John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
I haven't yet decided exactly what kind of content I intend to post here. I love cooking and taking pictures so initially I'll probably just share recipes, photos and that kind of thing.
If I really start using the space I may expand on the blog capabilities. For now I'm keeping it quite simple.

FedRAMP Says Authorized. That Doesn't Mean Enforced.
ProPublica raises questions about major cloud authorizations. Congress pressed on CISA staffing. Post-incident recovery data shows uneven performance long after disclosure. Compliance and enforcement capacity are not the same thing.
Read More
Geopolitics Landed in Your Hiring and Vendor Workflows Whether You're Ready or Not
Treasury sanctioned DPRK IT worker fraud facilitators with hundreds of millions in annual revenue tied to the ecosystem. Greek firms are scanning over conflict spillover. CISA says Iran hasn't spiked yet. Calibration matters, but so do controls.
Read More
Patch Cycles Are Now Running Behind the Exploit Curve
A GNU telnetd PoC is already circulating. CISA added another KEV entry. Rapid7 says exploited high/critical vulns surged 105% and attack timelines collapsed. Meanwhile teams are still digesting Microsoft's 83-vulnerability March dump.
Read More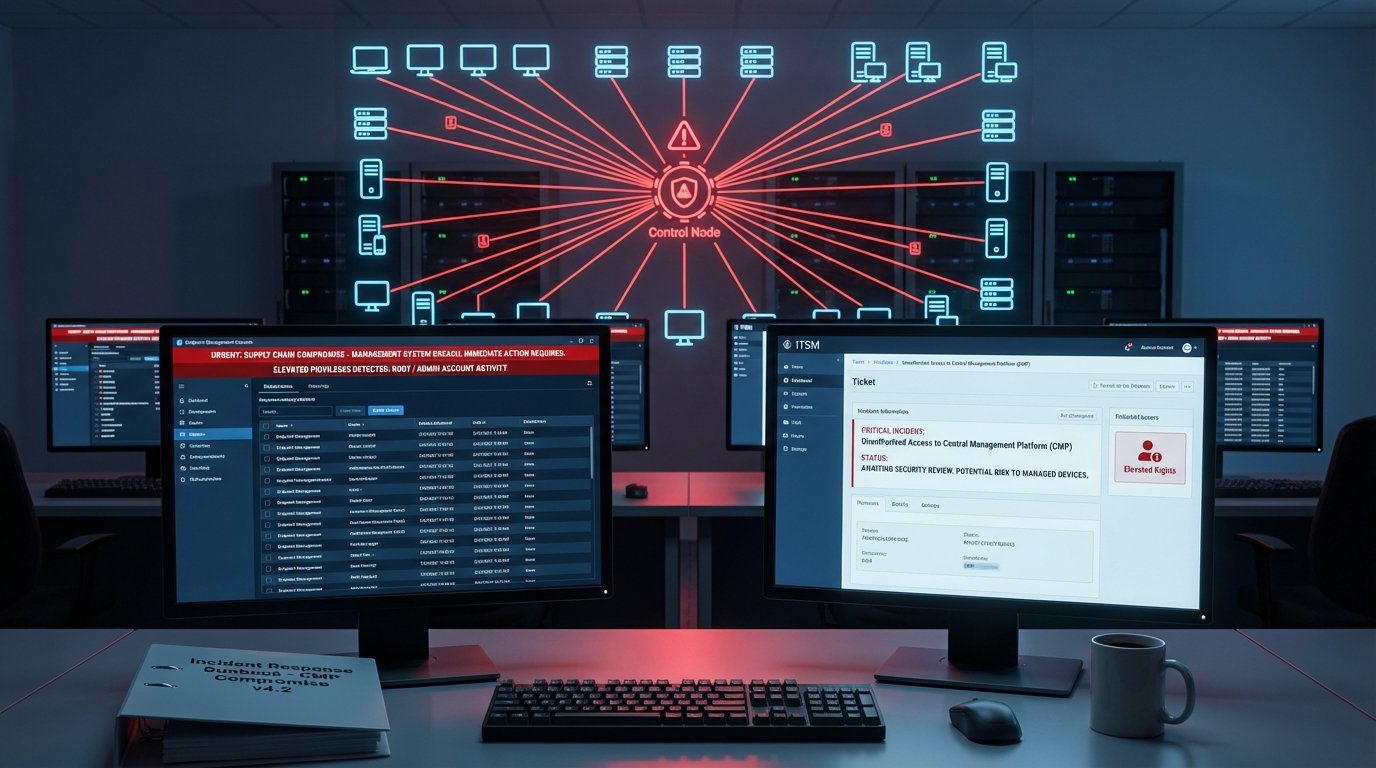
Your Management Stack Is the Shortcut Attackers Are Looking For
CISA flagged endpoint management systems after a real incident. Researchers dropped pre-auth RCE chains for BMC FootPrints ITSM. IP-KVM gear is a network takeover path. The pattern is clear: attackers go for the systems that control everything else.
Read More
FedRAMP's Trust Gap: When Technical Warnings Lose to Procurement Momentum
Federal cyber experts reportedly called Microsoft's cloud a 'pile of shit' -- and approved it anyway. That's not just a Microsoft story. It's a story about what certification badges actually mean.
Read More
Federal Cyber Reality Check: Capacity, Coordination, and Confidence Are Out of Sync
Staffing gaps, fuzzy lead-agency roles, and public messaging that doesn't always match operational uncertainty -- the layers of federal cyber aren't running in sync right now.
Read More