John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
Patch and Pray Failed: FIRESTARTER Proves Cisco Devices Can Stay Owned
A federal agency followed the rules, patched the CVE, and still got owned. FIRESTARTER is a specialized Cisco backdoor designed to survive the remediation cycle. It’s time to stop assuming a patch equals a clean network.
Read More
The Ephemeral Illusion: Why the Cloud Sandbox is not a Safe Zone
We have been told that serverless environments are secure because they are temporary. New research on Azure and AWS Lambda proves that attackers are learning how to live in the layer underneath.
Read More
Researchers Turned a Fiber Optic Cable Into a Listening Device. Your RF Scanner Won't Find It.
New research from NDSS 2026 demonstrates that standard fiber optic cables can reconstruct conversations in adjacent rooms using off-the-shelf commercial equipment. No network access. No credentials. No software. And it bypasses both RF scanners and ultrasonic jammers, the two most common counter-surveillance tools.
Read More
CISA Has Already Assessed Almost Every World Cup Stadium. The Cyber Defense Operation Is Running.
CISA has completed cybersecurity assessments at nearly every World Cup 2026 stadium and team base camp. A White House task force is operational. The Milan Winter Olympics just gave the whole framework a live stress test with real Russian-linked attacks. This isn't a plan anymore.
Read More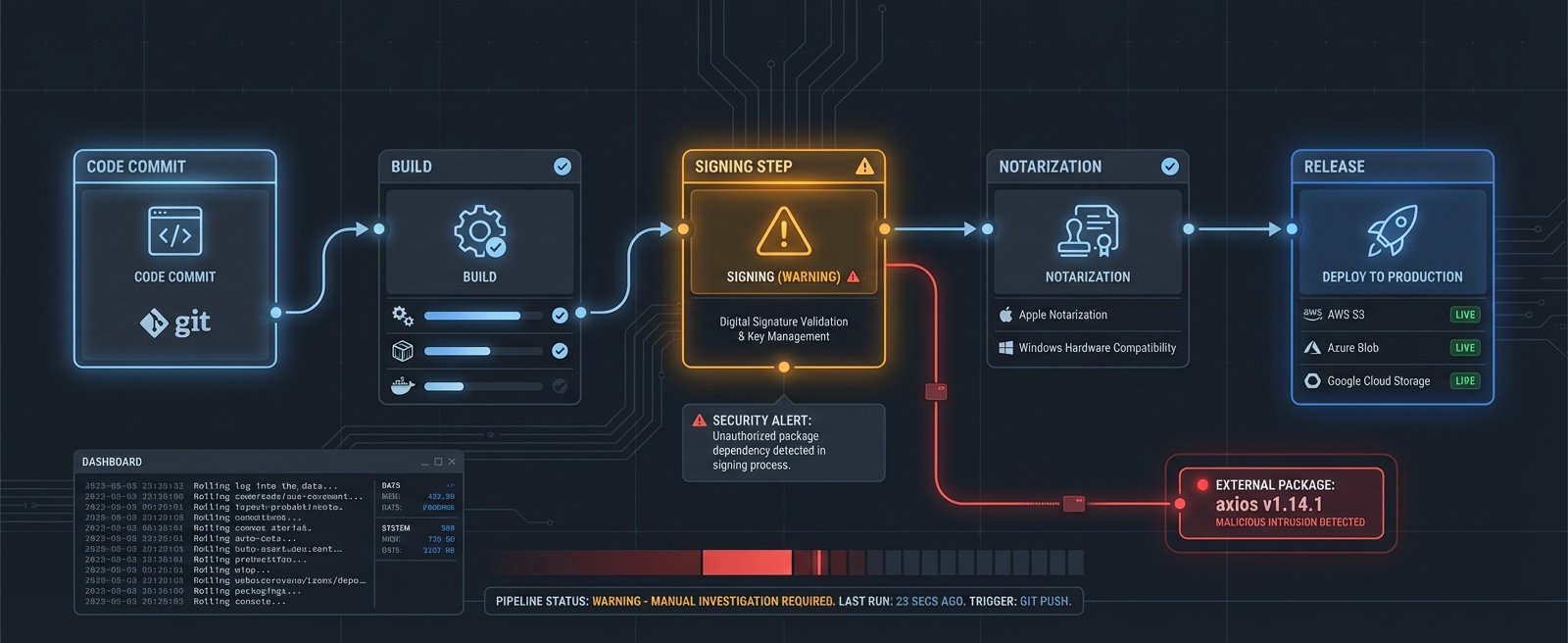
OpenAI Rotated Its macOS Signing Certs After the Axios Attack. No Proof of Key Theft. They Rotated Anyway.
A malicious Axios npm package executed inside OpenAI's GitHub Actions signing workflow. Their investigation found no evidence keys were stolen. They revoked and rotated the certificates anyway. That decision is the interesting part.
Read More
The Math Does Not Work Anymore: Why Patching Faster Is No Longer Enough
Qualys analyzed a billion CISA KEV remediation records and found attackers are weaponizing critical vulns an average of seven days before patches exist. The human-scale remediation model has hit a structural ceiling.
