John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
The Trivy Domino: How One Poisoned Security Tool Spread to a Thousand Cloud Environments
A poisoned Trivy Docker image grew into one of the year's worst CI/CD compromises. Thousands of pipelines ran the payload, LiteLLM got backdoored on PyPI, and the attackers built a three-part kit designed to hit Kubernetes clusters and stay.
Read More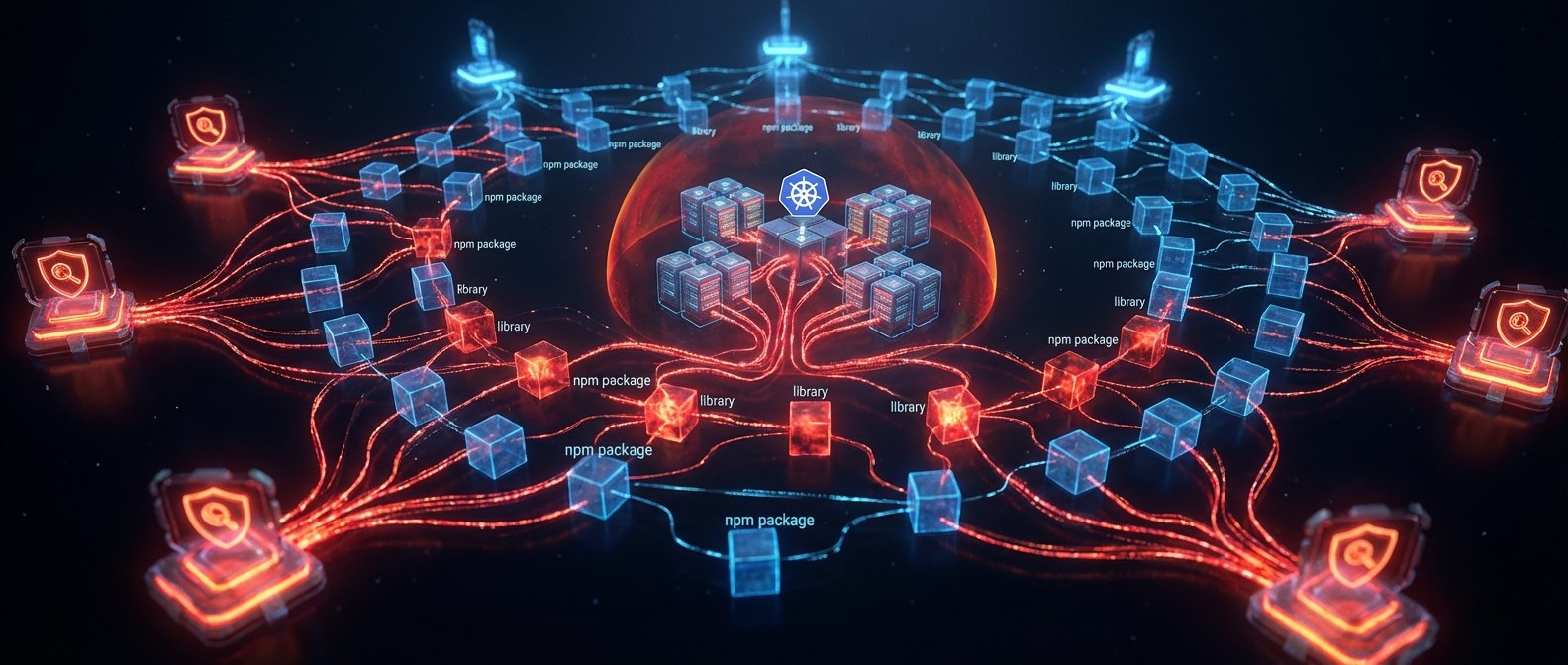
CanisterWorm: How TeamPCP Hijacked Your Security Scanners and Built an Untakeable Botnet
TeamPCP compromised Trivy and KICS CI/CD scanner tags, spread CanisterWorm to 47 npm packages, and deployed a Kubernetes wiper targeting Iranian timezones -- all controlled via blockchain C2 that can't be taken down.
Read More
The Toolchain Turned Hostile: Trivy and Langflow Show Security Pipeline Fragility
A compromised Trivy vulnerability scanner and an AI pipeline builder exploited within 20 hours of disclosure reveal a deepening problem: the tools developers trust for security are becoming high-value attack targets.
Read More
Trivy Incident Reality Check: Your Security Tool Can Become Your Attack Path
The Trivy incident is a blunt reminder that CI security tools need the same zero-trust controls as production systems.
Read More