John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
A few days ago, TeamPCP looked like a threat group getting bolder. Supply chain attack here, blockchain-based wiper there. Related incidents. An evolving toolkit.
That framing is already out of date.
What’s become clear is that we weren’t watching a group run campaigns. We were watching a criminal platform finish building itself.
The Trivy attack in March established supply chain reach inside developer infrastructure – not for immediate profit, but for access. Then came the Telnyx PyPI incident: a malicious SDK pushed to PyPI with malware hidden inside WAV audio files using steganography. Not because it’s easy – it’s harder than hiding code in a Python file. They did it specifically because scanners inspect scripts, not audio files. That’s evasion built on research into what defenders actually look at.
Then CanisterWorm landed, and the infrastructure problem got real.
CanisterWorm routes its command-and-control through Internet Computer Protocol (ICP) blockchain canisters. Traditional C2 gets taken down through domain seizures and BGP null-routing – law enforcement calls registrars, hosting providers, ISPs. That entire playbook doesn’t apply here. ICP canisters don’t live on any domain. They’re not routed through any ISP that can be pressured. They exist on the blockchain and stay online as long as the operator pays fees. You can’t seize them.
One note: as of March 22, the canister was returning a benign redirect rather than a payload – the attacker likely detected researcher attention and held back. The worm’s propagation and credential theft were still active. If your organization had npm tokens exposed in CI/CD environments between March 19 and March 21, treat them as compromised and rotate them now.
The monetization piece is Vect: a ransomware-as-a-service program now actively recruiting affiliates. Written in C++, ChaCha20-Poly1305 encryption, runs in SafeMode to dodge behavioral detection. Targets Windows, Linux, and VMware ESXi – built for enterprise environments. Affiliate entry fee is $250, waived for operators from CIS countries. First confirmed victims are in Brazil and South Africa.
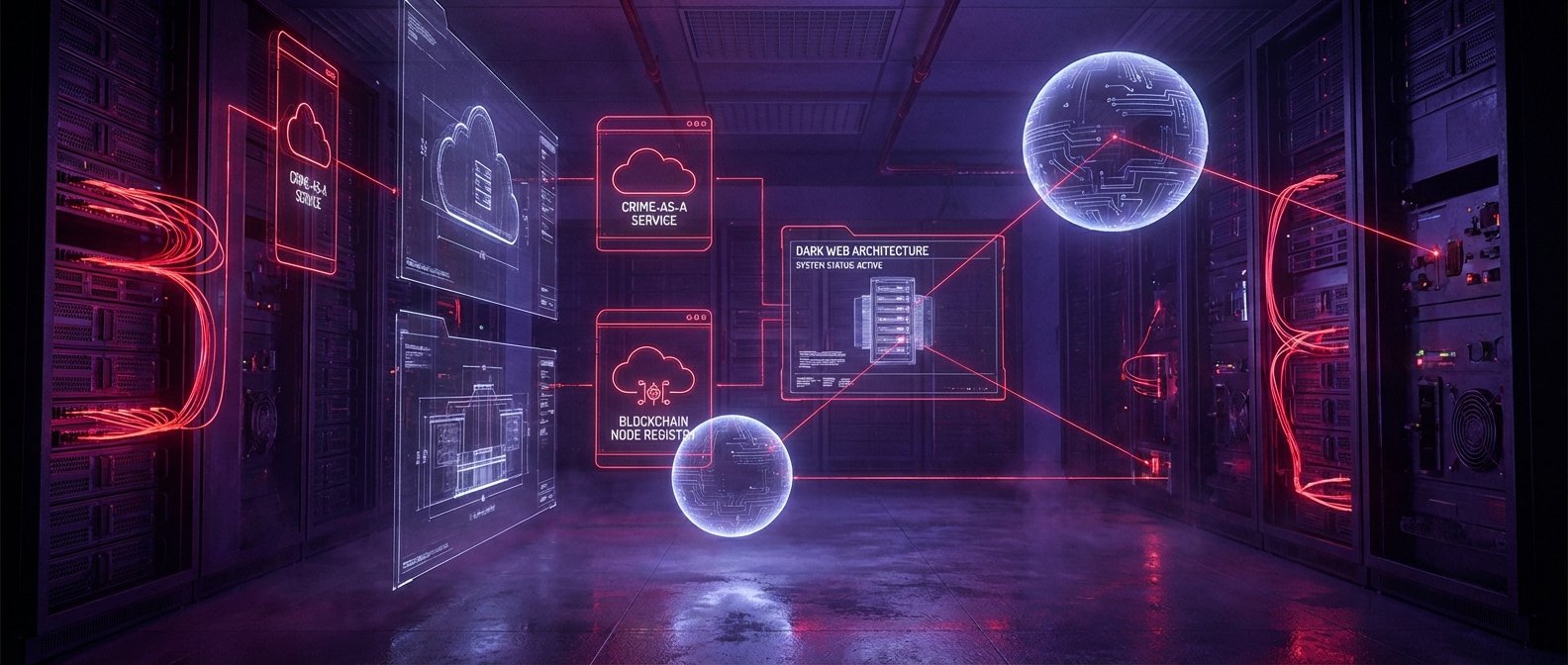
Supply chain access. Steganographic evasion. Unseizable infrastructure. Scalable ransomware. Every piece serves the others. Flare analysts are calling it a “cloud-native exploitation platform,” and that holds up.
This isn’t a group anymore. It’s a platform. And platforms are a lot harder to shut down than groups.