John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
When law enforcement takes down malware infrastructure, they seize servers, suspend domains, pressure hosting providers. The C2 goes dark. The malware stops getting instructions.
GlassWorm’s developers thought about that.
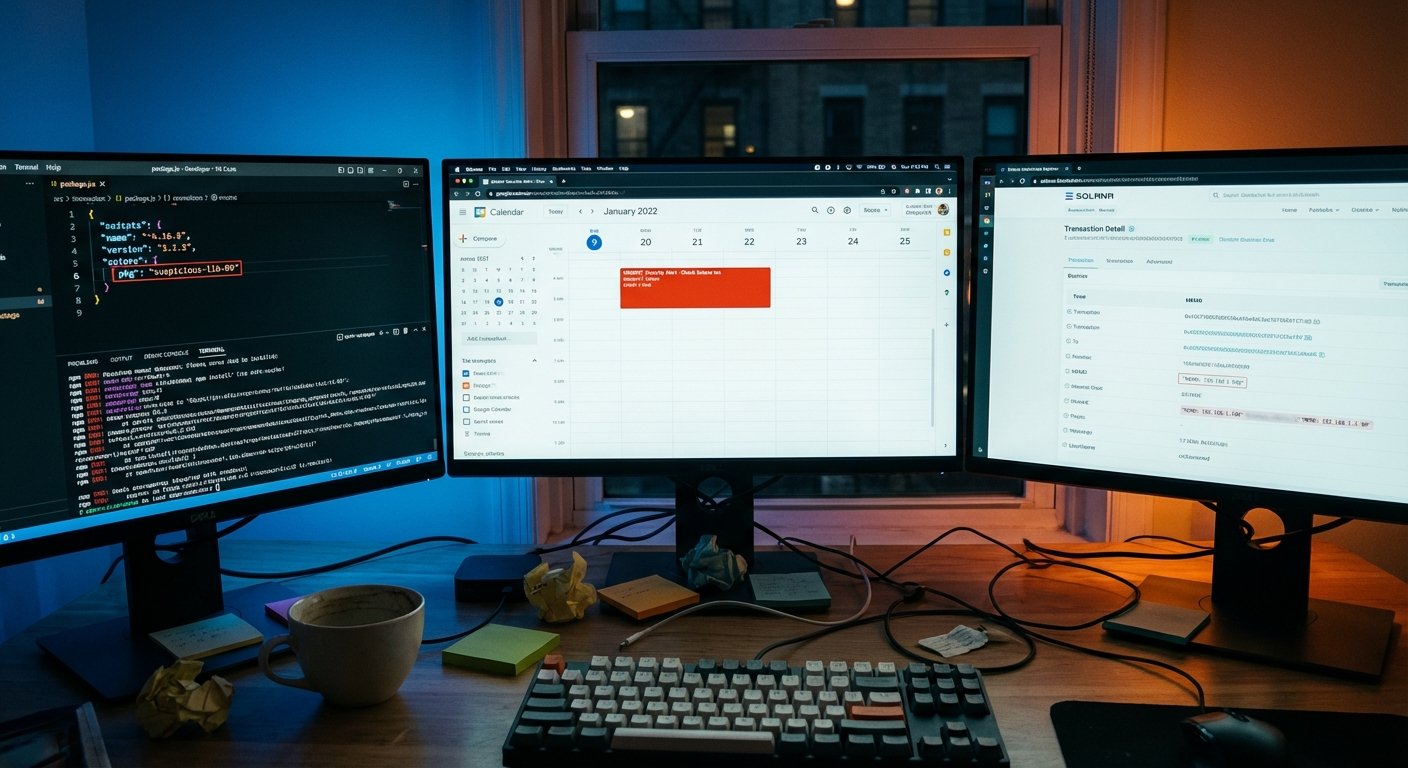
Their solution: hide the C2 address in a Solana blockchain transaction memo. You can’t seize a blockchain transaction. There’s no hosting provider to call. The data sits there permanently, readable by any node, with no authority to complain to.
Backup plan? The RAT payload’s address is embedded in a public Google Calendar event description.
How It Gets In
GlassWorm spreads through supply chain compromise. The attackers use stolen or hijacked maintainer accounts on npm, PyPI, GitHub, and the Open VSX marketplace to push malicious packages through channels developers already trust.
That’s the point. You’re not clicking a phishing link. You’re running npm install on a package that looks fine, from a maintainer account that was legitimate, in a registry full of legitimate software. The account was compromised, not the name.
Once on a system, GlassWorm logs keystrokes, dumps cookies and session tokens, captures screenshots, and phones home to the C2 address it read from the Solana blockchain. It also drops a fake Chrome extension disguised as an offline Google Docs viewer that harvests whatever it can reach from the browser.
Known exfiltration endpoint: 217.69.3[.]152/wall. Known payload server: 45.32.150[.]251.
The Blockchain Dead Drop
The malware doesn’t connect to a hardcoded IP. It reads a memo embedded in a Solana transaction, which contains the actual C2 address. The C2 can change by writing new transactions. But the memo can’t be deleted, and the chain can’t be seized.
Blocklisting known wallet addresses is possible but plays into the attackers’ hands. New wallet, same technique, problem persists.
The Google Calendar fallback works the same way. If the Solana address gets blocklisted, the malware reads the payload server address out of a Calendar event description. Defenders have to separately identify and block that URL, assuming they notice it at all.
Both approaches abuse infrastructure that’s trusted by default and hard to action against. Blocking Google Calendar in an enterprise environment has obvious downsides. Blocking all Solana lookups is blunt in a different way. The attackers made deliberate choices about which infrastructure would be hardest to disrupt.
The Hardware Wallet Angle
GlassWorm also delivers a .NET binary that targets hardware crypto wallets. If a Ledger or Trezor is connected, the malware shows a convincing fake error asking for the device’s 24-word recovery phrase. Ledger gets a “configuration error.” Trezor gets “Firmware validation failed.”
Handing over 24 words to any error screen, for any reason, gives an attacker permanent access to everything in that wallet. The malware skips infection on systems with a Russian locale, a standard tell for actors trying to avoid domestic legal exposure.
The Pattern Worth Naming
This is the second blockchain C2 story this week. CanisterWorm, the wiper tied to TeamPCP, used Internet Computer Protocol blockchain canisters for the same purpose. Different blockchain, different delivery, different payload, same core insight: immutable distributed ledgers are excellent places to hide addresses that can’t be taken down.
These campaigns aren’t connected. But two unrelated actors independently arriving at blockchain C2 means this is no longer one threat actor’s experiment. It’s an established technique.
For developers: verify maintainer accounts and watch for unexpected dependency additions. For security teams: add Solana blockchain lookups and unexpected Google Calendar API traffic to your anomaly detection. For anyone with a hardware wallet: the only legitimate reason a device asks for your 24-word seed phrase is initial setup. Any other time, it’s an attack.