John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com

Knock at the Door: Why Industrial Cyber Just Went Kinetic
German police are physically visiting factories to warn about software bugs while Swedish power plants dodge pro-Russian sabotage attempts. Industrial cybersecurity is no longer an IT issue, it is a national security emergency.
Read More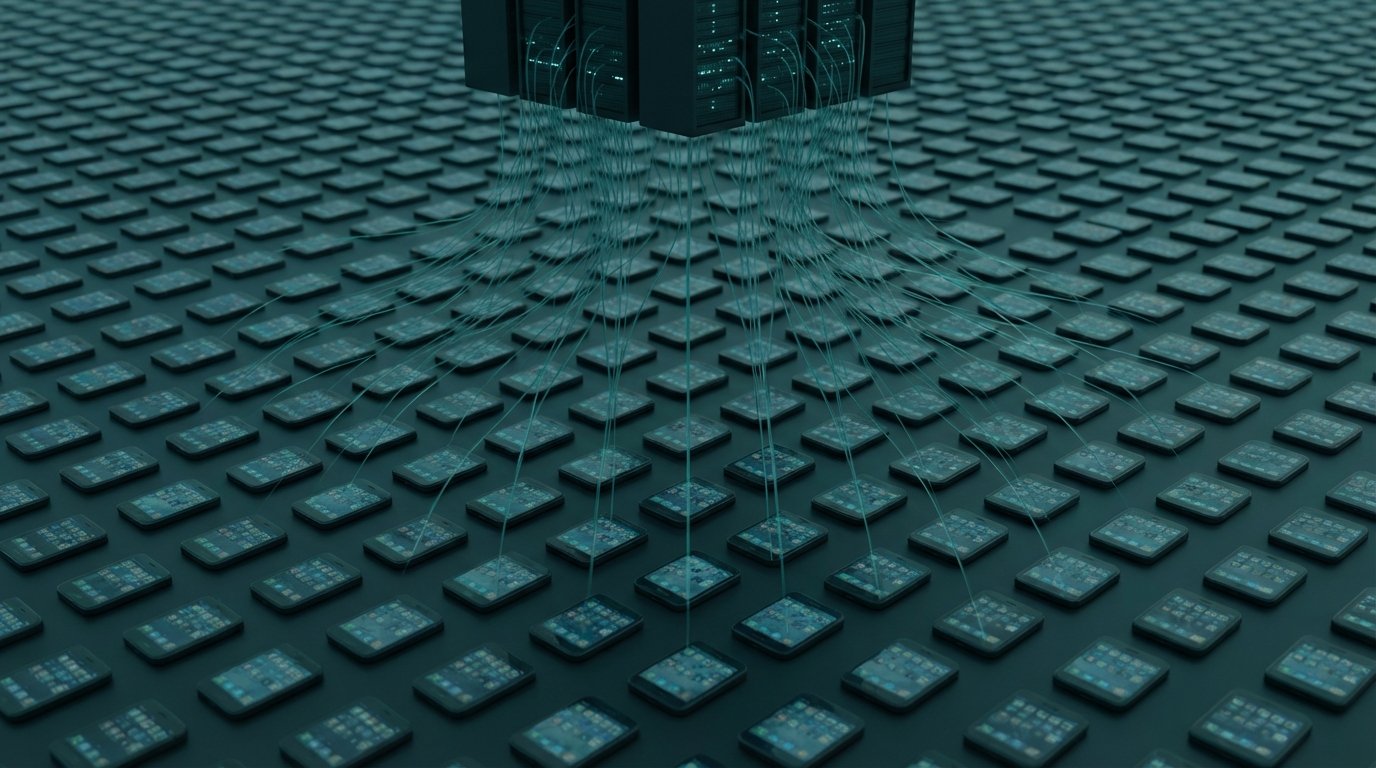
Your Phone, Your Browser, Your Router. All Still Working. All Compromised.
220,000 Android phones recruited into a criminal proxy network via Facebook ads. 108 Chrome extensions in the official Web Store harvesting Google and Telegram credentials. Russia's GRU running DNS hijacks through 18,000 home routers until law enforcement shut it down. Three campaigns, one pattern: your device keeps working while someone else uses it.
Read More
The FBI Used Your Router. They Had a Court Order. This Is the Third Time.
Operation Masquerade gave the FBI court authority to issue remote commands to privately owned home routers in 23 states, removing APT28's foothold. It worked. It also raises questions worth sitting with.
Read More
Russia's GRU Hijacked 18,000 Routers to Steal Microsoft 365 Tokens Without a Single Piece of Malware
APT28 changed the DNS settings on 18,000 home routers and stole Microsoft 365 tokens after users completed MFA. No malware needed. Your second factor was irrelevant.
Read More
Russian Hackers Are Going Back to Old Victims to Check If the Door's Still Open
CERT-UA warns APT28 and Void Blizzard are revisiting old compromises, testing dormant access, and calling targets directly in fluent Ukrainian. Incident response has an expiration date. Attackers don't.
Read More
APT28's Covenant Trick and North Korea's AirDrop Hack: How Nation-States Borrow Their Tools
Russia's APT28 hijacked an open-source red-team tool to hit Ukraine. North Korea's UNC4899 used Apple AirDrop to break into a crypto firm. Both attacks exploit the trust we put in legit software.
Read More