John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com

Persistent Espionage: Mustang Panda's LOTUSLITE Campaign Hits Banking
A refreshed LOTUSLITE variant from Mustang Panda is targeting Indian banks and South Korean policy groups. Nation-states aren't extortionists. They're collectors. And they're patient.
Read More
Adversarial Distillation: The Industrial-Scale Theft of Frontier AI
The White House has officially flagged 'adversarial distillation' as a major threat. China is using tens of thousands of fake accounts to clone U.S. AI capabilities by strip-mining model outputs. This is model theft through the front door.
Read More
The AI Espionage Playbook: How a Hacker Used Claude and GPT-4.1 to Steal 415 Million Records
A threat actor used Claude Code and GPT-4.1 to automate a government-scale data breach in Mexico, exfiltrating 415 million records through 5,317 AI-generated commands. This is the first documented case of AI coding tools used as a nation-state espionage engine.
Read More
China's TA416 Is Back in Europe After Two Years. They Brought New Tricks.
TA416 has resumed targeting EU government and diplomatic organizations with PlugX malware, now abusing OAuth redirects to slip past traditional phishing defenses.
Read More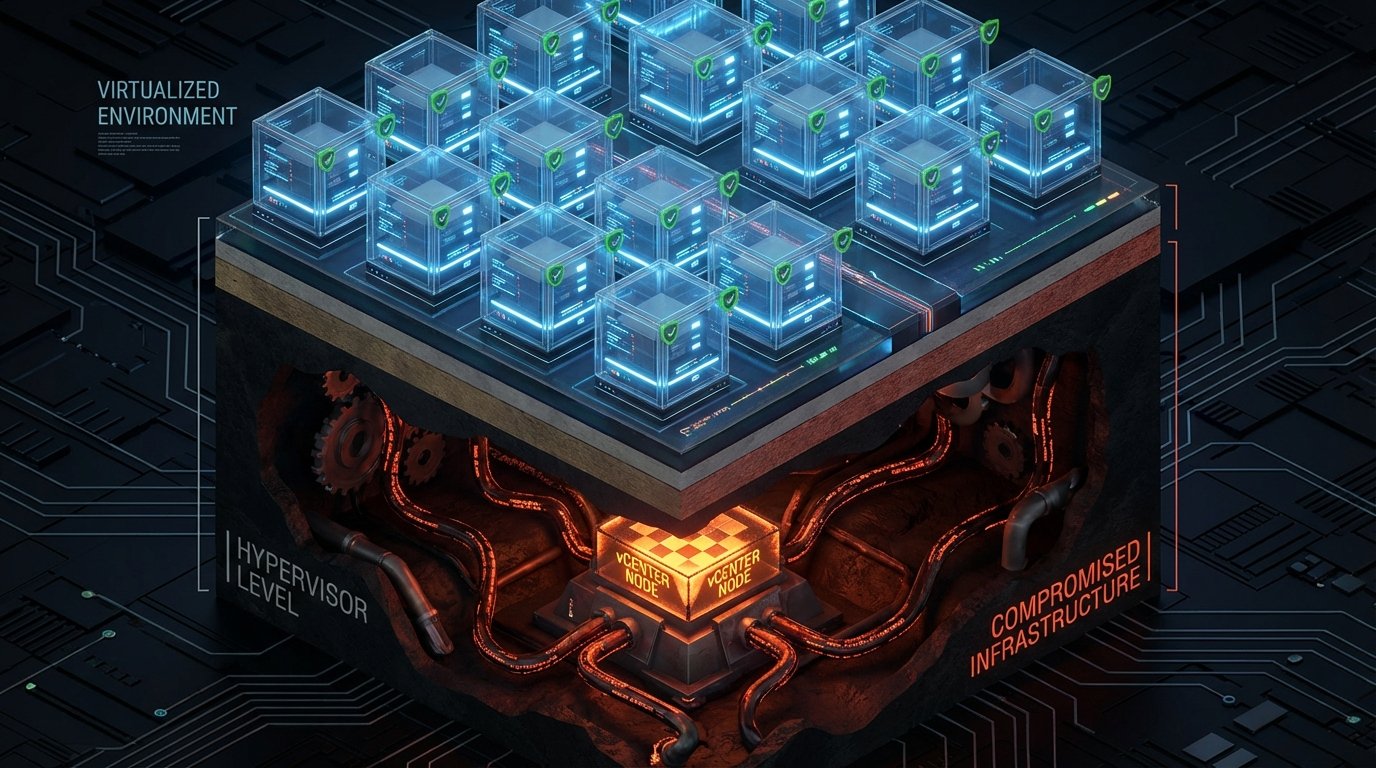
BRICKSTORM Hides Where Your EDR Can't See It
A suspected China-nexus espionage operation targets VMware vCenter and ESXi hypervisors, persisting at the virtualization layer where endpoint security is blind.
Read More
A Zero-Day Turned TrueConf's Update Channel Into a Malware Delivery System
Chinese-nexus actors exploited a zero-day in TrueConf to hijack the update mechanism and push trojanized updates to Southeast Asian government agencies.
Read More
FBI Says China Hacked Its Surveillance Systems, Triggers 'Major Incident' Classification
The FBI classified a suspected Chinese intrusion into law enforcement surveillance infrastructure as a FISMA major incident, forcing Congressional notification within days.
Read More
The Progress We Thought We Were Making Against Hackers? It Just Went Backward.
Dwell time reversed in 2025, and the reason why tells you exactly which threats most security programs are not built to catch.
Read More
Two Spy Campaigns, Two Completely Different Playbooks
A Chinese APT has been sitting inside Southeast Asian military networks for six years. Meanwhile, Russian hackers are stealing Signal accounts with fake support messages. Same goal, wildly different approaches.
Read More
China's Been Quietly Spying on Southeast Asian Militaries for Years
Unit 42 documented a suspected Chinese state-sponsored espionage campaign with years of undetected access to military networks across Southeast Asia. This is what patient intelligence collection looks like.
Read More