John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
Developers trust GitHub by reputation. Star counts, active maintenance, alerts from maintainers, curated extension marketplaces. These aren’t naive shortcuts – they’re heuristics that made sense when the signals were real.
Every one of those signals is currently broken or being actively gamed.
Research from CMU’s STRUDEL lab, presented at ICSE 2026, documented 6 million suspected fake GitHub stars. Up from 4.5 million in earlier work. GitHub’s response to this as of today: silence. Criminal groups including TeamPCP are already buying stars to make malicious repositories look legitimate.
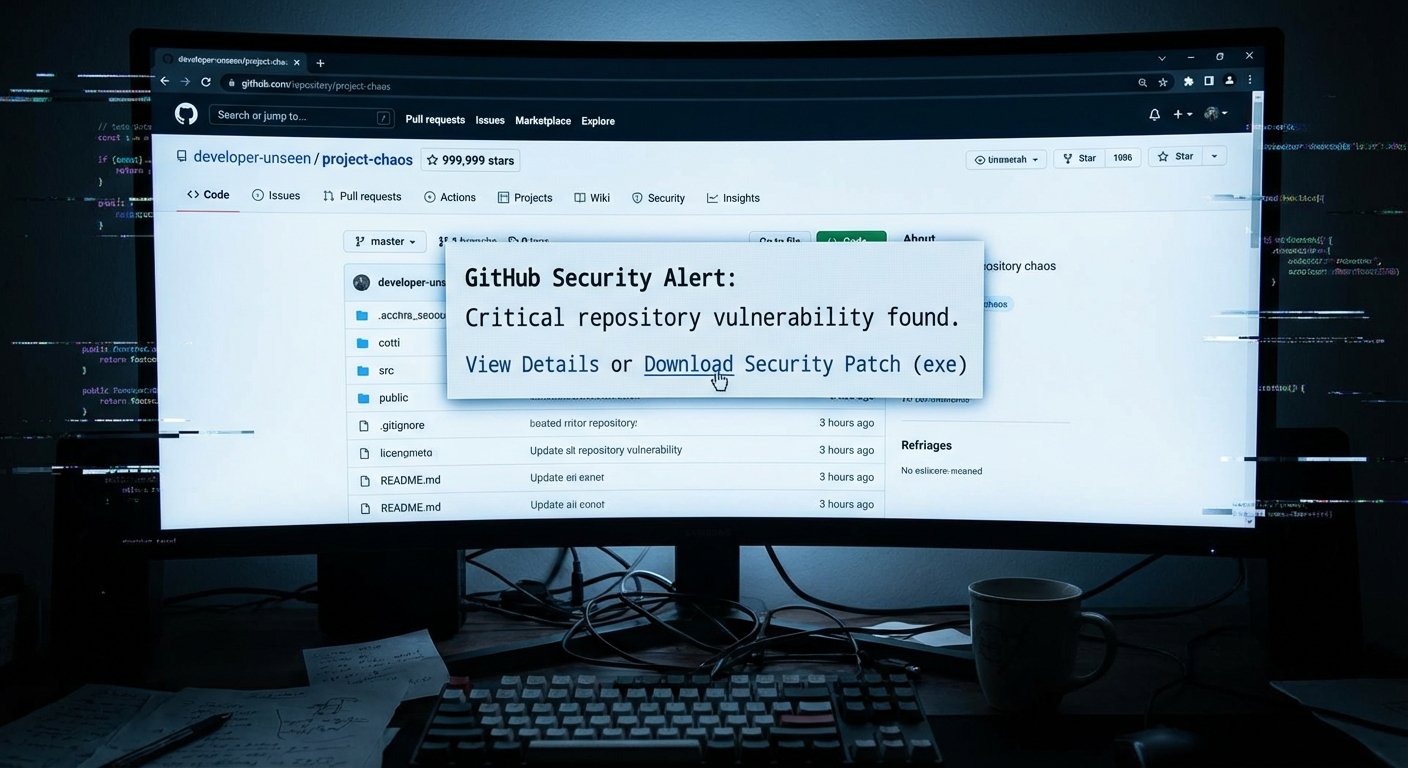
Then there’s the VS Code alert campaign. Attackers are posting in GitHub Discussions across multiple repositories, impersonating maintainers, using fake CVE identifiers to create urgency. Click the link, and you don’t go straight to a payload – you get routed through Google Drive and a redirect chain to a site that fingerprints you first. Timezone, locale, OS, user agent. Looks like a sandbox? You get a clean page. Looks like a real developer on a real machine? Payload.
What makes this particularly nasty is how GitHub Discussions email notifications work. Every post in a thread for a repo you’re watching generates an email. The attackers understood this. One malicious post reaches every watcher of that repo automatically. The platform did the distribution work for them.
Meanwhile, Open VSX – the VS Code extension registry – had a boolean logic bug that treated “no scanners configured” and “all scanners failed” as identical results. Both returned success. So extensions appeared to pass security scanning when scanning wasn’t actually running. A campaign called GlassWorm abused 72 extensions before the fix landed.
Stack all three together. Stars can be bought. Security alerts can be faked and distributed through legitimate infrastructure. Extension scanning can fail silently. The signals aren’t just imperfect – they’re under coordinated attack across multiple vectors at once.
What’s left to rely on? Code review. Dependency pinning. Behavioral monitoring. Treating every dependency update as hostile until proven otherwise. None of that is new advice. The context around it just changed.
How fake stars, fake CVE alerts, and a scanning bug quietly turned GitHub into an attack surface