John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
Mostly security stuff...
Make sure you check out my main blog at https://gnerdsec.com/blog
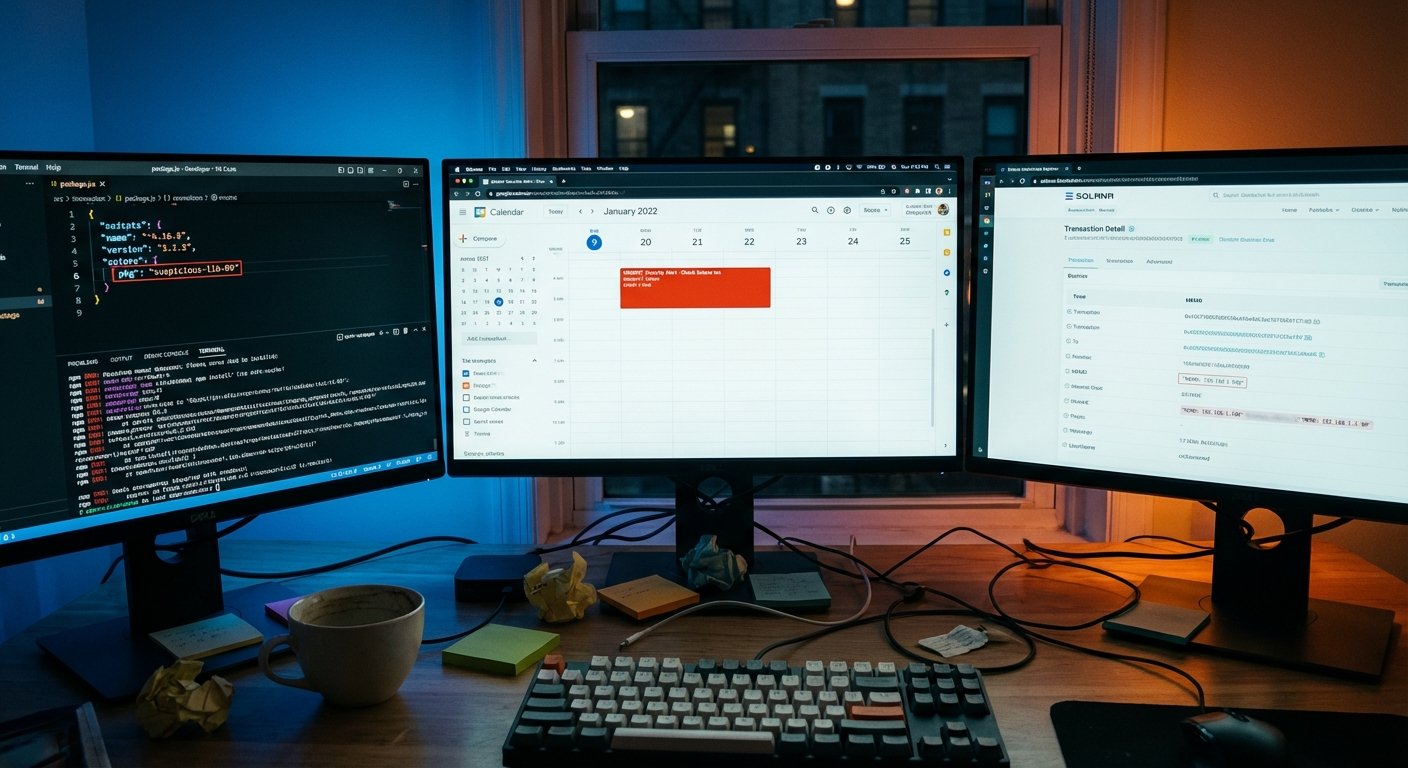
This Malware Hides Its Command Server in the Blockchain, and Borrows Google Calendar Too
GlassWorm targets developers through compromised npm, PyPI, and GitHub packages. Its C2 address is hidden in a Solana blockchain memo. You can't take down a blockchain transaction.
