John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
Googling Your VPN Download Just Became a Security Risk
Someone at a company this week searched for their VPN client download. Maybe they got a new laptop. Maybe IT sent a setup guide and they couldn’t find the link. Maybe they just typed it into Google like you type everything into Google.
If they landed on one of Storm-2561’s pages, they got a credential stealer instead.
Microsoft’s security team exposed Storm-2561, a threat actor running SEO poisoning campaigns specifically designed to intercept that exact moment: when an employee searches for legitimate software and downloads whatever shows up first.
How It Works
Search engines rank pages on hundreds of signals. Attackers who understand those signals can push malicious pages toward the top of results for specific queries. No compromised websites needed. No phishing emails. Just beat Google’s ranking algorithm.
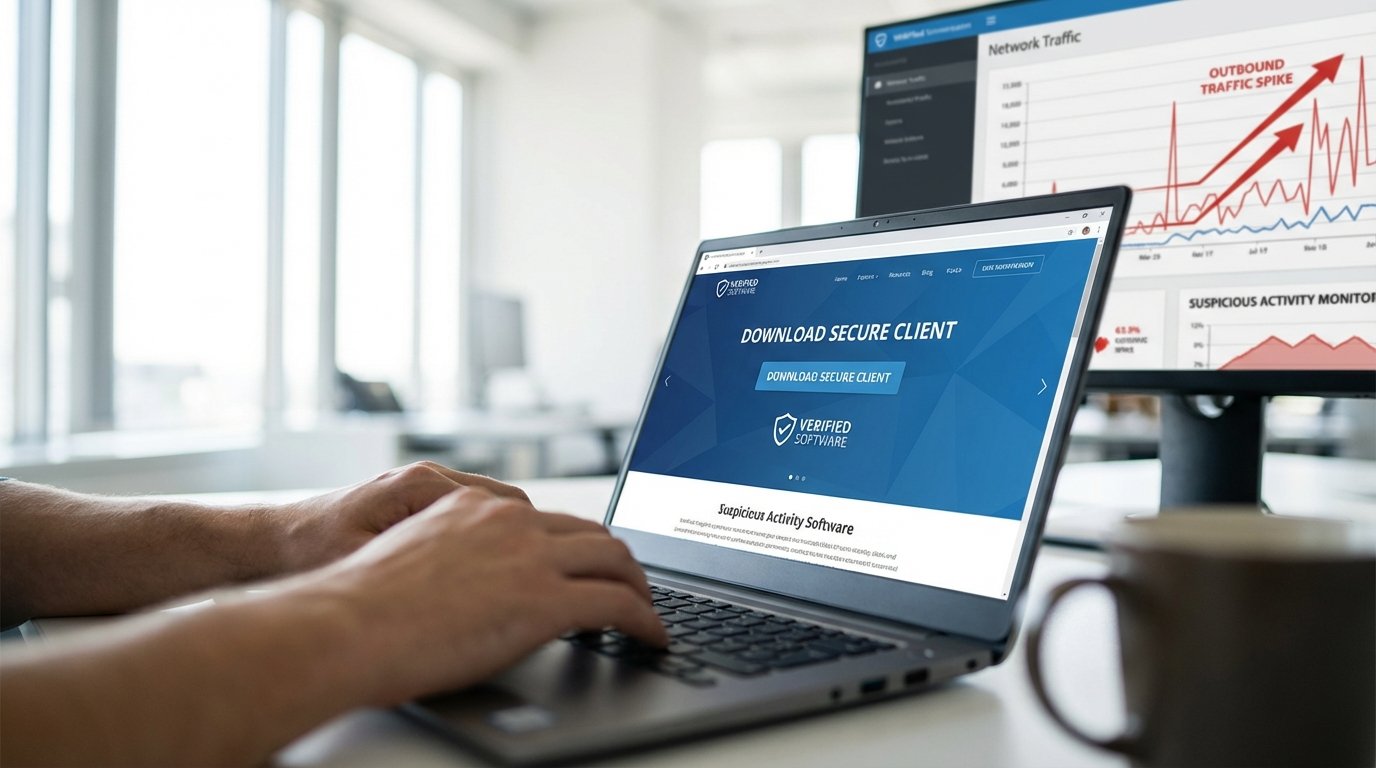
Storm-2561 built pages that look convincingly like legitimate VPN vendor download sites. Same branding. Same layout. Download buttons that produce a real installer. An installer that also installs credential-stealing malware.
The victim experience is seamless. Search, find, download, install. Nothing seems wrong. The malware runs quietly in the background, harvesting credentials from browsers, auth apps, and corporate tools.
Why VPN Clients Specifically
Think about when someone downloads a VPN client. They’re setting up a new device or reconnecting to their employer’s network. They’ve been told by IT to install this software. They’re expecting to download something. Already in a mindset of following setup instructions.
Less suspicious than usual. And VPN clients are high-value targets because of what they do. A credential stealer installed alongside a fake VPN client captures whatever the VPN would’ve used: network credentials, auth tokens, corporate passwords.
No phishing email needed. No suspicious attachment. Just an ordinary search and an ordinary download from the wrong place.
What to Do
The defense here is less technical than behavioral, which makes it both simple and hard.
Stop searching for software downloads. If someone needs a VPN client, IT should provide the direct download link. Not “just Google it.” Especially for anything in the authentication or network access stack.
Set up an enterprise software catalog. For any software employees need to install, provide it through managed deployment or a documented internal page with verified URLs.
Train on this specific risk. Most phishing training focuses on suspicious emails. SEO poisoning doesn’t look suspicious at all. That’s the point.
Verify downloads. Legitimate vendors publish hash values for their installers. Checking takes 30 seconds.
The attack surface increasingly lives in the routine, mundane moments of the workday. Searching for a download barely registers as a decision. Storm-2561 is betting on exactly that.