John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
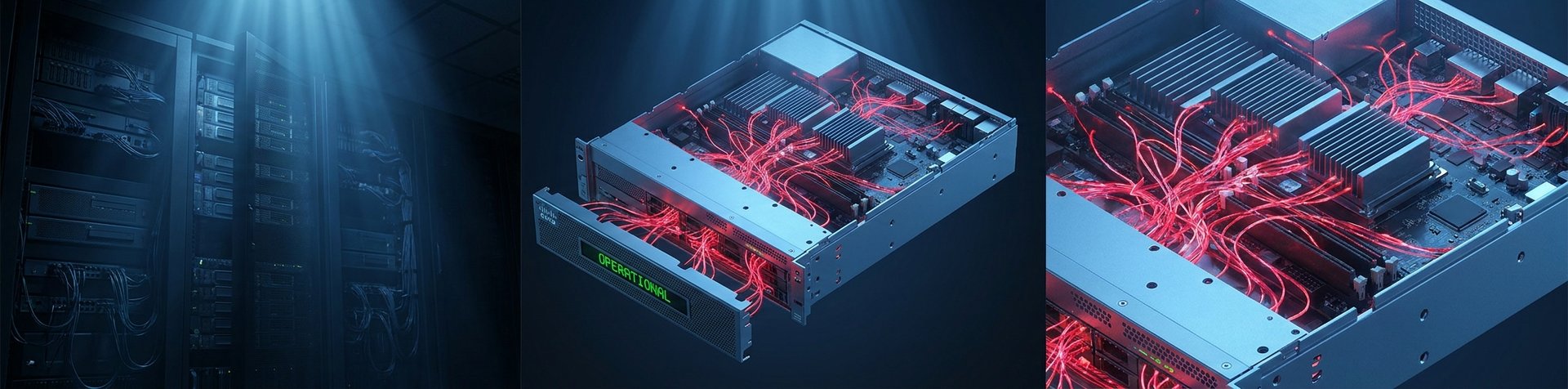
Patch and Pray Failed: FIRESTARTER Proves Cisco Devices Can Stay Owned
A federal agency followed the rules, patched the CVE, and still got owned. FIRESTARTER is a specialized Cisco backdoor designed to survive the remediation cycle. It’s time to stop assuming a patch equals a clean network.
Read More
Akira Ransomware Can Encrypt Your Network in Under an Hour
Akira ransomware completes full attack lifecycles in under an hour, making traditional detect-and-respond strategies basically useless.
Read More
Stryker Finds a Malicious File in Its Systems. Production Is Coming Back Online.
Stryker's forensic investigation with Palo Alto Networks Unit 42 found a malicious file used to run commands and conceal activity, a separate finding from the initial Handala attack. Production recovery is underway.
Read More
M-Trends 2026: The 22-Second Stat Everyone Is Misreading
Mandiant's M-Trends 2026 report is getting misquoted everywhere. The 22-second ransomware handoff is real -- but it's not what you think, and the dwell time stat buried in the report is scarier.
Read More
AI Exploits in Hours: The Patch Window Just Collapsed
Rapid exploitation plus cross-platform AI exposure means next-sprint patching is no longer a safe operating model.
Read More
After Stryker: Why Incident Response Now Starts in the Management Plane
The Stryker fallout, Intune warnings, and leak-site disruption show a hard truth: incident response now lives or dies on control-plane integrity and coordinated external action.
Read More
DarkSword Spread Beyond One Campaign. Mobile Risk Has to Follow.
Google threat intelligence ties DarkSword-linked iOS exploitation to a broader actor picture than earlier reporting suggested. The bigger signal isn't the exploit chain. It's that the capability is spreading across actors and channels.
Read More
Federal Cyber Reality Check: Capacity, Coordination, and Confidence Are Out of Sync
Staffing gaps, fuzzy lead-agency roles, and public messaging that doesn't always match operational uncertainty -- the layers of federal cyber aren't running in sync right now.
Read More
Breach Disclosure Lag Is Becoming the Real Story in Financial Supply Chains
The Marquis breach started with a ransomware attack. The damage is still accumulating months later -- not because of what happened technically, but because of how disclosure was handled.
Read More
The Insider No One Suspected: DOJ Says a Ransomware "Helper" Was Running the Attack
A ransomware negotiator was secretly feeding BlackCat operators confidential victim data to jack up ransom payments. The DOJ just charged him.
Read More
The Ransomware 'Negotiator' Was Running the Attack: DigitalMint's $75M Double Cross
Federal charges reveal DigitalMint's ransomware negotiators were allegedly running the attacks themselves. The second employee charged in the same operation. This wasn't a rogue employee. It was the business model.
Read More