John Z Black
Brunswick, ME • (207) 245-1010 • contact@johnzblack.com
Mostly security stuff...
Make sure you check out my main blog at https://gnerdsec.com/blog

The Lock Is Broken: Critical Auth Bypasses Hit Cisco, GitHub, and Palo Alto
Four critical authentication bypasses dropped this week across Cisco SD-WAN, GitHub Enterprise, Palo Alto PAN-OS, and Zabbix. This isn't a credential problem. The authentication systems themselves are failing.
Read More
The Mythos Breach: Your AI Is Only as Secure as Its Weakest Integration
Unauthorized access to Anthropic's Mythos model via a compromised OAuth app exposes the real security threat in the agentic AI era: third-party integrations that inherit trust they haven't earned.
Read More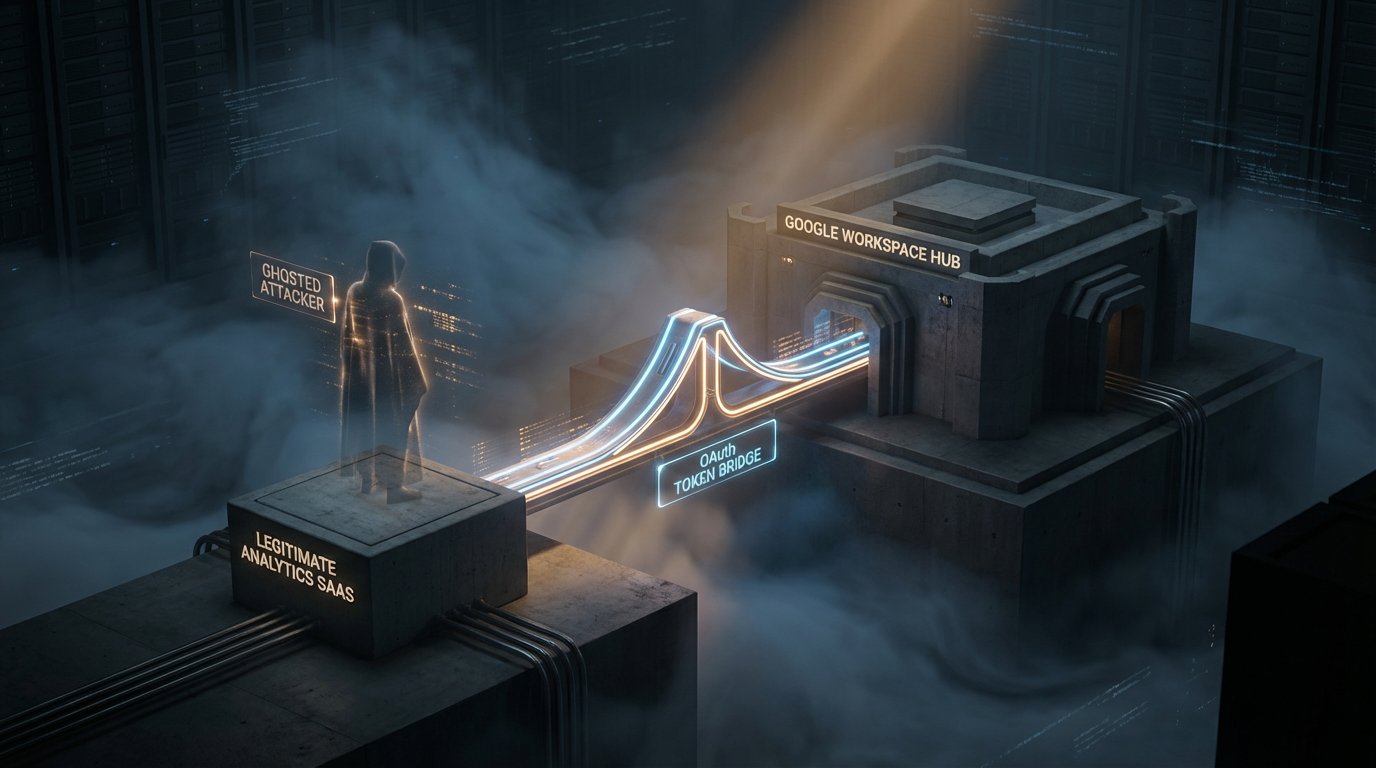
The 22-Month Window: How Vercel's Upstream Analytics Bridge Was Compromised
Vercel recently disclosed a major security incident via Context.ai that began in June 2024. For nearly two years, an invisible door was held open into the core of their cloud identity. It is a masterclass in the hidden risks of 'harmless' SaaS analytics.
