John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
The attacks that are hardest to catch aren’t the ones that break things. They’re the ones that don’t.
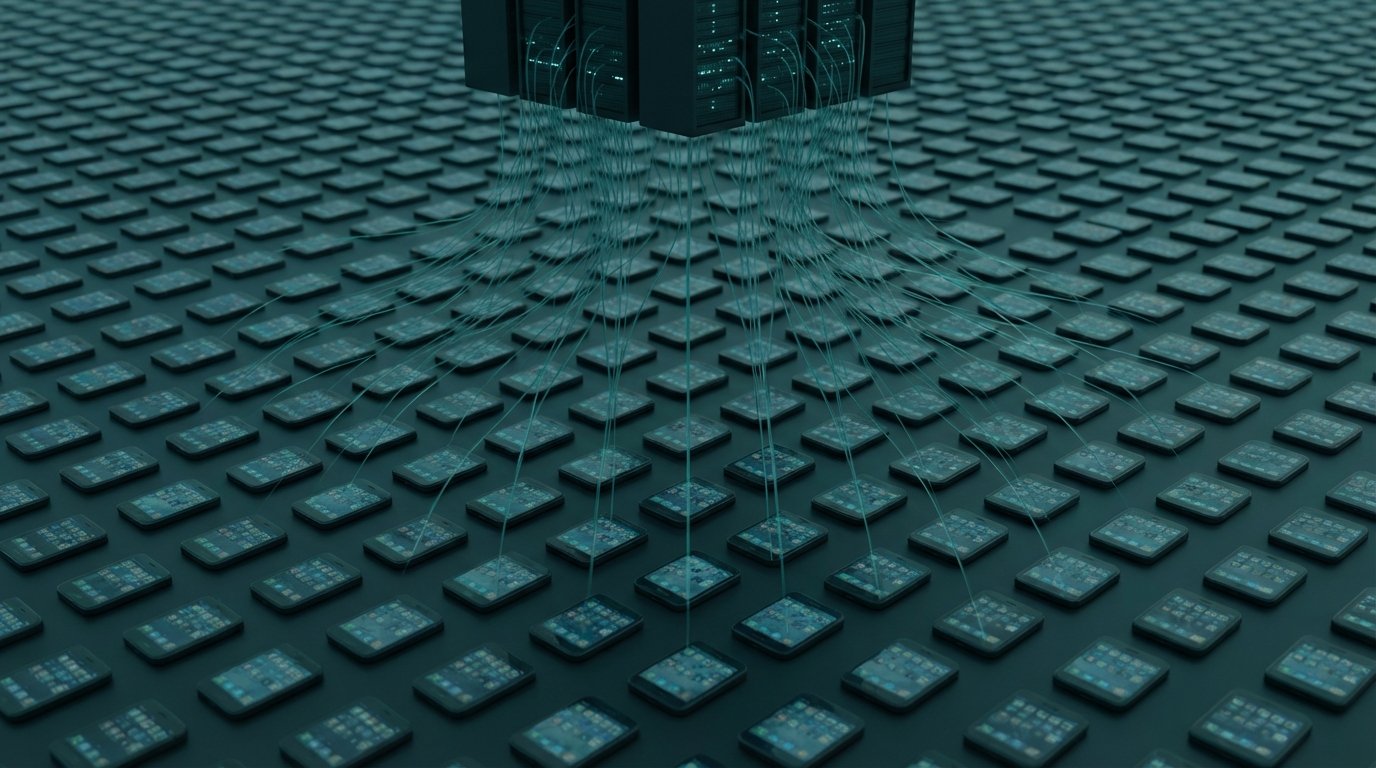
The Mirax Android RAT spread through Facebook and Instagram ads posing as a streaming app. 220,000 installs. Once on the phone, it doesn’t steal passwords or show ransomware banners. It turns your device into a SOCKS5 proxy node. Your phone keeps working. Somebody else’s traffic quietly flows through your IP address.
108 malicious Chrome extensions, all in the official Web Store, all reporting to the same command-and-control server. Published under five different developer identities to stay under the radar. Most stole credentials. Five of them abused Chrome’s own APIs to strip security headers before pages even loaded.
And then there’s FrostArmada. GRU Military Unit 26165, Fancy Bear, compromised roughly 18,000 home routers globally via a known TP-Link vulnerability and used DNS hijacking to intercept Microsoft 365 authentication traffic. The router kept working perfectly. It just had a different idea of where your login credentials should go. Operation Masquerade, a coordinated action by the FBI, UK NCSC, Microsoft, and Lumen’s Black Lotus Labs, shut it down this week.
Check your Chrome extensions. Reboot your router and verify the DNS settings. These aren’t exotic threats.
Full technical breakdown of all three campaigns and what you can actually do about them