Read More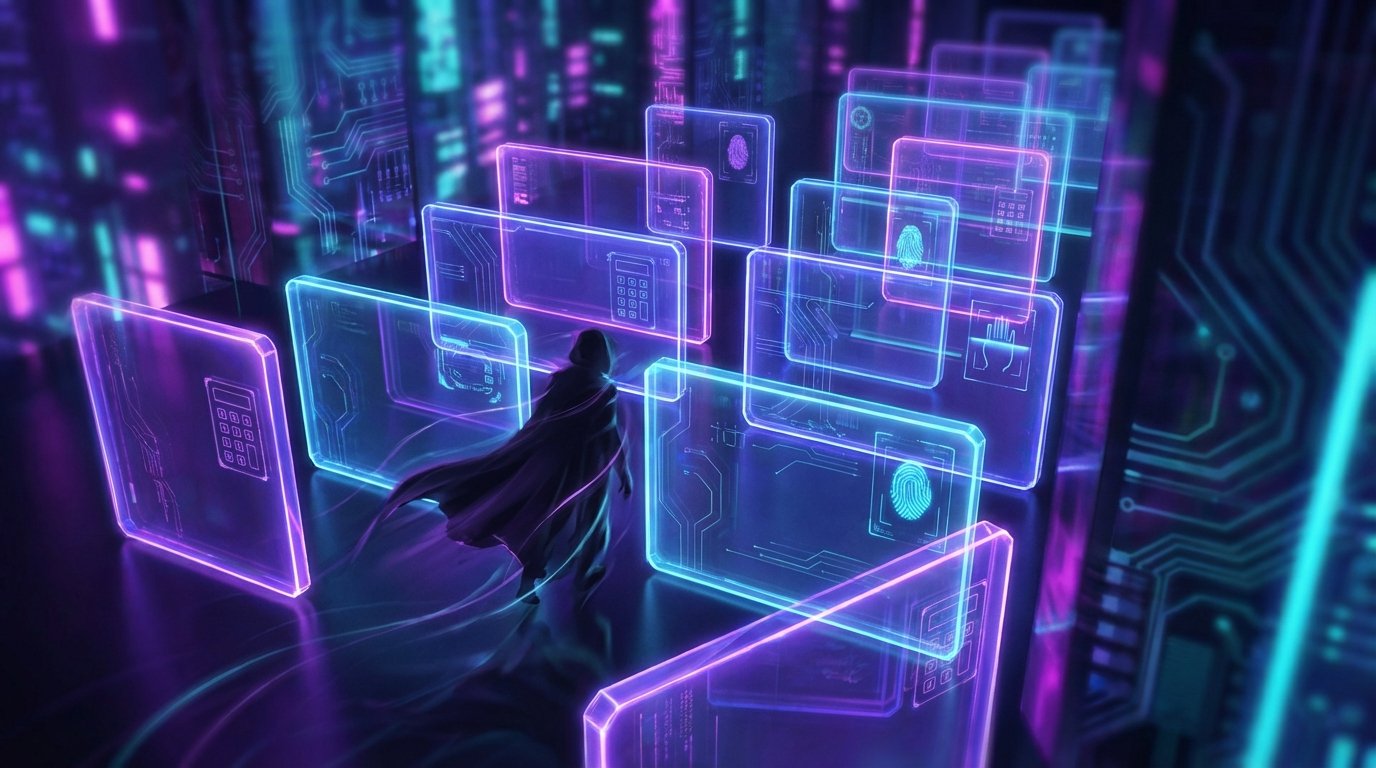
MFA Isn't the Final Barrier Anymore. It Hasn't Been for a While.
Three research teams this week documented MFA failures at login, at the helpdesk layer, and post-session. The answer isn't more MFA. It's hardware-bound authentication.
Read More
Google Says You Have Until 2029 to Get Ready for Post-Quantum Encryption. That's Three Years.
Google moves its internal post-quantum cryptography deadline to 2029, signaling that everyone else should already be planning.
Read More
CrowdStrike and Microsoft Are Sharing Data Now. Yes, Really.
CrowdStrike's Falcon SIEM can now ingest Microsoft Defender telemetry, and Formula 1 is somehow responsible.
Read More
RSAC 2026: AI Dominated, Washington Bailed, and Facial Recognition Got Wrecked on Stage
RSAC 2026's biggest story was who didn't show up. CISA, FBI, and NSA all pulled out. Meanwhile, AI was everywhere, a researcher beat facial recognition live, and OpenAI launched a $100K bug bounty.