Read More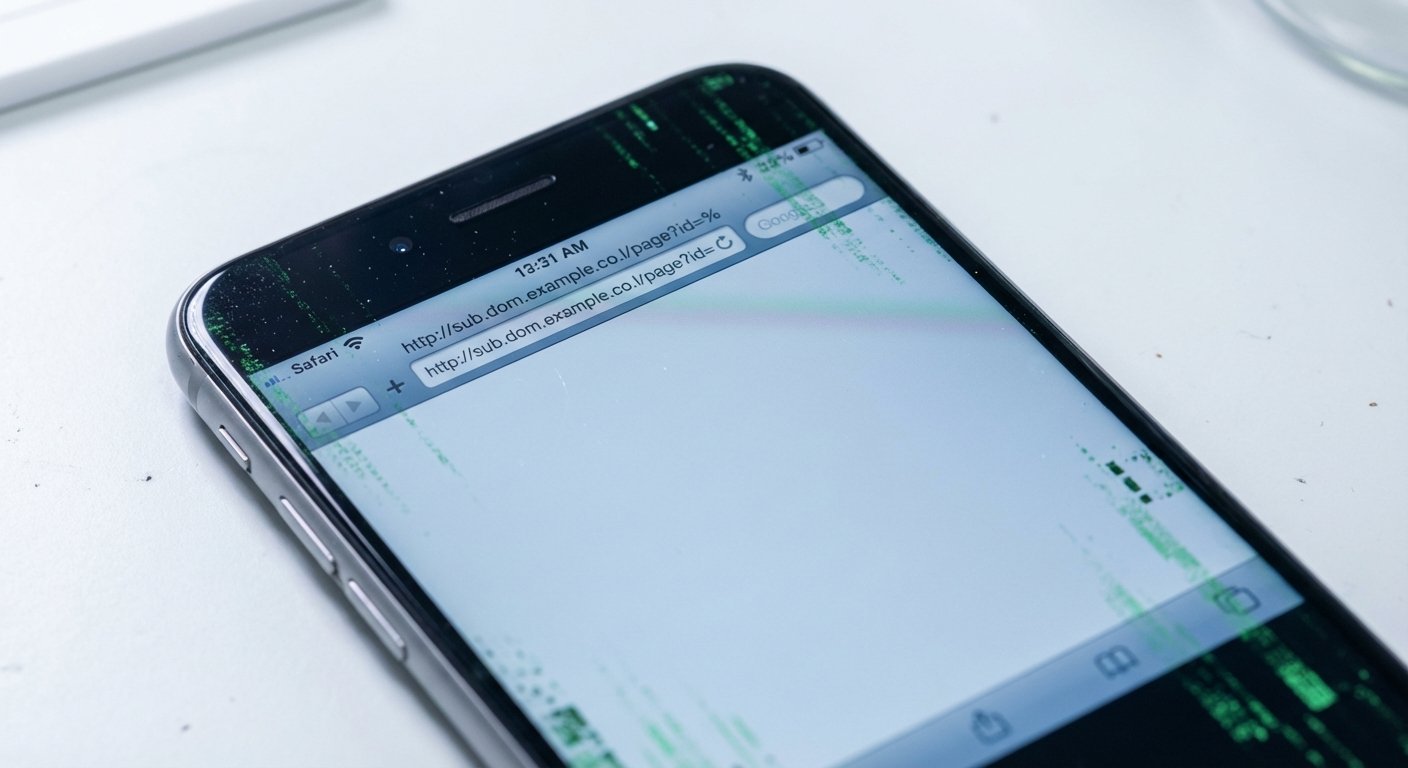
The iPhone Exploit That Won't Die: Operation Triangulation's Code Is Back and More Dangerous
Exploit code from the 2023 Operation Triangulation campaign lives inside Coruna, a new iOS attack framework hitting modern iPhones in mass attacks. Elite nation-state code is now being aimed at everyone.
Read More
America's Cyber Watchdog Is Walking Out the Door. The UK's Is Calling for a Full Court Press.
CISA is bleeding staff through its third government shutdown, with 1,000 vacancies and 60% of its workforce sidelined. Across the Atlantic, the UK's NCSC chief is demanding coordinated escalation against the same threats.
Read More
China Is Running Three Cyber Operations Against the West Simultaneously. Here's What They Look Like.
BPFDoor sleeping inside telecom networks, US officials blaming Beijing for enabling billion-dollar fraud, and a $20B Telegram black market just sanctioned by the UK. Three fronts, one picture.
Read More
Regulators on Both Sides of the Atlantic Are Forcing Platforms to Verify Who's Online
Apple rolled out mandatory age verification for all UK iPhone users. The EU opened a formal DSA investigation into Snapchat. The era of anonymous sign-ups is ending, and it's moving faster than most platforms planned.
Read More
AI Tools Are Now Both the Target and the Weapon, And Security Teams Haven't Caught Up
A CVSS 10.0 flaw in Langflow was exploited within 20 hours. The Claude Chrome extension let any website hijack your AI assistant. And a state-sponsored actor used autonomous AI to run 80-90% of a cyber espionage campaign. Three stories, one picture.
Read More