Read More
The Megaleak Stage: Why the Standard Bank Breach is 2026's Scariest Proof-of-Failure
Standard Bank South Africa's breach just hit the 154-million-row stage. This is no longer an investigation. It is a permanent intelligence library for identity thieves. When negotiations fail, the consumer picks up the bill.
Read More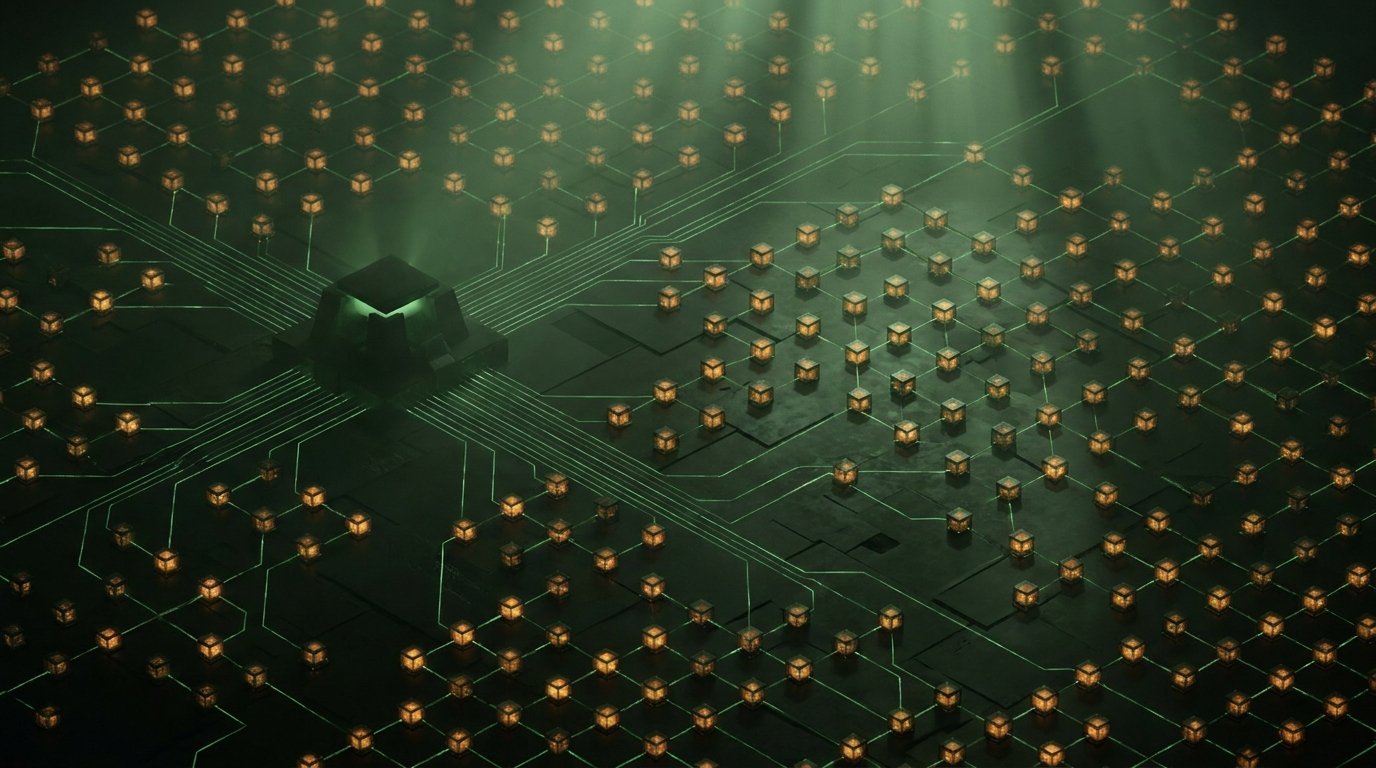
Machine-Speed Dwell Time: The Bot-Powered Recon of 'The Gentlemen'
A massive 1,570-host botnet linked to The Gentlemen ransomware has been unburied. These attackers are using automated proxy infrastructure to scout corporate networks before you even know they are there. Dwell time just got industrialized.
Read More
The 2-Minute Defeat: Why the EU's Child Safety App is a Case Study in Security Theater
The EU's high-profile age verification app was cracked in under two minutes by a security consultant. It turns out storing sensitive tokens in an unencrypted local text file is not 'Safe by Design.' Here is what happens when PR outpaces engineering.
Read More