John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
Most phishing is a numbers game. FAUX#ELEVATE is not playing that game.
Before it does anything, this malware runs one check through Windows Management Instrumentation: is this machine on a corporate domain? If no, it exits. No payload, no trace. If yes, everything happens fast. About 30 seconds fast, according to Securonix.
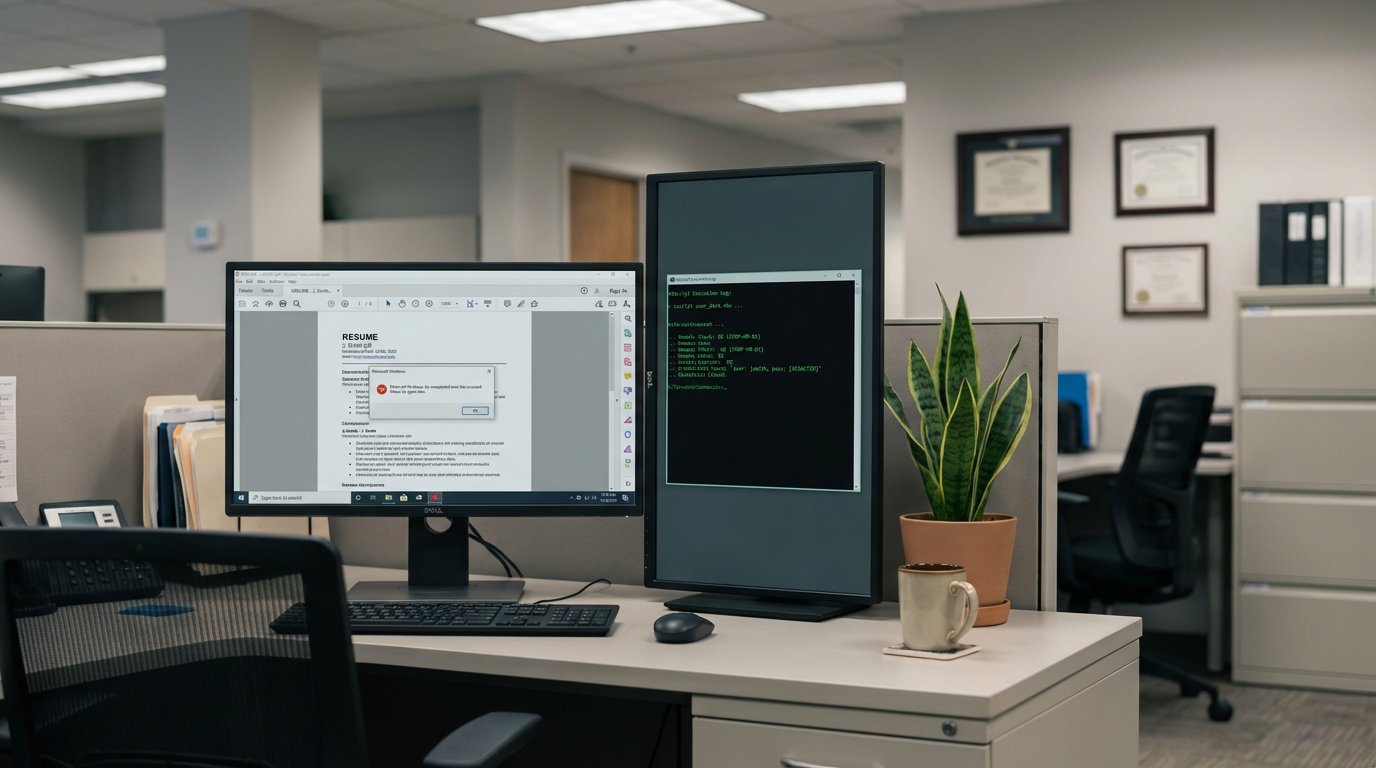
The lure is a VBScript file named nouveau_curriculum_vitae.vbs. A résumé, in French, targeting French-speaking corporate professionals. You work in recruiting, you open résumés all day. One lands from an applicant, you double-click it, an error message pops up, you assume the file is corrupted. You have no idea what just ran.
The script is 224,471 lines long. Only 266 of those lines are actual malicious code. The other 99.88% is pure garbage, random noise designed to make automated scanners choke. A signature-based tool is looking for a needle in a haystack made of fake needles.
Once the domain check passes, Chrome credentials are the first thing to go. FAUX#ELEVATE uses a component called ChromElevator to pull passwords, session tokens, and stored cookies – without admin rights. This is the part where “our users don’t have admin access” stops being a meaningful defense. ChromElevator doesn’t need elevation. It runs at the same permission level as the logged-in user, and that’s all it needs.
Stolen data goes out encrypted via SMTP. Meanwhile, XMRig fires up in the background and your HR person’s CPU starts mining Monero while they’re reviewing the next application.
HR and recruiting teams open attachments from strangers all day. That’s the job. FAUX#ELEVATE is built entirely around that fact. VBScript attachments shouldn’t reach inboxes. If your workflows require receiving files from external applicants, that’s a process worth reviewing right now.
See the full technical breakdown of FAUX#ELEVATE, including IOCs and detection guidance