John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com

When the Breach Isn't at Your Bank: Third-Party Risk Hits Healthcare and Finance in the Same Week
A hospital email account, a fintech ransomware attack still sending notifications eight months later, and a Lapsus$ claim against a financial vendor. Third-party concentration risk landed in two sectors at once this week.
Read More
Two Breaches Today. One Was Careful. One Was a Unlocked Door. Both Were Catastrophic.
ShinyHunters dumped 78.6 million Rockstar records after the ransom deadline expired. They never touched Rockstar directly. They went through a cloud analytics vendor. Meanwhile, a French email provider left an Elasticsearch cluster open to the internet and exposed 40 million records across L'Oreal, Renault, and French government embassies.
Read More
The LAPD Was Not Hacked. But 7.7 Terabytes of Its Data Leaked Anyway.
World Leaks didn't touch LAPD's network. They breached a third-party file-sharing app connected to the LA City Attorney's Office that apparently had no password protecting it. 337,000 files including Internal Affairs records and witness names are now in an extortion group's hands.
Read More
Healthcare Had a Bad Week. A Really, Really Bad Week.
Three healthcare breaches in one week, all tracing back to the same problem: third-party vendors with access to patient data and not enough security around it.
Read More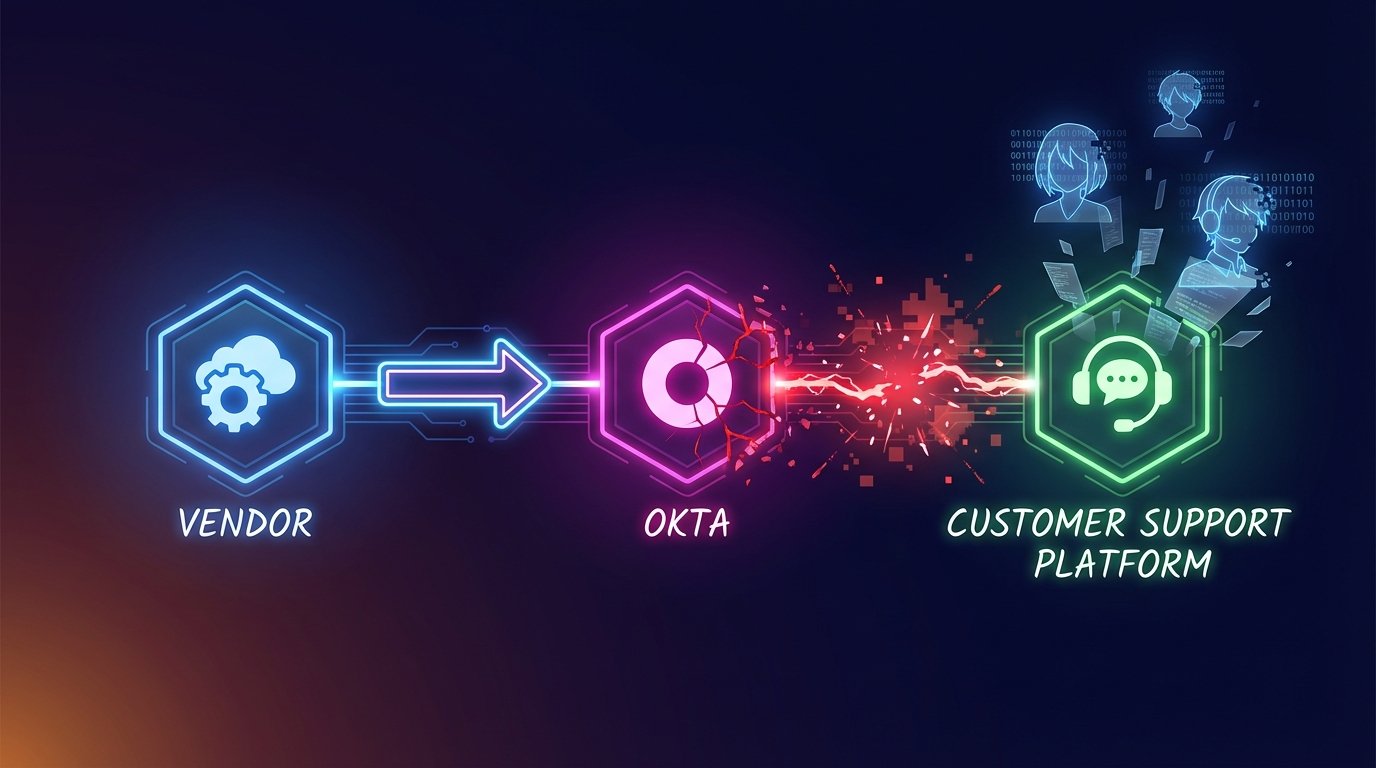
Crunchyroll Got Breached. Their Systems Were Never Touched.
6.8 million Crunchyroll users had their data stolen through a three-hop attack chain that went from a vendor's infected laptop through Okta into Crunchyroll's customer service platform, without ever touching Crunchyroll's own systems.
Read More
AI Export Controls Are Now a SOC Problem, Not Just a Legal Memo
New enforcement activity pushes export-control risk into day-to-day security operations, especially around access, logging, and partner workflows.
Read More
Breach Disclosure Lag Is Becoming the Real Story in Financial Supply Chains
The Marquis breach started with a ransomware attack. The damage is still accumulating months later -- not because of what happened technically, but because of how disclosure was handled.
Read More