Read More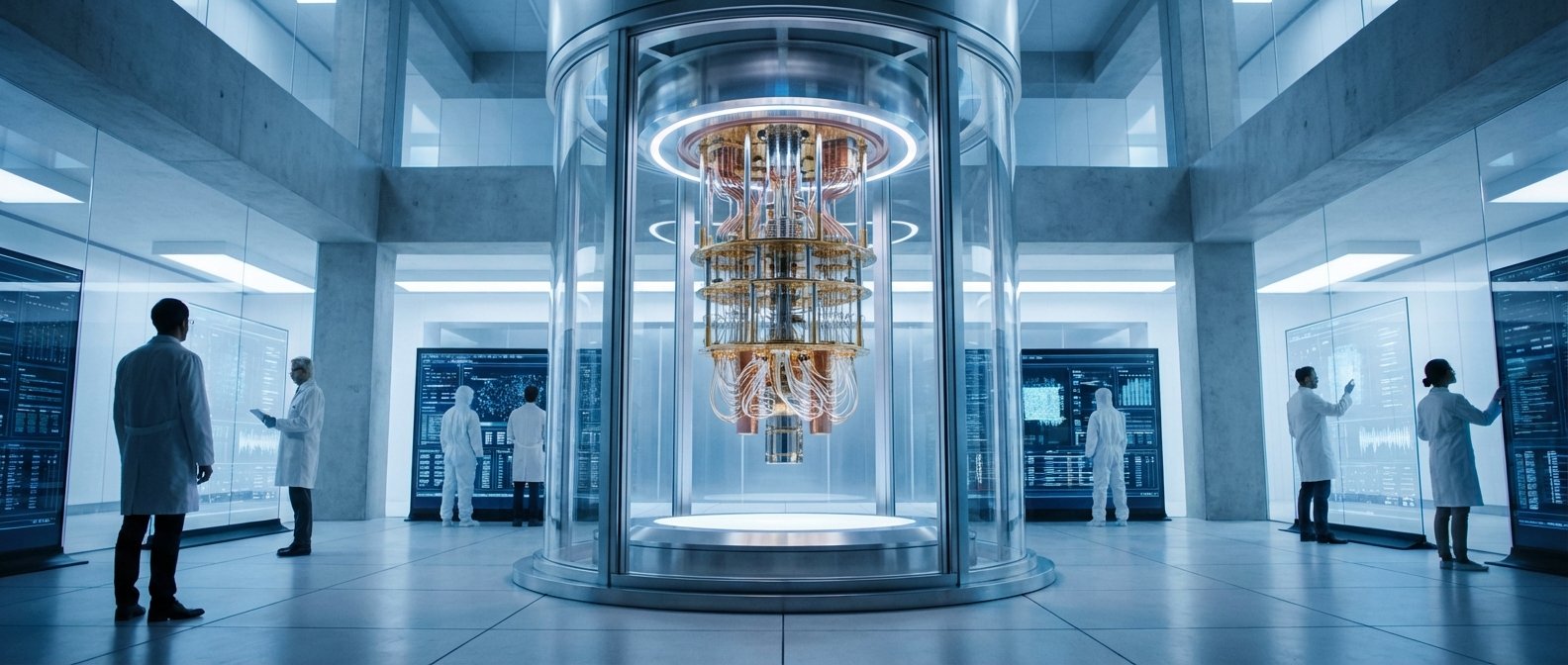
Google Says Q Day Is 2029. Three Billion Android Devices Are Already Changing.
Google moved its internal Q Day deadline to 2029. Android 17 is already being rebuilt around post-quantum standards. If you're waiting on this, you're already late.
Read More
M-Trends 2026: The 22-Second Stat Everyone Is Misreading
Mandiant's M-Trends 2026 report is getting misquoted everywhere. The 22-second ransomware handoff is real -- but it's not what you think, and the dwell time stat buried in the report is scarier.
Read More
RSAC 2026 Opens Monday: Here's What the Cybersecurity Industry Will Be Talking About All Week
RSAC 2026 opens Monday at Moscone Center. Agentic AI, human manipulation, and post-breach resilience are the dominant themes -- here's what to watch and why this year feels different.
Read More
Security Below the OS: Why Device Integrity Is Becoming a Boardroom Topic
Eclypsium raised $25M for firmware security. A compromised security scanner and ongoing IoT campaigns add context. Enterprise security that stops at the OS is leaving a meaningful gap below it.
Read More
Trivy Incident Reality Check: Your Security Tool Can Become Your Attack Path
The Trivy incident is a blunt reminder that CI security tools need the same zero-trust controls as production systems.
Read More
Security Funding Is Getting Specific, and That Is the Signal
Capital is clustering around persistent pain points like cellular risk, device trust, and brand abuse, which is useful planning intelligence.
Read More
After Stryker: Why Incident Response Now Starts in the Management Plane
The Stryker fallout, Intune warnings, and leak-site disruption show a hard truth: incident response now lives or dies on control-plane integrity and coordinated external action.
Read More
Robots Are Moving Into Sensitive Environments. Security Gets Decided at Procurement.
U.S. robotics firms are pushing Congress for procurement barriers against Chinese suppliers. Robot dogs are already patrolling data centers. The security posture is decided before install day, during sourcing and contract language.
Read More
The Next Enterprise Exposure Wave: Old Management Surfaces, New Root Paths
An unpatched telnetd with unauthenticated root RCE. Nine critical IP-KVM flaws. A Linux privilege escalation tied to systemd timing. Different CVEs, same underlying problem: forgotten management plumbing.
Read More