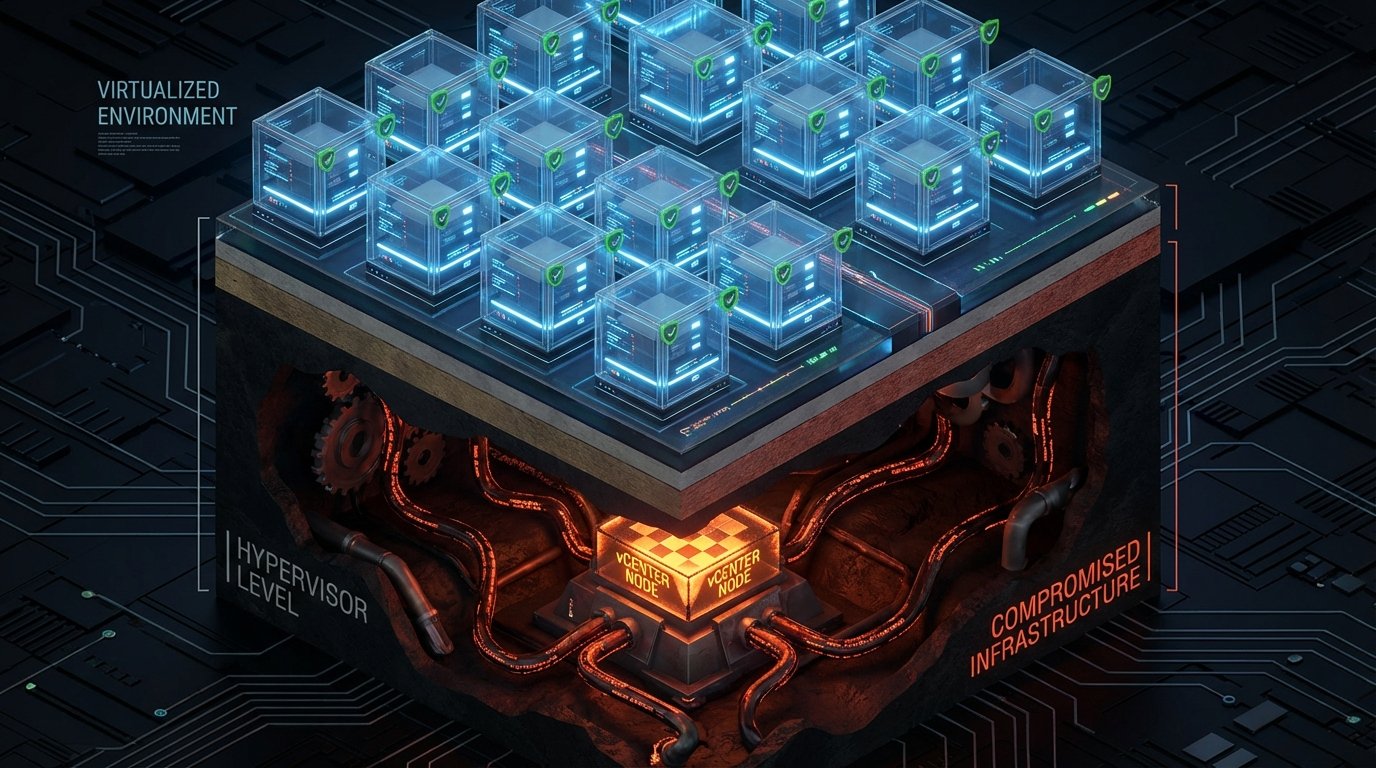
Google Cloud Threat Intelligence published a defender’s guide for BRICKSTORM, a suspected China-nexus espionage operation attributed to UNC5221. The malware targets VMware vCenter Server and ESXi hypervisors, establishing persistence at the virtualization layer. Every EDR agent you’ve deployed lives inside a virtual machine. BRICKSTORM lives underneath all of them.
Compromising vCenter is like getting the master key to an entire building. The attacker can control every ESXi host and guest VM, read VMDK files directly, and do it all without triggering a single EDR alert. Mandiant’s incident response data shows these operations regularly go undetected for more than a year.
No CVE to Patch Your Way Out
The frustrating part: the vSphere attack pattern doesn’t rely on a specific vulnerability. BRICKSTORM exploits weak security architecture. Default configurations, overprivileged service accounts, poor segmentation between management and production planes. You can’t wait for a patch. You have to harden the environment.
The group does use vulnerabilities when available (they deployed through a Dell zero-day in February 2026), but the vSphere playbook is about exploiting how organizations architect their virtualization, not the software itself.
What to Do Now
Run the publicly available Mandiant vCenter Hardening Script on GitHub. Segment your vCenter management network. Audit service account privileges. Enable and monitor vCenter audit logs. If you’re not monitoring the hypervisor layer, you’re not monitoring the thing that controls everything else.
Your endpoints are fine. It’s what’s underneath them you should worry about.
See the full defender’s guide and hardening framework for vSphere environments