John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
TeamPCP figured out something clever and genuinely alarming: your security scanner is a better target than your application code.
Trivy is a vulnerability scanner from Aqua Security. KICS is a static analysis tool from Checkmarx. Both are staples of CI/CD pipelines. They run with credentials. They have access to cloud environments and token stores. That’s the point of them.
TeamPCP hijacked GitHub Actions tags for both tools – 75 Trivy tags, 35 KICS tags. When your pipeline pulled those tags, it ran TeamPCP’s modified version. The malware, called CanisterWorm, harvested credentials and tokens sitting in those CI/CD environments. Azure environments accounted for 61% of compromised servers; AWS, 36%.
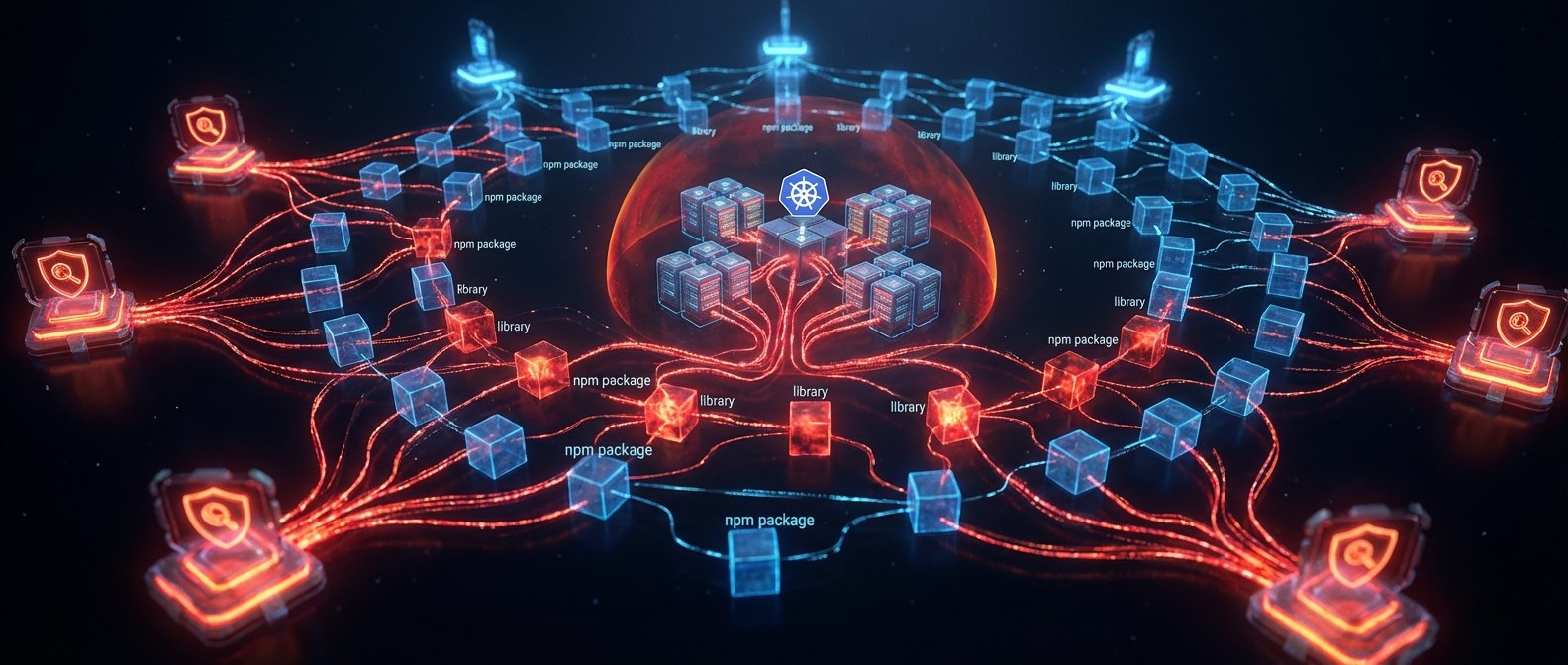
With stolen npm tokens in hand, CanisterWorm published to npm. 47 packages total across the @EmilGroup and @opengov scopes. Supply chain attack layered on top of supply chain attack. Any project pulling from those scopes got infected.
Then it gets genuinely new.
TeamPCP’s command-and-control infrastructure runs on an Internet Computer Protocol blockchain canister. According to researchers, this is the first time this technique has been observed in an active campaign. There’s no central server to take down. No domain to sinkhole. No IP to block. The C2 lives on a decentralized network. The standard takedown playbook doesn’t apply here. That’s a meaningful escalation in attacker resilience, and you should expect other groups to copy it.
And then there’s the payload that makes this geopolitically interesting: CanisterWorm checks the timezone of the infected system. If it detects an Iranian timezone, it destroys every Kubernetes node on that cluster. Not ransomware. Not exfiltration. Destruction. A financially motivated cybercrime group with a geopolitically targeted wiper built into its toolset is unusual. The explanation for that combination is still unclear.
If you use Trivy or KICS in your pipelines, check now. Pin to commit SHAs, not tags. Rotate any credentials that were accessible during the affected window. Check your npm dependencies for @EmilGroup and @opengov packages. And verify directly with Aqua Security and Checkmarx for official guidance – research on this campaign is still evolving.